Security management method and system for smart card chip operating system files
A smart card chip, operating system technology, applied in transmission systems, digital transmission systems, secure communication devices, etc., to achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below through specific embodiments in conjunction with the accompanying drawings. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
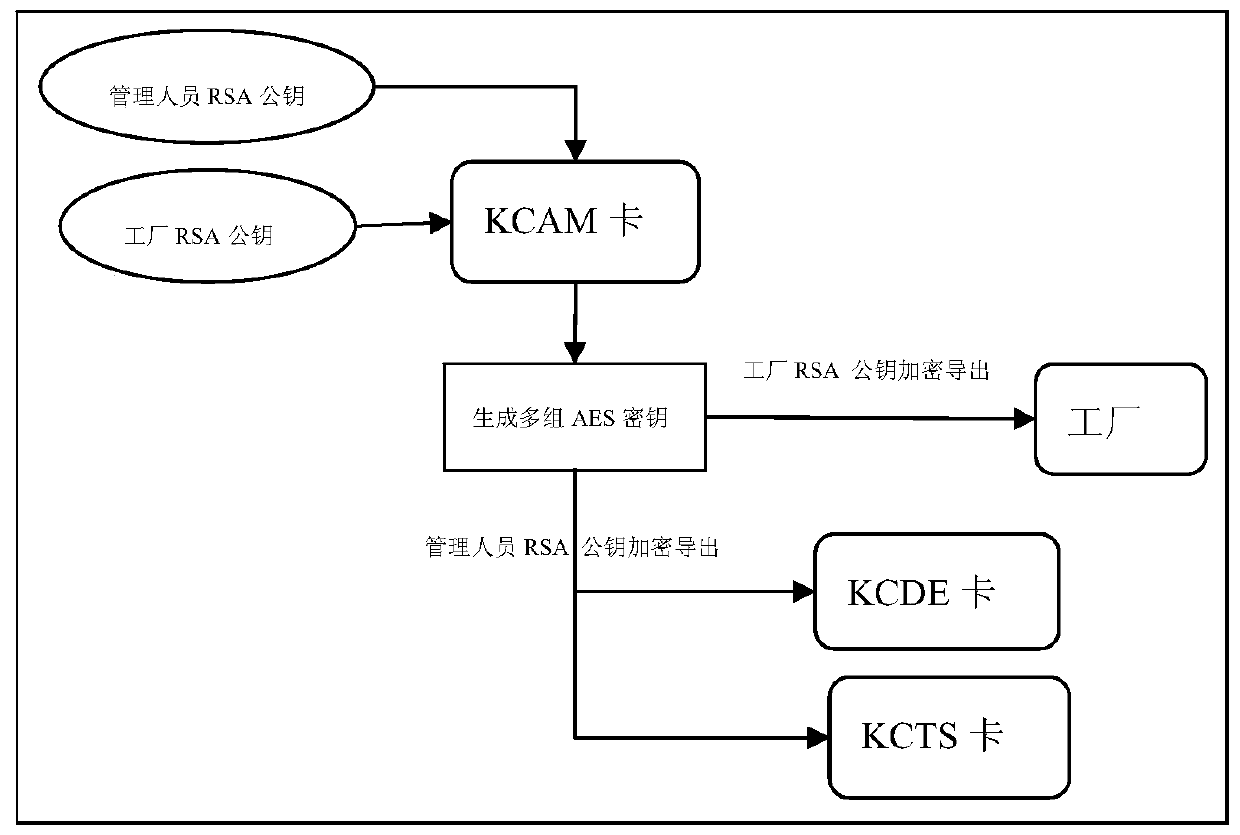
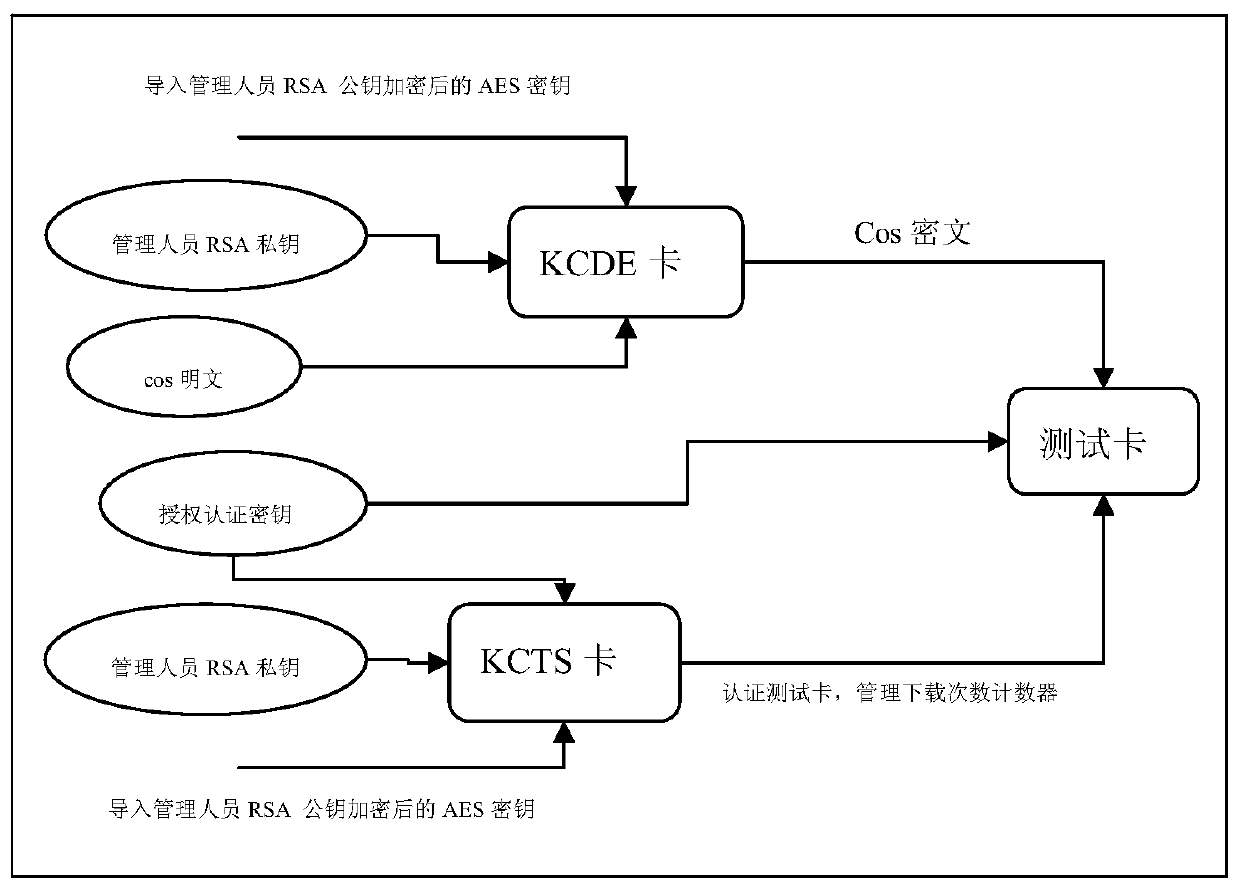
[0031] For the convenience of description, AES stands for symmetric key algorithm and RSA