SIP security authentication method and system based on learning problem with errors on the loop
An error learning and problem technology, applied in the field of SIP security authentication methods and systems, can solve the problems of SIP protocol authentication vulnerable to attacks, poor security, and errors, and achieve good anti-attack effect.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0033] The present embodiment provides a SIP security authentication method based on the learning problem with errors on the ring;
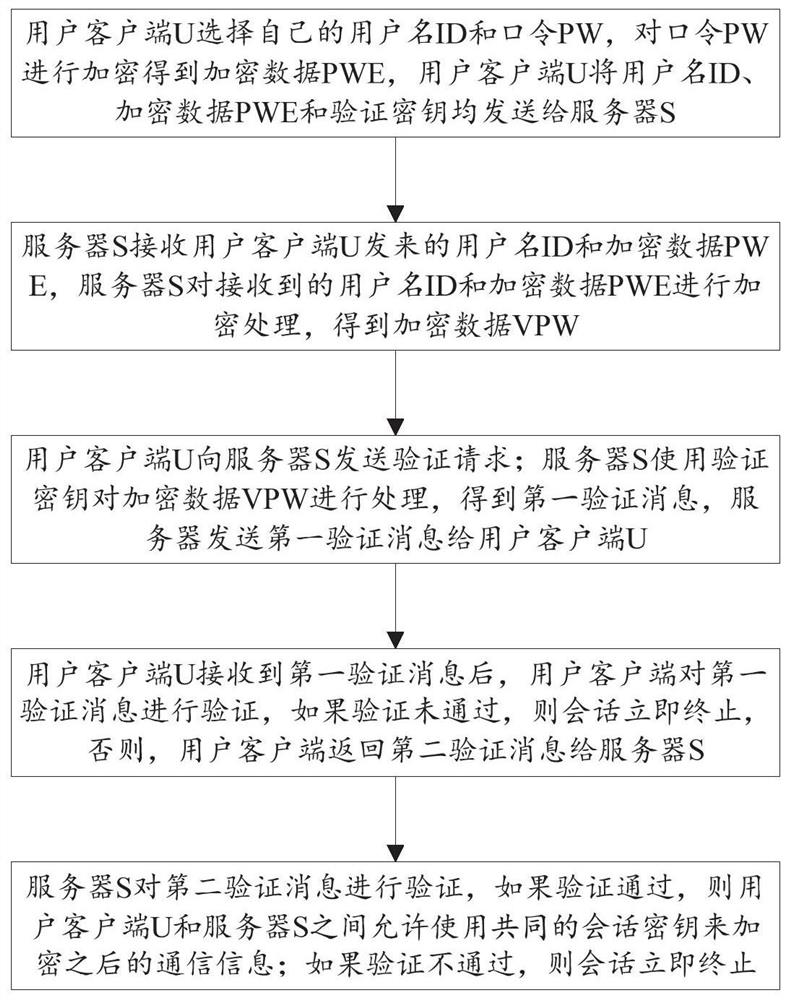
[0034] like figure 1 As shown, the SIP security authentication method based on the learning problem with error on the ring includes:
[0035] S101: the user client U selects its own user name ID and password PW, encrypts the password PW to obtain encrypted data PWE, and the user client U sends the user name ID, encrypted data PWE and verification key to the server S;
[0036] S102: The server S receives the username ID and encrypted data PWE sent by the user client U, and the server S encrypts the received username ID and encrypted data PWE to obtain encrypted data VPW;
[0037] S103: the user client U sends a verification request to the server S; the server S uses the verification key to process the encrypted data VPW to obtain a first verification message, and the server sends the first verification message to the user client U;
[0038] S104...
Embodiment 2
[0085] The present embodiment provides a SIP security authentication system based on the learning problem with errors on the ring;
[0086] The SIP security authentication system based on the error learning problem on the loop, including: user client U and server S;
[0087] The user client U selects its own user name ID and password PW, encrypts the password PW to obtain encrypted data PWE, and the user client U sends the user name ID, encrypted data PWE and verification key to the server S;
[0088] The server S receives the username ID and the encrypted data PWE sent by the user client U, and the server S encrypts the received username ID and encrypted data PWE to obtain the encrypted data VPW;
[0089] The user client U sends a verification request to the server S; the server S uses the verification key to process the encrypted data VPW to obtain a first verification message, and the server sends the first verification message to the user client U;
[0090] After the user...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More