Data display method and system for network resources
A data display and network resource technology, applied in the field of data processing, to achieve the effect of improving convenience and comfort
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
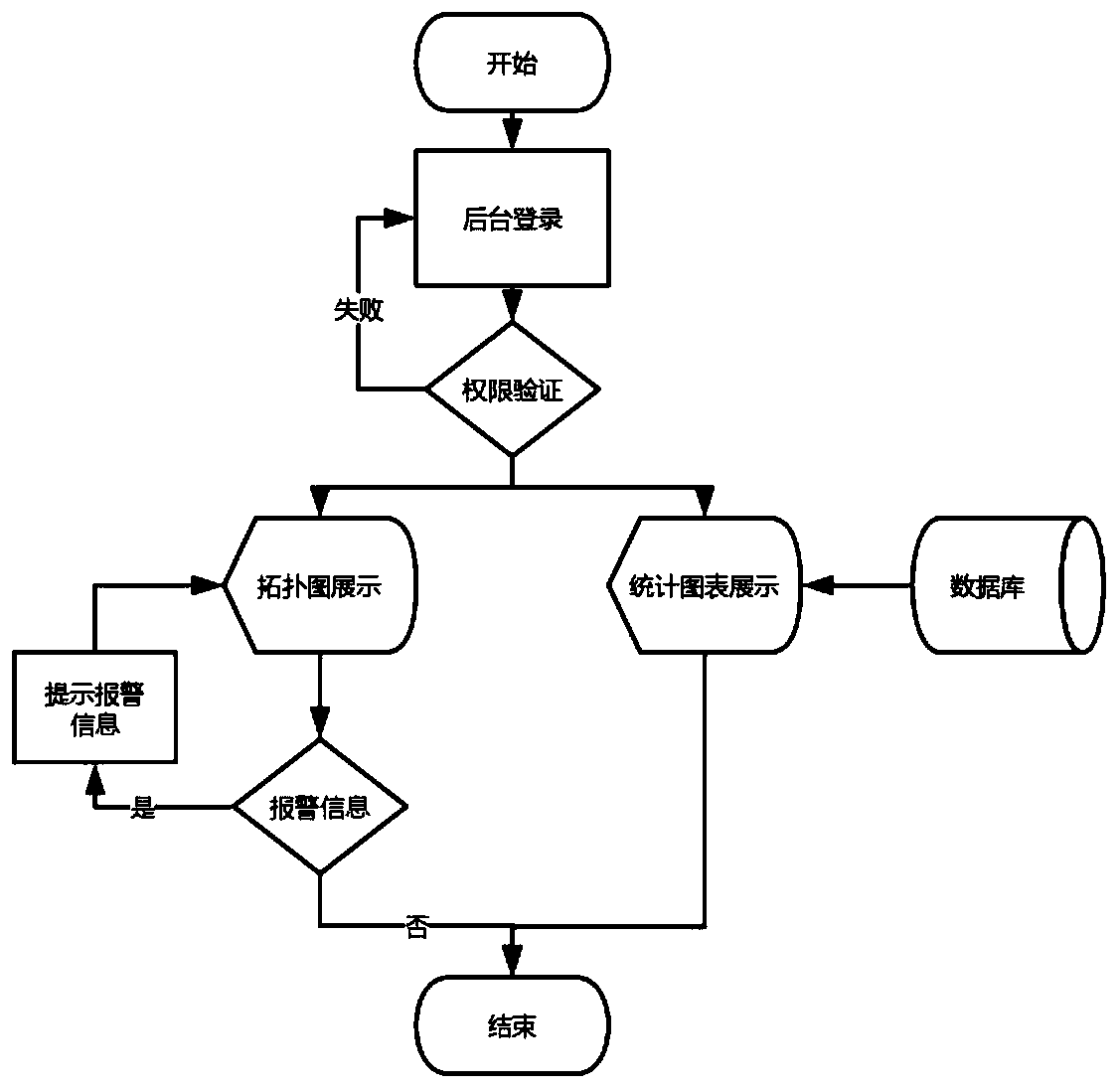
[0033] refer to figure 1 , which is a schematic diagram of the overall flow of a method for displaying network resource data proposed by this embodiment. The method specifically includes the following steps,
[0034] S1: User login and authority verification; among them, user authority can be divided into three categories, ordinary user, management user and advanced user, ordinary user can only view the topology map, alarm topology map and equipment within the set authority range Information; In addition to having the right to view information, management users can also manage and set permissions, such as assigning and setting permissions for all users, upgrading or removing user permissions, changing device locations or basic information, and exporting logs, etc. ;Advanced user permissions can view the location topology map and device information of all devices, and can view the data charts after data visualization to make decisions, and can also export logs.
[0035] S2: If...
Embodiment 2
[0060] refer to Figure 4 , which is a schematic diagram of a network resource data display system proposed in this embodiment. The network resource data display method proposed in the above embodiment can verify users and provide information to them according to different types of user needs. The information of the device is displayed, and the data display system based on the network resources of this embodiment can realize the above content.
[0061] The data display system for network resources includes an authority verification module 100 , a device management module 200 , a data analysis module 300 , a data display module 400 and an alarm module 500 . specific,
[0062] The authority verification module 100 is used to verify the user's authority;
[0063] The device management module 200 is used for managing and storing device information;
[0064] The data analysis module 300 can perform data analysis according to the input, and output the analysis result;
[0065] T...
Embodiment 3
[0072] Based on the above-mentioned embodiments, a data display method for network resources is proposed. In order to prevent resource information leakage caused by malicious polling attacks and illegal logins to the network resource system, this embodiment proposes an access control method for network resources in order to improve the security of network resources. In this method, when polling the alarm operation of each device status, access authorization or unauthorized permission is required to improve the management security of the entire network resource.
[0073] Access control is the process of controlling the user's execution of certain operations or access to certain network resources based on the identity or attributes of the network user. It can provide a more secure, flexible and dynamic access authorization mechanism, thereby improving the security and reliability of the authorization mechanism. sex.
[0074] Specifically, the unauthorized access control method f...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More