A fog computing industrial protocol construction method and system based on a generative adversarial network
An industrial protocol and construction method technology, which is applied in the field of fog computing industrial protocol construction method and construction system based on generative adversarial network, which can solve the problem that adversarial network has not been used in depth.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
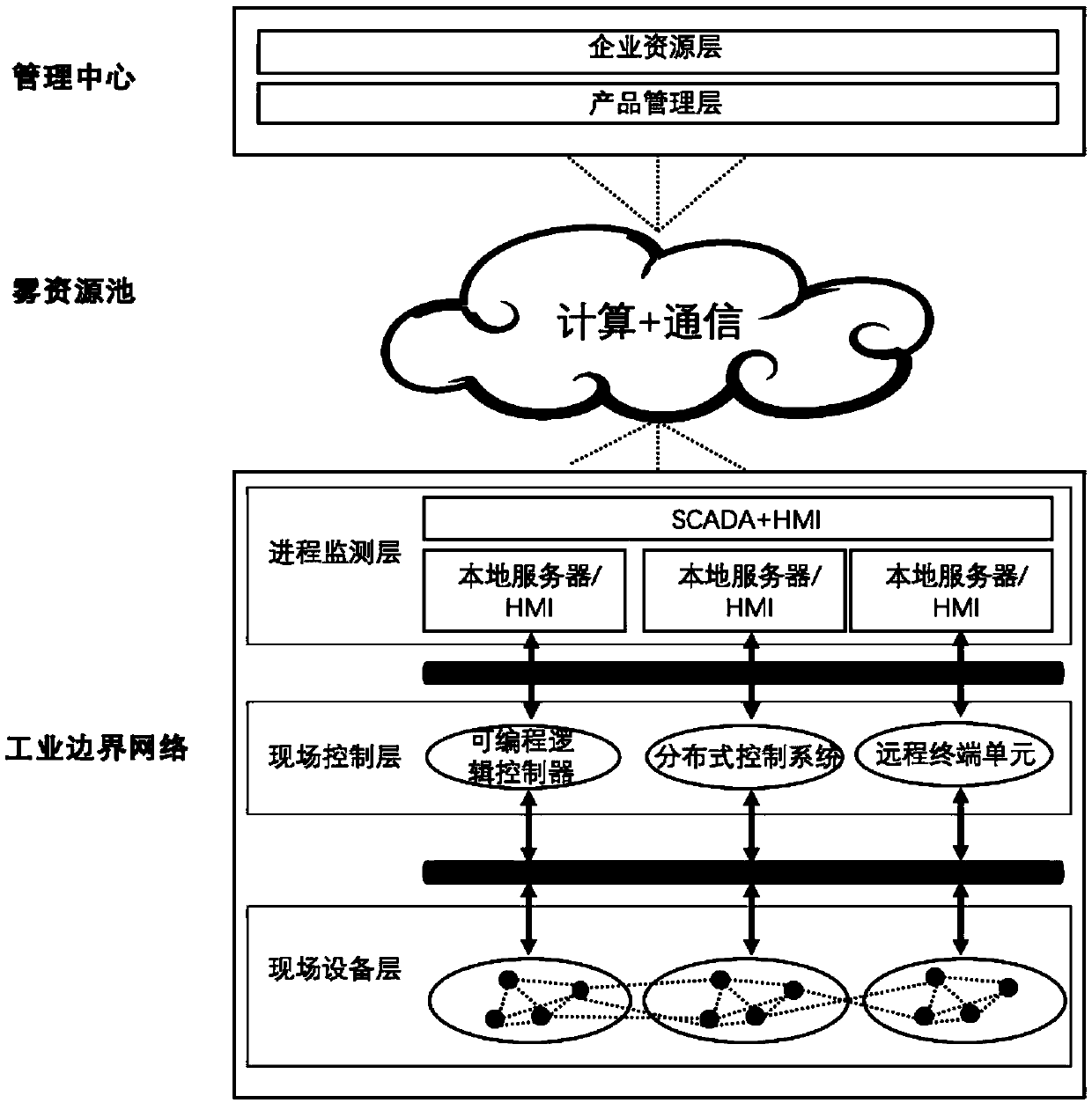
[0032] In conjunction with the following specific embodiments and accompanying drawings, the invention will be further described in detail. The process, conditions, experimental methods, etc. of implementing the present invention, except the content specifically mentioned below, are common knowledge and common knowledge in this field, and the present invention has no special limitation content.
