Sensitive data security protection method and system based on shadow system
A sensitive data and security protection technology, applied in the field of data security, can solve the problem of low security of sensitive data, achieve the effect of improving security and data security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 2
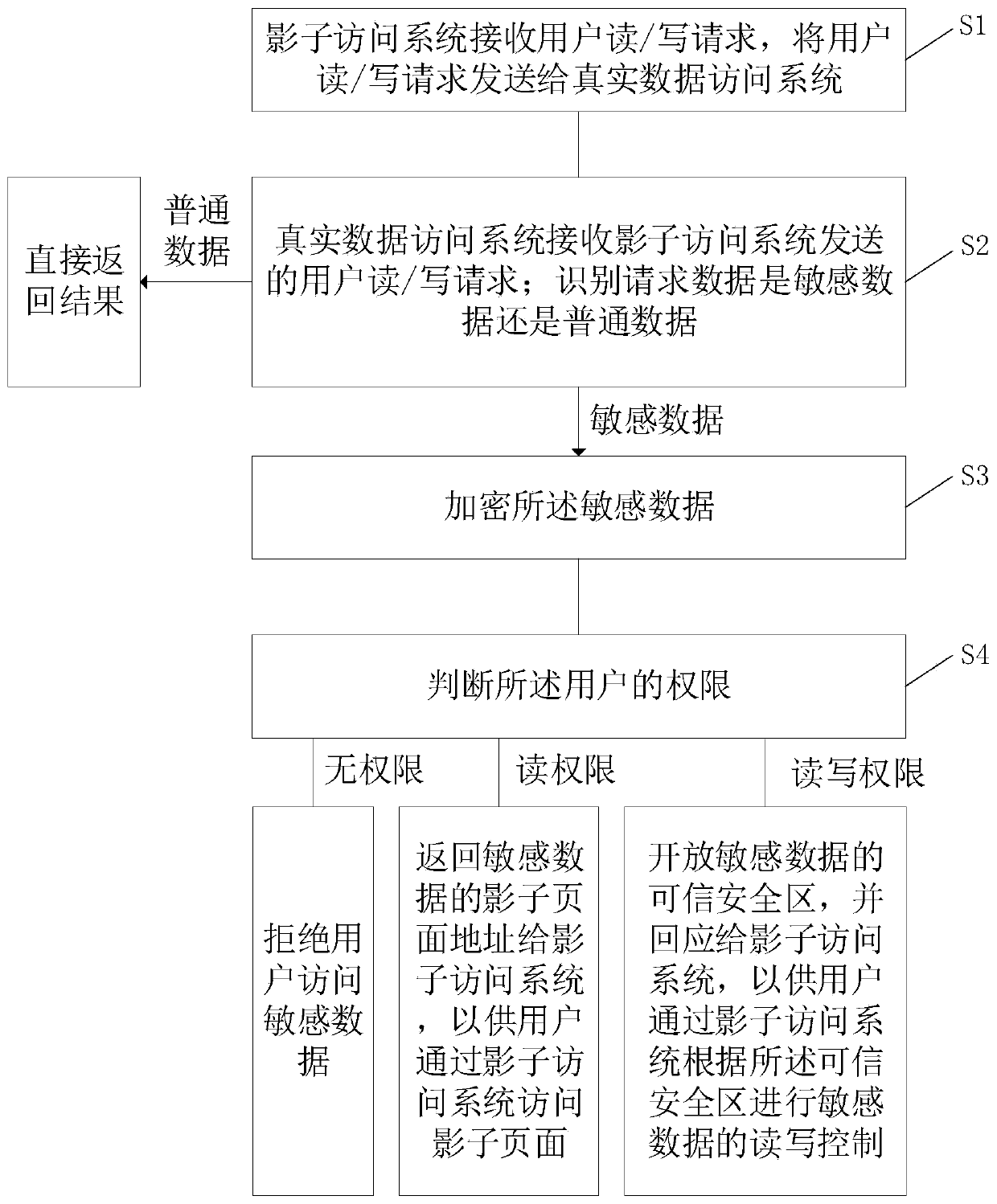
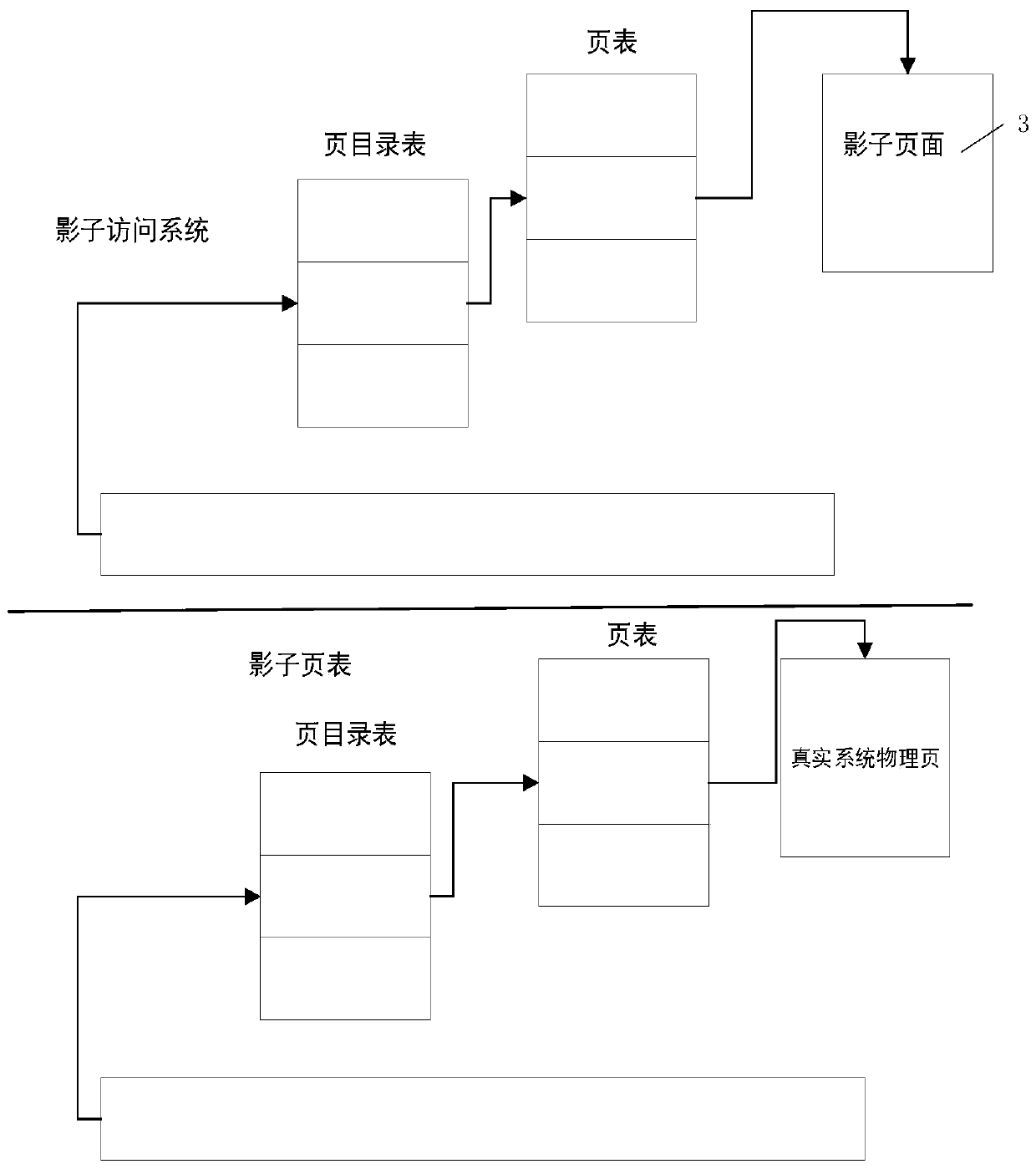
[0112] see figure 2 with Figure 5 , a sensitive data security protection system based on a shadow system, including a shadow system 1 and a real data access system 2, and the real data access system 2 includes a sensitive data identification module 21;
[0113] The shadow system is used to receive user read / write requests, and send user read / write requests to the real data access system;
[0114] The real data access system is used to receive user read / write requests sent by the shadow system; and identify whether the requested data is sensitive data or ordinary data through the sensitive data identification module; for ordinary data, directly return the result; for sensitive data, encrypt the sensitive data data, and determine the authority of the user;
[0115] If the user does not have access to sensitive data, deny the user access to sensitive data;
[0116] If the user only has read permission for sensitive data, return the address of the shadow page of the sensitive...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More