Proxy data integrity detection method based on identities in cloud storage
A technology of integrity detection and proxy data, which is applied in the field of cloud computing security to achieve the effect of reducing certificate overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0016] It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other. The present invention will be described in detail below with reference to the accompanying drawings and examples.
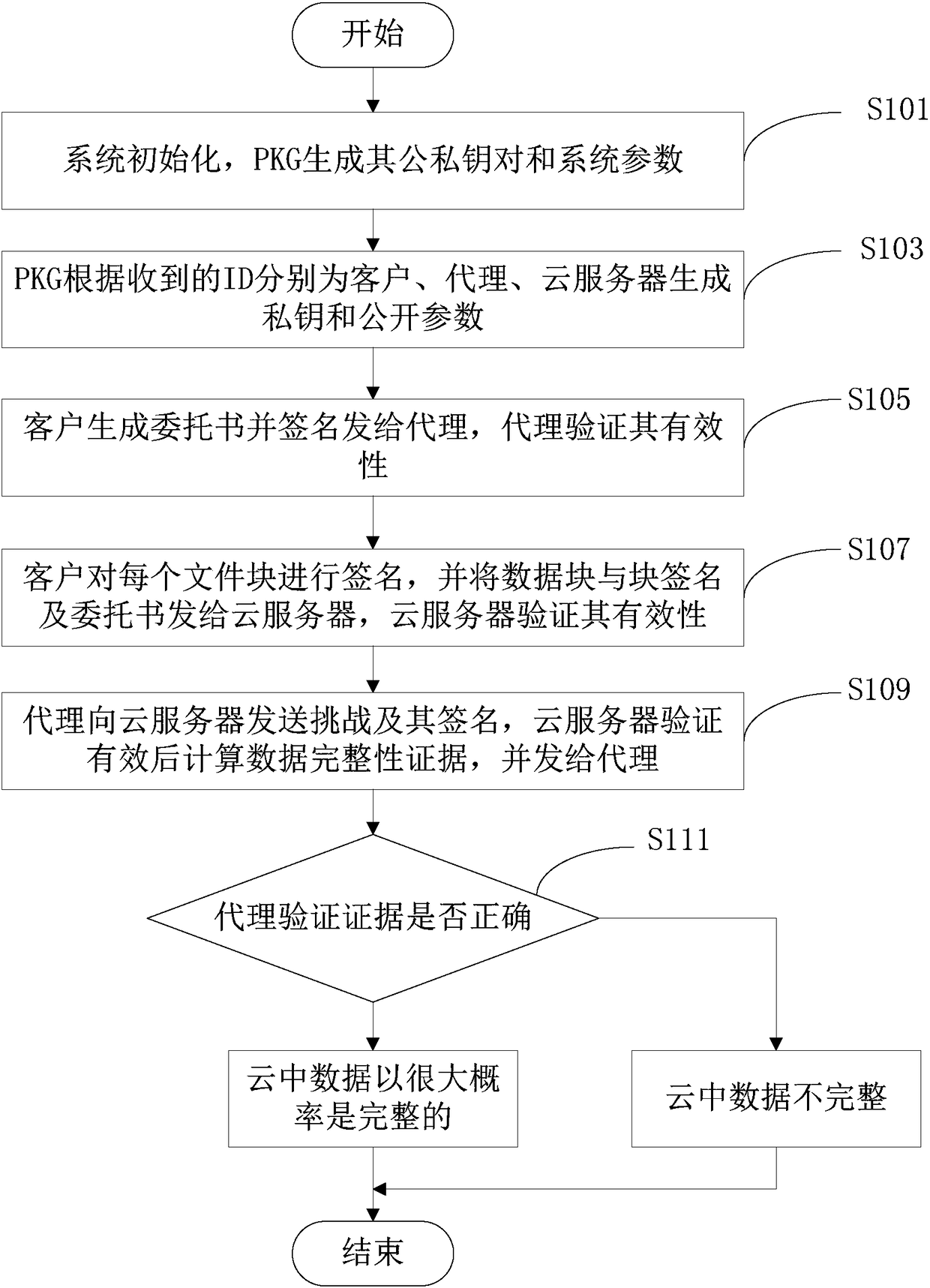
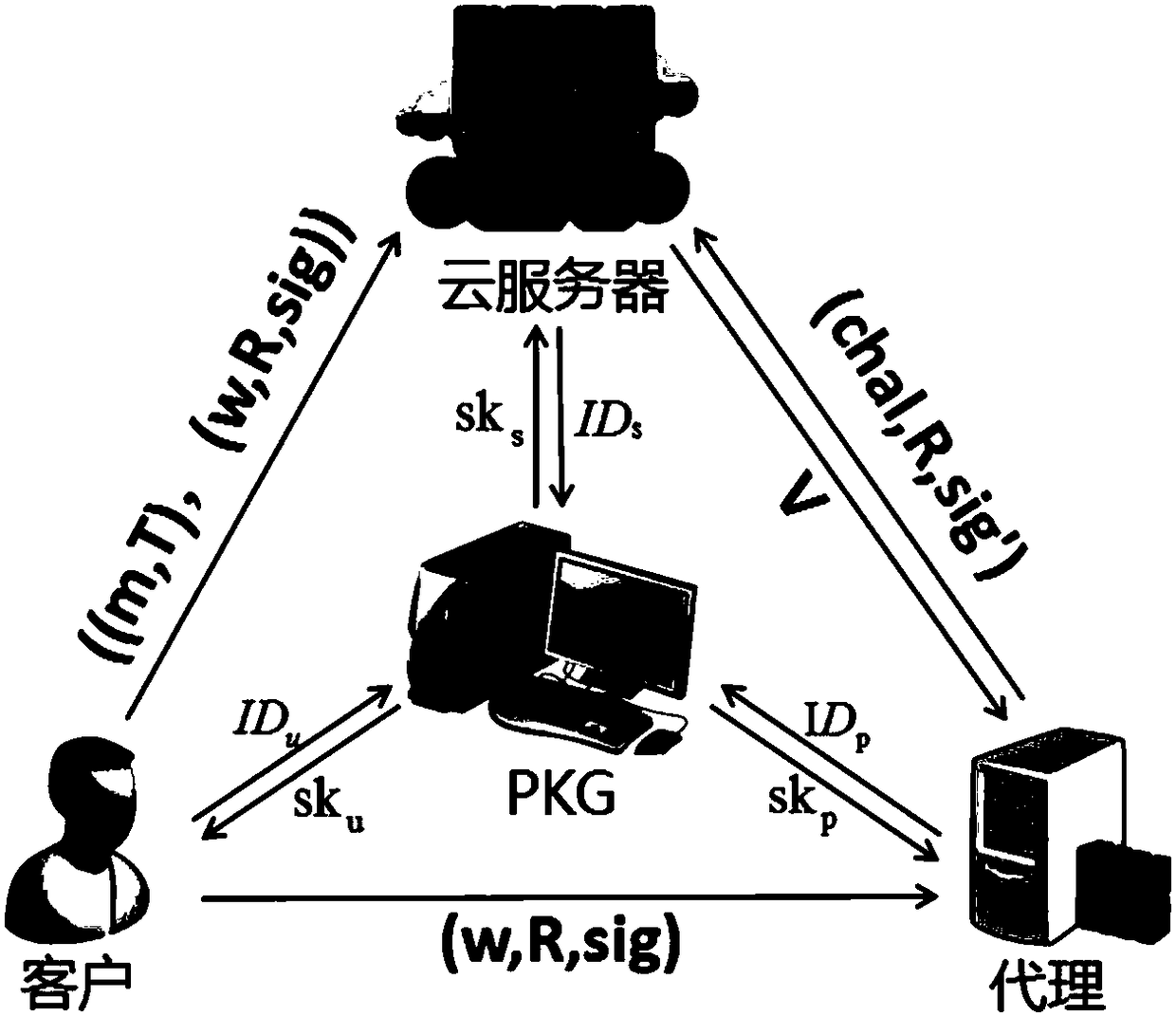
[0017] Such as figure 1 As shown, the identity-based proxy data integrity detection method of the present invention is applied to a cloud storage system, and the system includes four participating objects: PKG, client, cloud server and proxy.
[0018] Among them, PKG: the secret key generator is a trusted third party, which can authenticate all parties and issue private keys to them according to their respective identities.
[0019] Among them, the customer: can be an individual or an organization, and there is a large amount of data that needs to be transferred to the cloud server for storage. At the same time, the label will be calculated for each data block according to its private key, and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More