Application control-based anti-virus attack realization method and system
A technology of application programs and implementation methods, applied in the fields of instruments, electrical digital data processing, platform integrity maintenance, etc., can solve the problems of computer system security damage, application programs are vulnerable to attacks, tampered or terminated, etc., to ensure safe operation. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0049] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
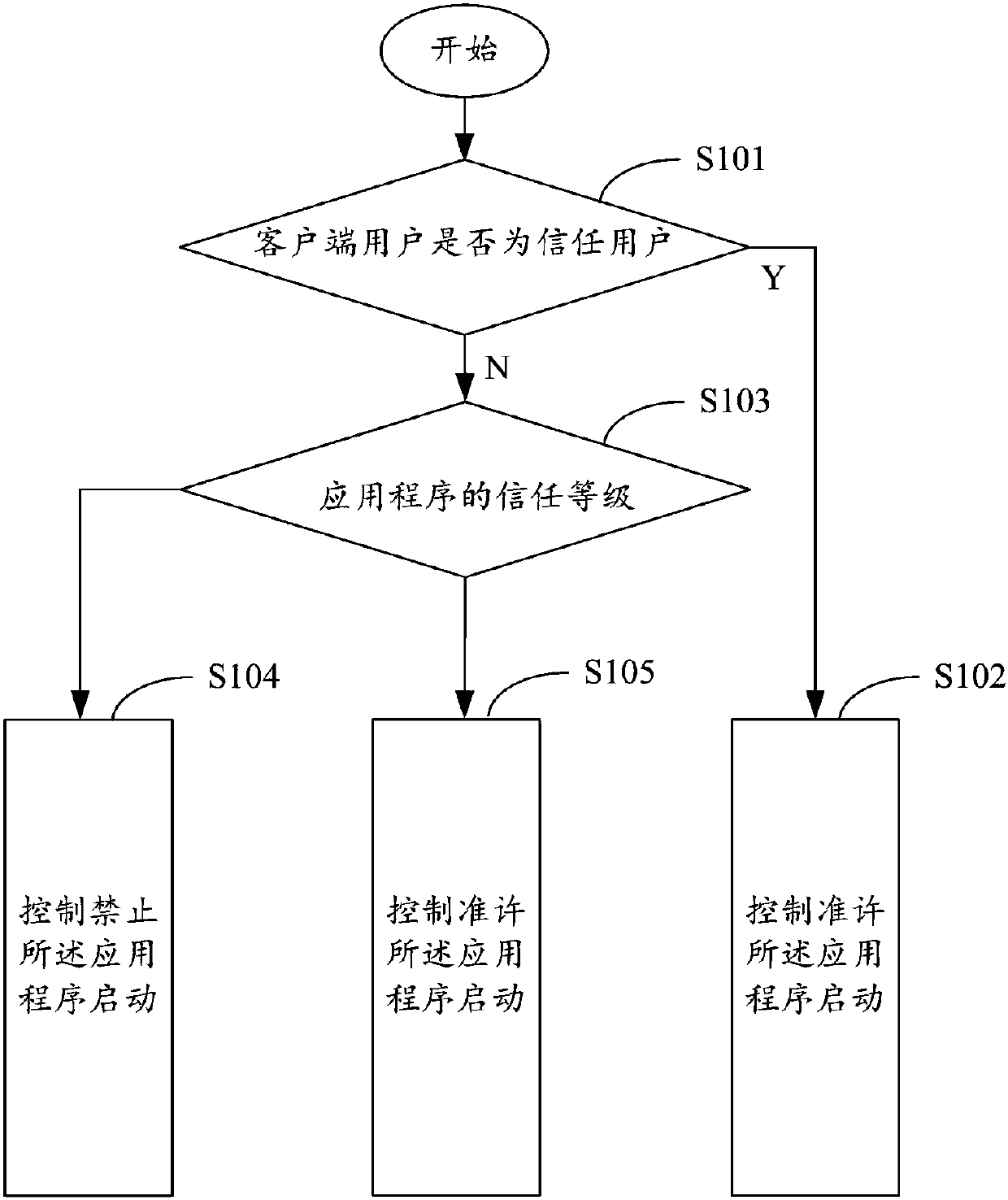
[0050] figure 1 It shows the implementation flow chart of the anti-virus attack implementation method based on application program management and control provided by the present invention, which specifically includes the following steps:
[0051] In step S101, when it is detected that the application is started, it is judged whether the client user is a trusted user, if it is a trusted user, then step S102 is executed, otherwise, step S103 is executed.
[0052] In step S102, when the client user is a trusted user, the control allows the application program to start.
[0053] In step S103, when...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More