An implicit authentication method, apparatus and computer-readable storage medium
An implicit authentication and algorithm technology, applied in computer parts, computing, secure communication devices, etc., can solve problems such as cloud platform and user privacy leakage, and achieve the effect of improving accuracy and protecting behavior privacy.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] The present invention will be described below with reference to the accompanying drawings and embodiments.
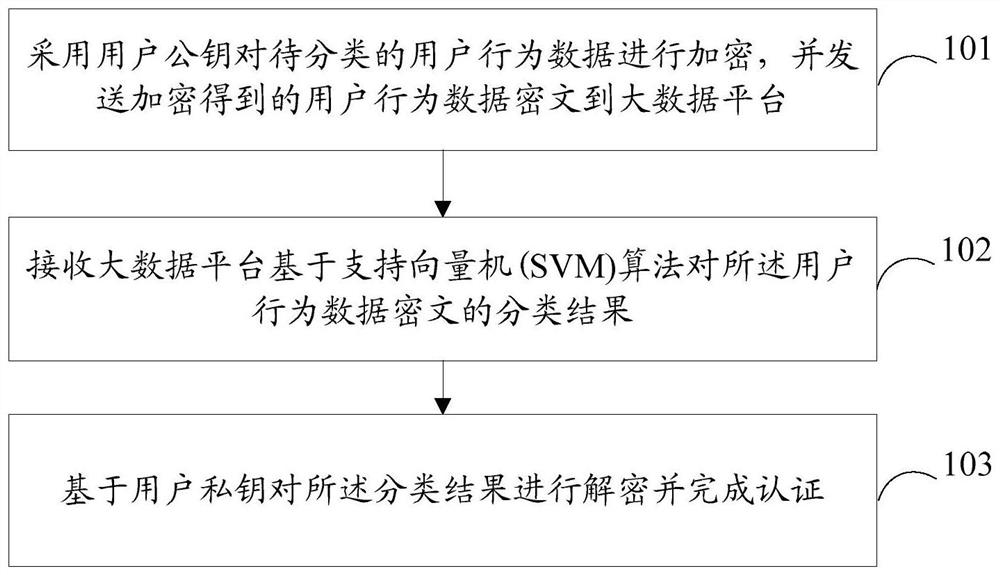
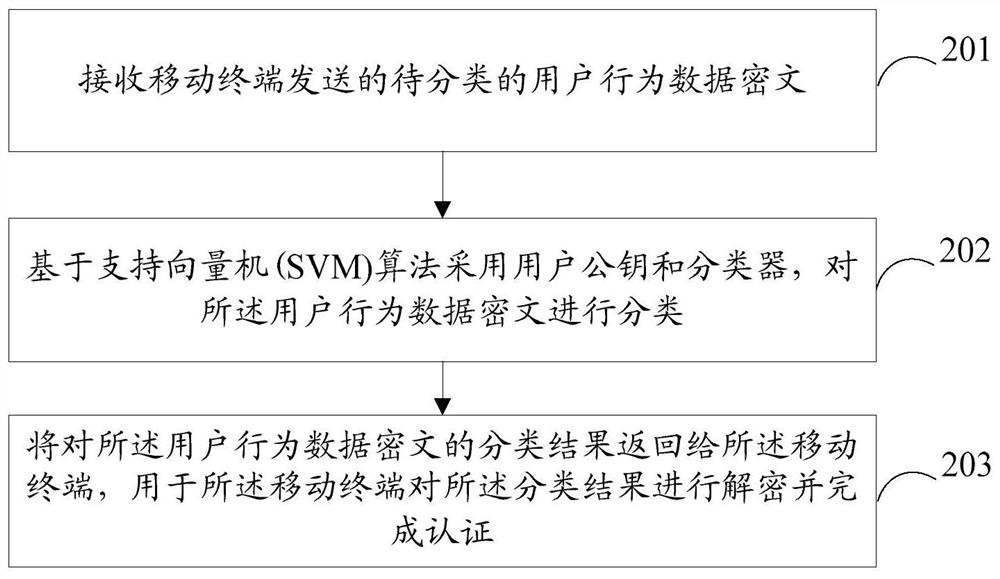
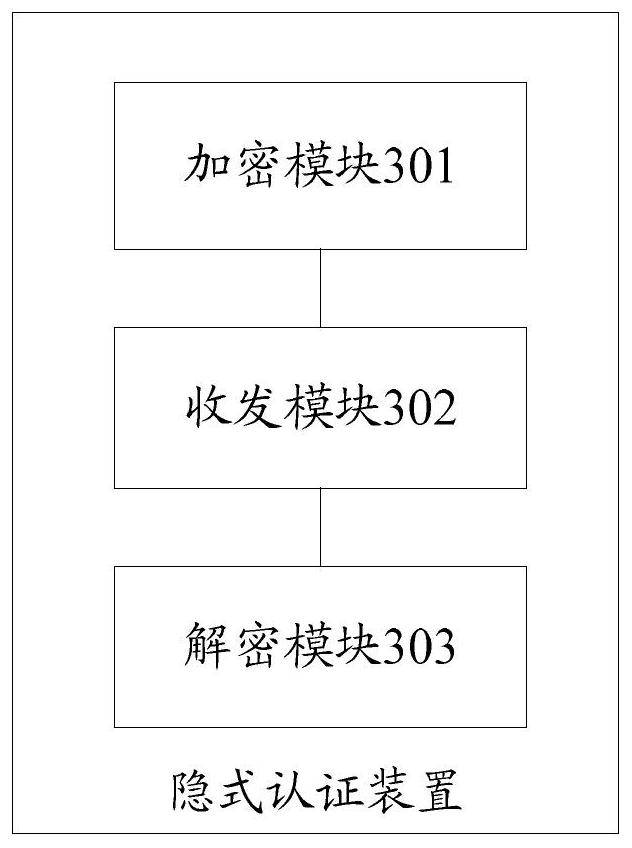
[0047] The embodiment of the present invention provides an implicit authentication method, and the method is applied to the mobile terminal side, such as figure 1 shown, including:
[0048] Step 101: Encrypt the user behavior data to be classified using the user public key, and send the encrypted user behavior data ciphertext to the big data platform;
[0049] Step 102: Receive the classification result of the user behavior data ciphertext based on the support vector machine SVM algorithm by the big data platform;
[0050] Step 103: Decrypt the classification result based on the user's private key and complete the authentication.
[0051] In the embodiment of the present invention, the mobile terminal encrypts the user behavior data to be classified by using the user public key and sends it to the big data platform, so that the semi-trusted big data platform ca...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More