Secure storage method and system suitable for embedded real-time operating system
A real-time operating system and embedded system technology, applied in the computer field, can solve the problems of embedded real-time systems that cannot meet performance requirements, affect system performance, and low portability, so as to improve development efficiency, high flexibility, and reduce development cost effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
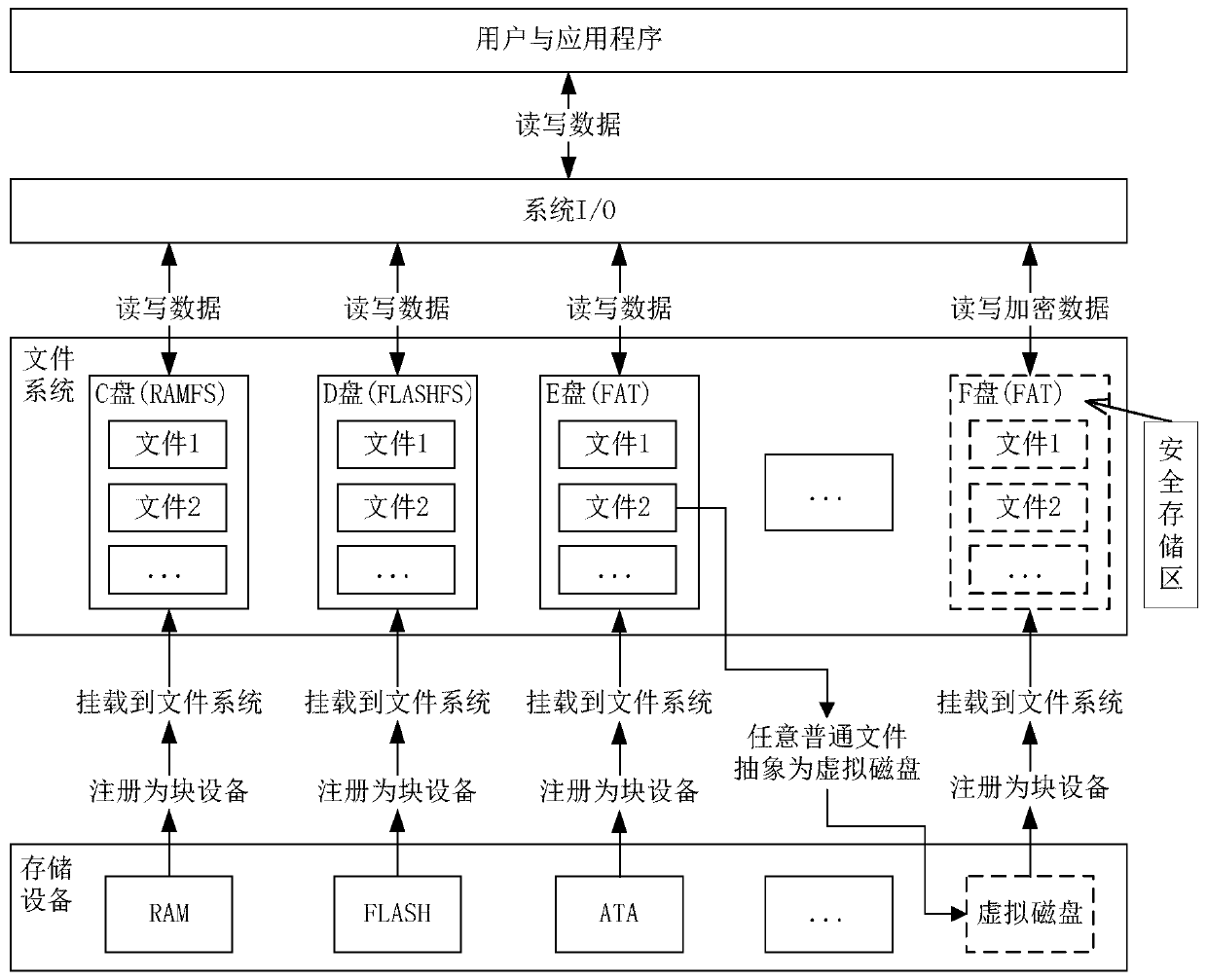
[0065] Take an embedded real-time operating system whose storage device is a SATA hard disk and whose file system is FAT as an example. Users or applications first configure secure storage parameters, including bearer device information (SATA), storage capacity (such as 10M), number of virtual disks, encryption and decryption algorithms (such as DES), key specifications, etc. Add the secure storage into the embedded operating system, start the system, and initialize the secure storage module for the first time.
[0066] During the initial initialization, parameter checks or system resource checks will be performed. If the parameters are illegal, the free capacity of the bearer device is insufficient or cannot be accessed, the creation of the secure storage area will fail, otherwise the creation will succeed. After the virtual disk is successfully created, register it with the I / O subsystem as a block device, write basic information, keys and other security information, and mou...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More