Malicious link detection method and system
A malicious link and detection method technology, applied in the computer field, can solve problems such as waste of system resources and low detection efficiency, and achieve the effect of saving system resources and high detection efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] The principles and features of the present invention are described below in conjunction with the accompanying drawings, and the examples given are only used to explain the present invention, and are not intended to limit the scope of the present invention.
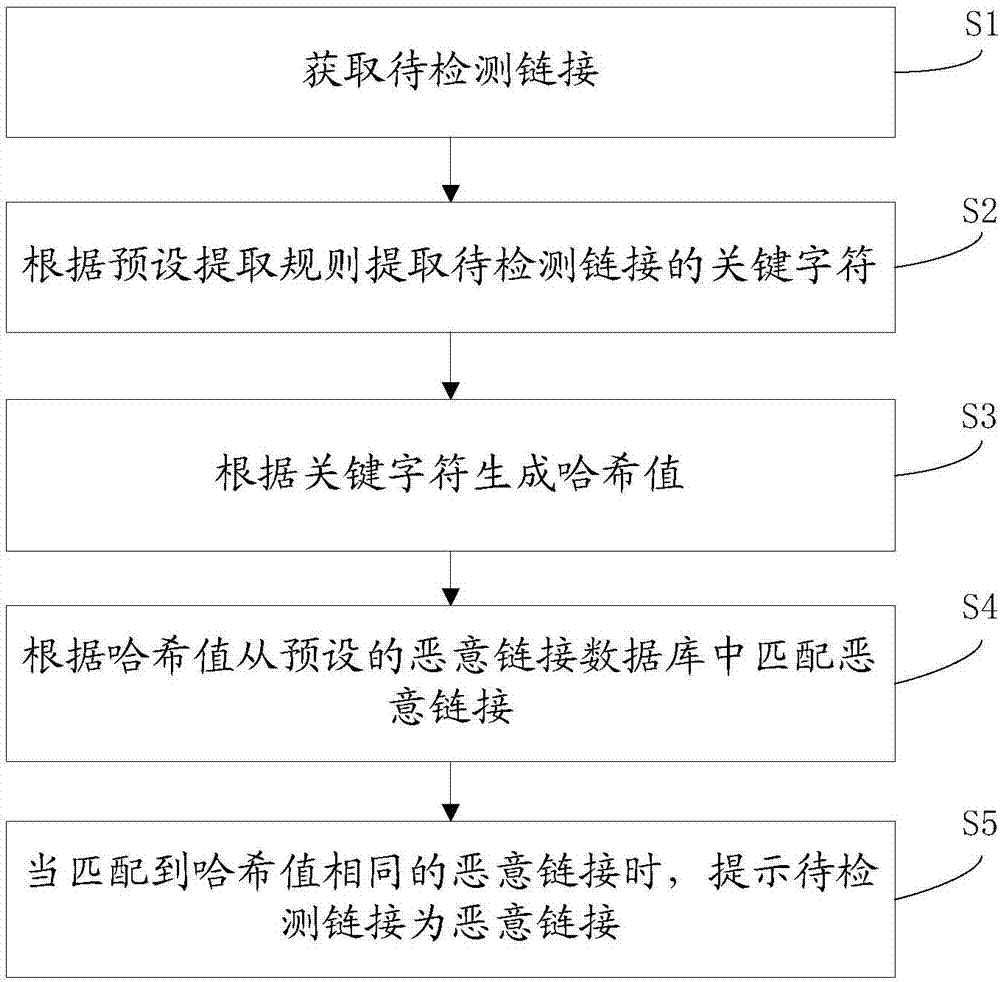
[0038] Such as figure 1 As shown, it is a schematic flowchart of a malicious link detection method provided by an embodiment of the present invention, the method includes:
[0039] S1. Obtain a link to be detected.
[0040] S2, extract key characters of links to be detected according to preset extraction rules.
[0041] S3, generate a hash value based on key characters.
[0042] S4, matching the malicious link from the preset malicious link database according to the hash value.
[0043] S5, when a malicious link with the same hash value is matched, prompting that the link to be detected is a malicious link.
[0044] Preferably, it also includes:
[0045] When no malicious link with the same hash value is matche...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More