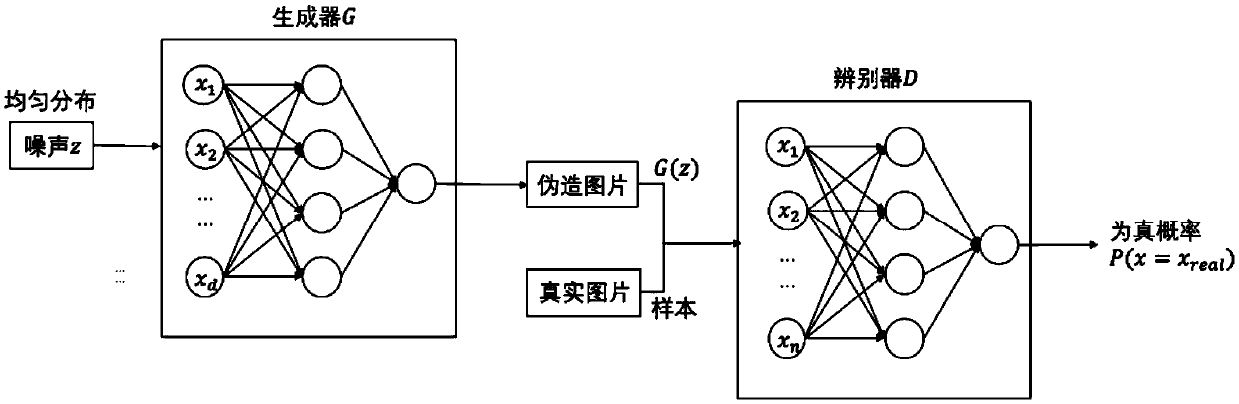
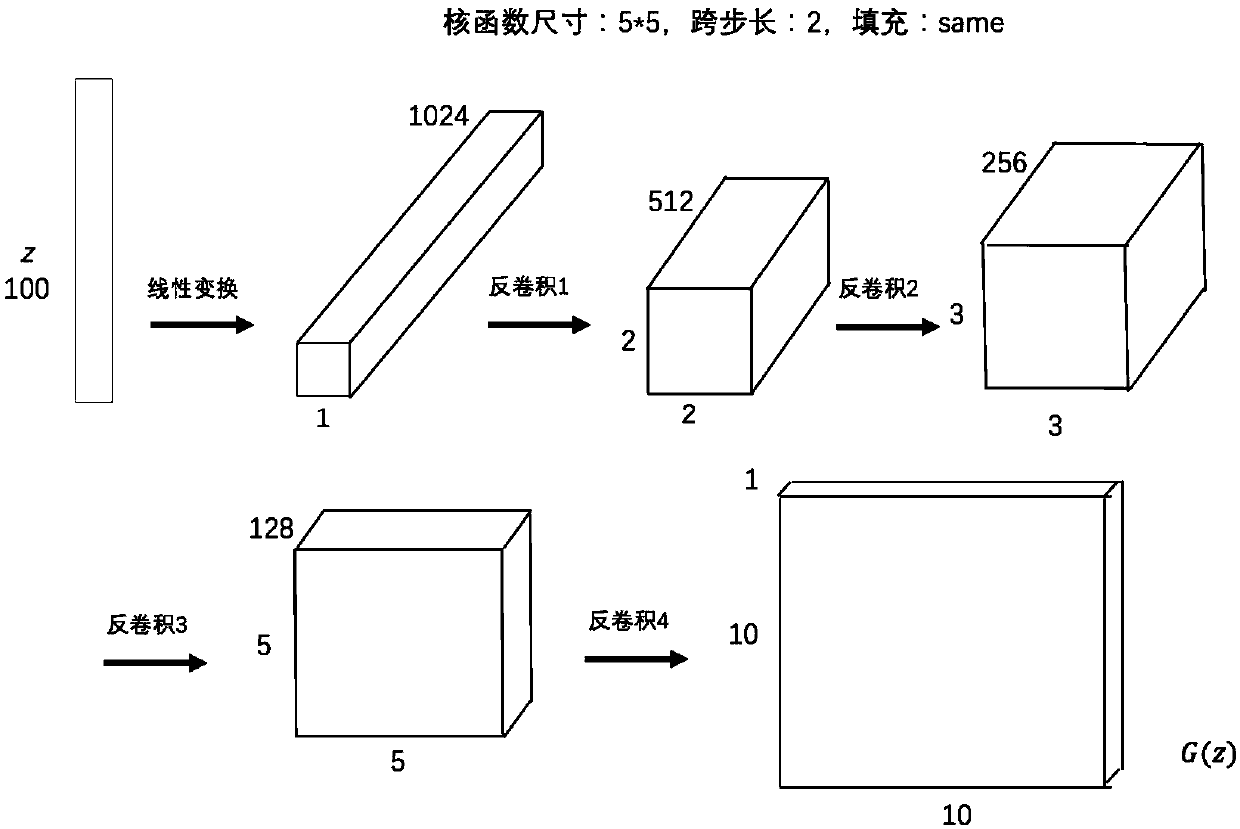
[0033] The honeypot is deployed in the industrial system based on fog computing through traditional technology, but the actual industrial protocol is not used when deploying the honeypot, but the simulation protocol is used. For industrial protocols used in fog computing, its payload bytes can be represented by values in [0, 255], which is consistent with the pixel format of grayscale images. Therefore, the industrial protocol stream can be converted into a single-channel grayscale image, for example, the hexadecimal Siemens S7 communication protocol can be a 10×10 grayscale image. ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More