Vulnerability detection method and device
A vulnerability detection and vulnerability technology, applied in the computer field, can solve the problems of error-prone, low efficiency of manual detection, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
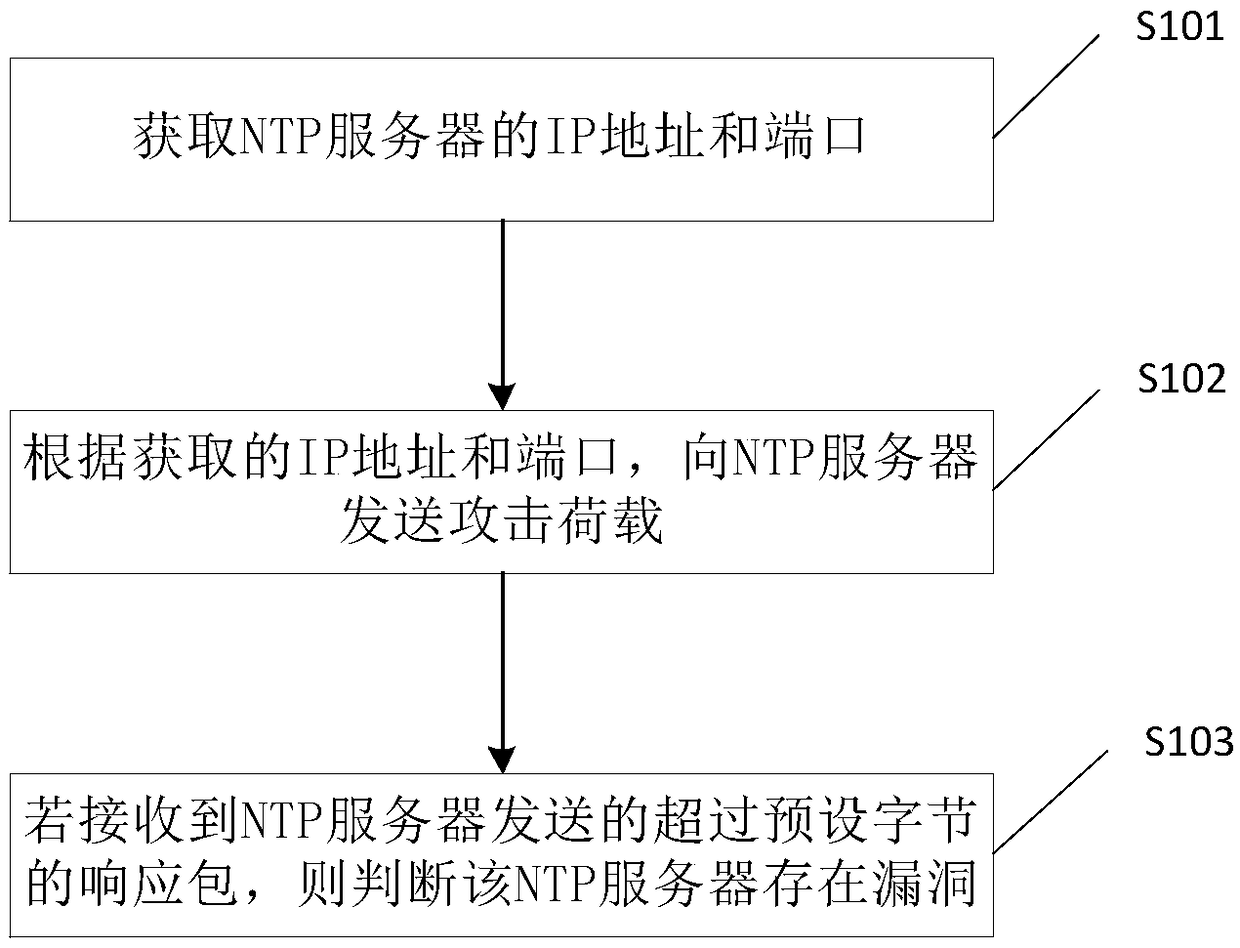
Method used
Image
Examples
Embodiment Construction
[0036] The inventor found through research that the standard NTP service provides a monlist query function. Specifically, after receiving the monlist query request, the NTP server can obtain the IP addresses of the last 600 clients that have time-synchronized with the NTP server, and convert these IP addresses Split to form multiple response packets, and return these response packets to the client. For example, the number of response packets may be 100, and each response packet may include 6 IP addresses.
[0037] The attacker can forge the source IP address of the NTP request, and send a monlist query request to the NTP server through the forged source IP address. When the NTP server has vulnerabilities, these forged source IP addresses cannot be filtered or screened. Therefore, the The IP address sends a large number of response packets to the real source IP address, for example, 100 UDP packets can be sent to the real source IP address. In this way, the attacker can send a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More