An access control system, an access control robot and an operating method of the system
An operation method and robot system technology, applied in the direction of instruments, time registers, single input port/output port registers, etc., can solve the problems of high cost, low security, fraudulent access control system credit, etc., to prevent theft Brushing or proxy brushing, the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0036] The features and technical effects of the technical solution of the present invention will be described in detail below with reference to the accompanying drawings and in conjunction with schematic embodiments, and an access control system, a robot and an operation method thereof that can effectively prevent fraudulent brushing or proxy brushing and improve security are disclosed. It should be pointed out that similar reference numerals represent similar structures, and the terms "first", "second", "upper", "lower" and the like used in this application can be used to modify various system components or method steps . These modifications do not imply a spatial, sequential or hierarchical relationship of the modified system components or method steps unless specifically stated.
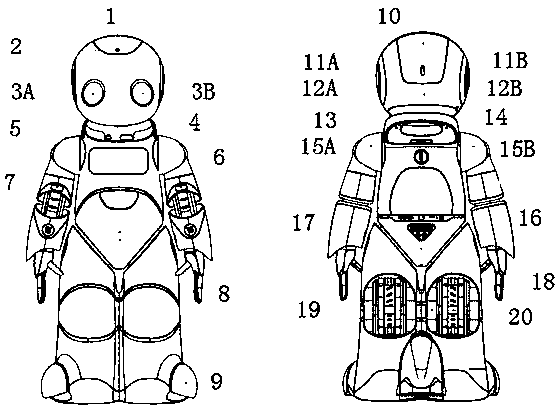
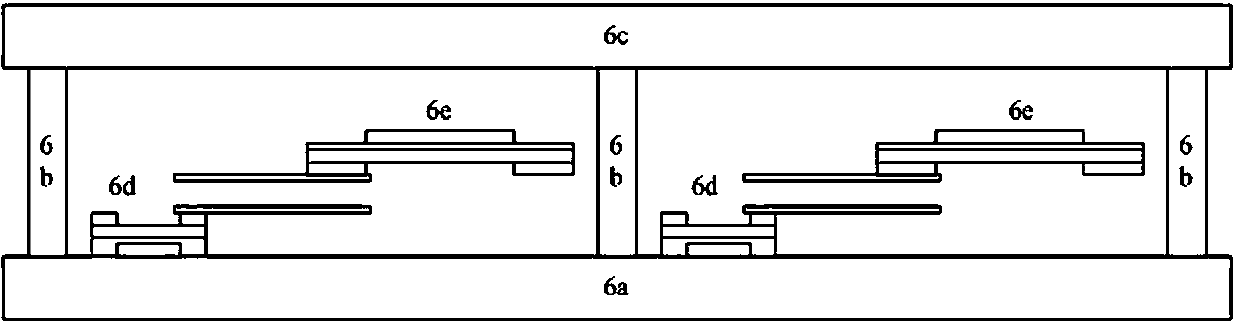
[0037] Such as figure 1 As shown, the access control robot according to the embodiment of the present invention includes: a high-sensitivity microphone 1 positioned at the top of the head for co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More