stands for asymmetric encryption algorithm as examples for description below, but this is not limited thereto. It should be understood that other symmetric encryption methods such as DES, 3DES and asymmetric encryption methods such as Elgamal, Rabin may also be used.
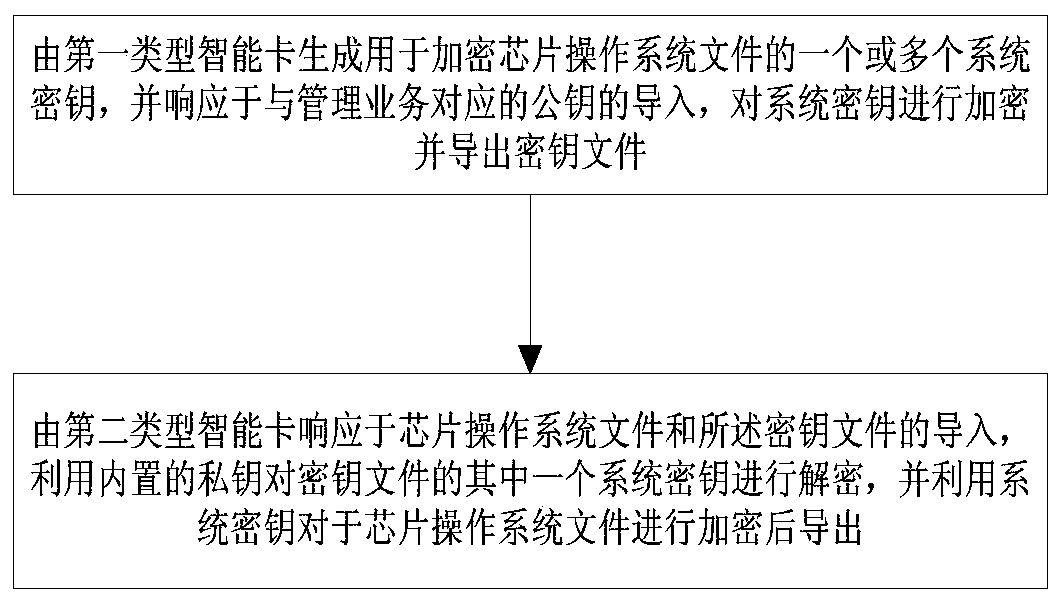
[0032] The smart card COS file mainly involves three links in the process of development, testing and production: 1) In the development environment, COS developers can use a symmetric encryption algorithm such as the advanced encryp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More