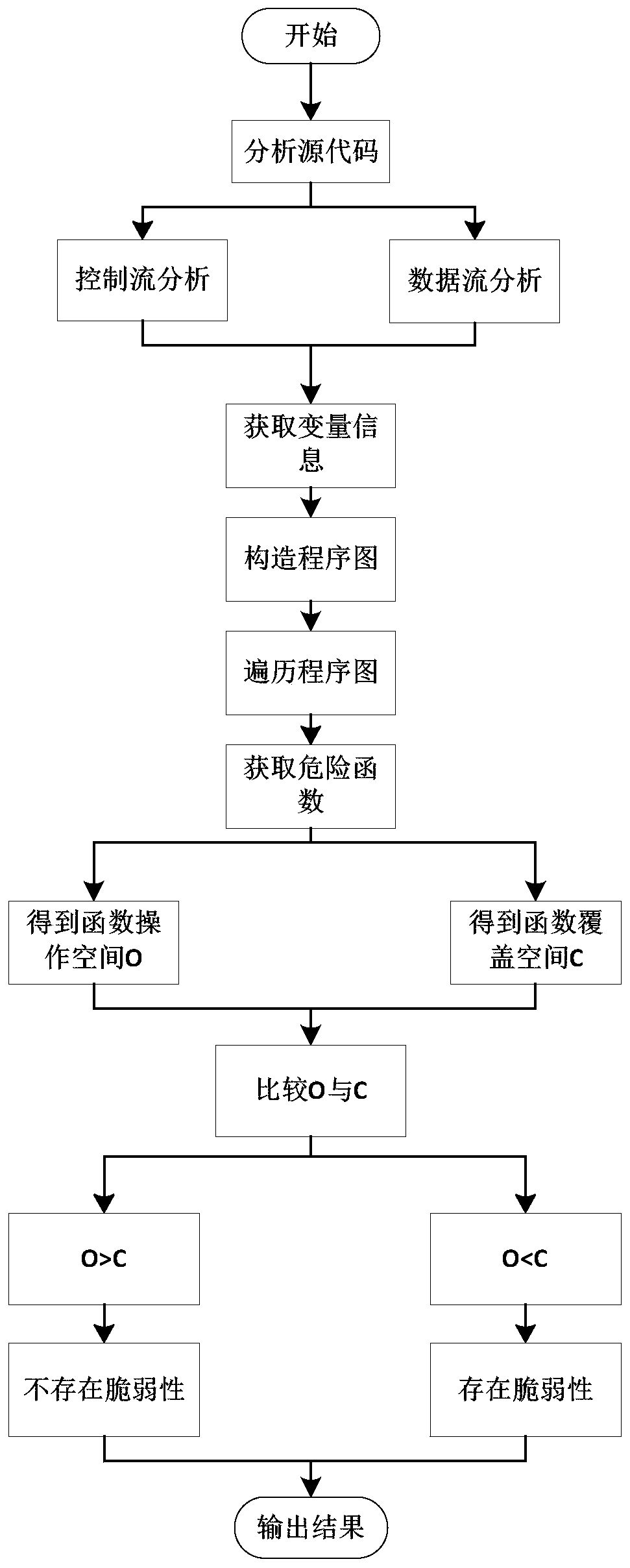
A stack buffer overflow vulnerability detection method based on a program diagram
A buffer overflow and detection method technology, applied in the field of information security, can solve the problems of high false negative rate and false positive rate, inaccurate modeling, attacks, etc., to achieve accurate detection, improve detection efficiency, and improve security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
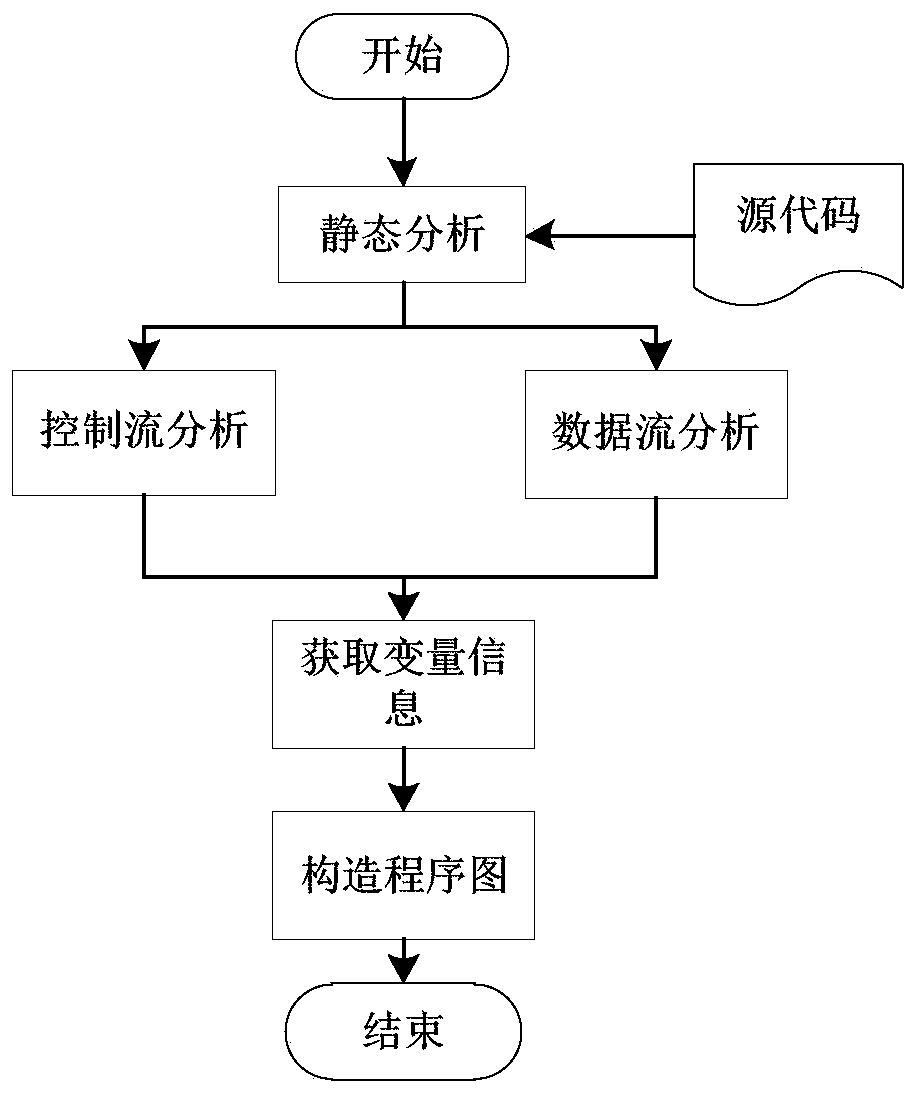
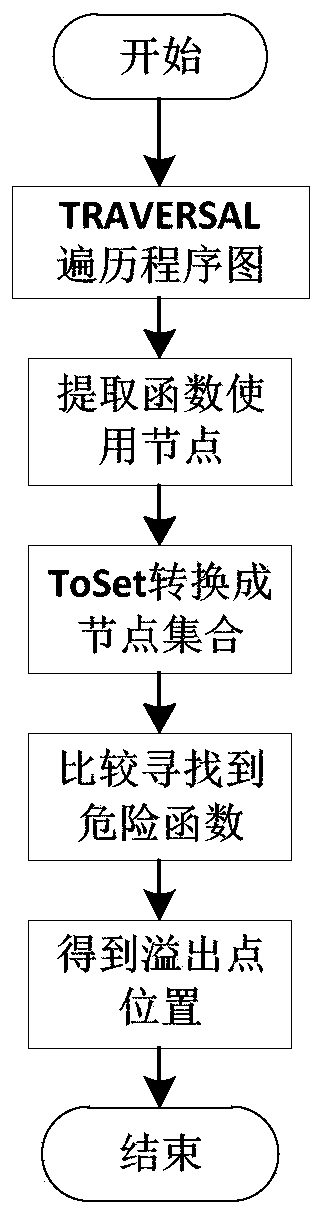
[0036] In order to better understand a stack buffer overflow vulnerability detection method based on a program diagram of the present invention, the present invention will be further described below in conjunction with the accompanying drawings and specific implementation cases. It should be pointed out that the described implementation cases are intended to This is to facilitate understanding of the present invention without requiring any limitation thereto.
[0037] The invention proposes a stack buffer overflow vulnerability detection method based on a program diagram, which can be better applied to the vulnerability detection of resource access software and improves detection efficiency.
[0038] First, the definitions and calculation formulas of several concepts involved in the present invention are as follows.
[0039] Definition 1 Program diagram: also known as program flow chart, which graphically expresses the logical function of the code, the logical flow direction o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More