Automatic deployment method for improving remote login safety of elastic cloud host
A remote login and automatic deployment technology, applied in the field of cloud hosts, can solve problems such as time-consuming, labor-intensive, repetitive labor, and easy to be attacked, and achieve the effects of wide application, improved security, and strong scalability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
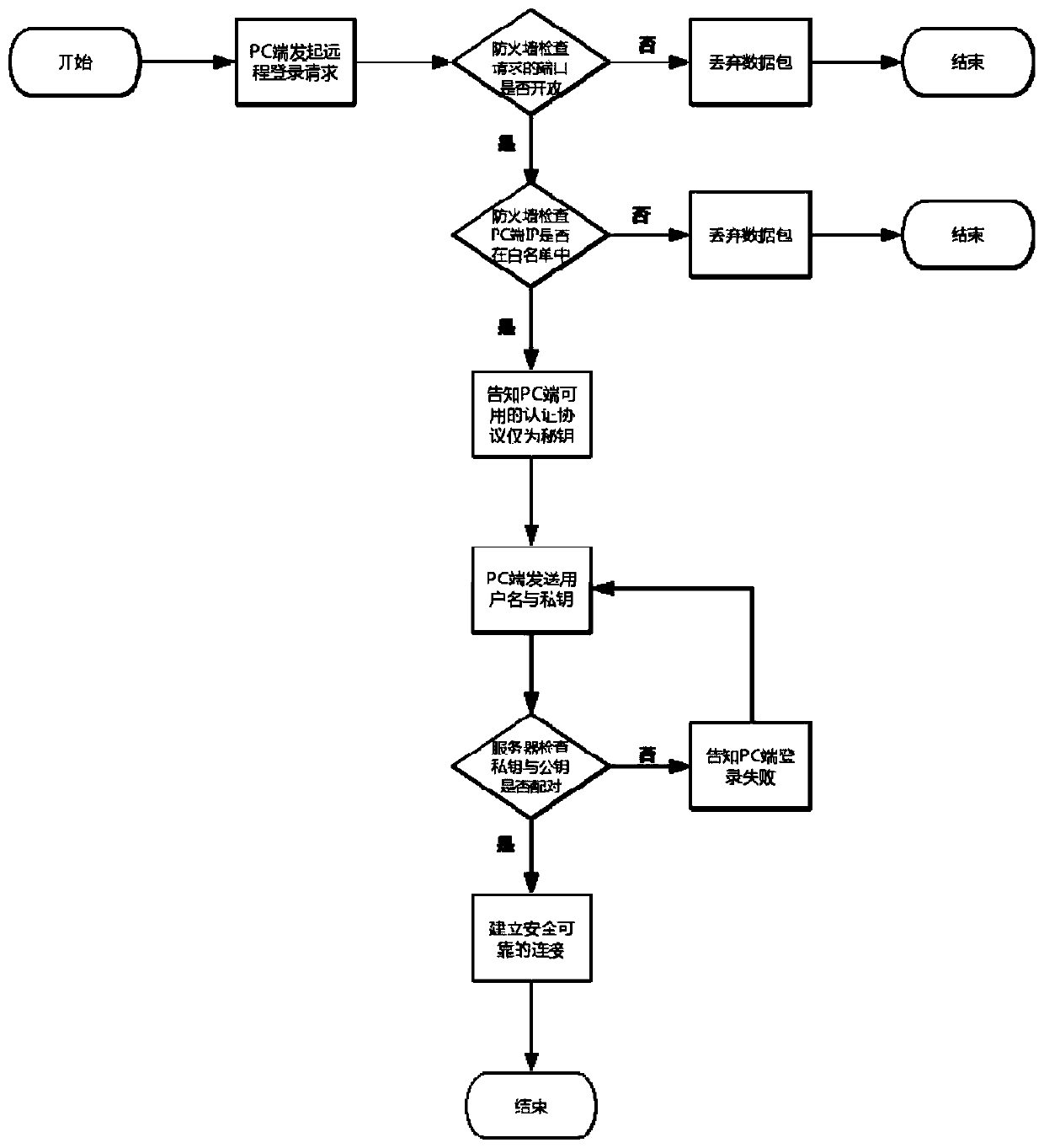
[0021] The technical solution of the present invention will be explained more clearly and completely through the description of preferred embodiments of the present invention in conjunction with the accompanying drawings.
[0022] Such as figure 1 As shown, an automatic deployment method for improving the remote login security of an elastic cloud host in the preferred embodiment of the present invention includes the following steps:
[0023] S1: The remote automatic deployment starts, and the PC initiates a login request to the system. The remote access processing module in the system checks whether the requested port is open and makes a judgment. If yes, enter the next step; otherwise, discard the data packet and end the request;
[0024] S2: The remote access processing module checks whether the IP of the PC is in the white list, and judges, if yes, enters the next step, otherwise discards the data packet and ends the request;
[0025] S3: The remote access processing modul...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More