Network training method, abnormal transaction behavior identification method and device, and medium
A network training and network technology, applied in the field of digital currency, can solve problems such as the use of Ethereum by criminals, and achieve the effect of saving computer resources
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
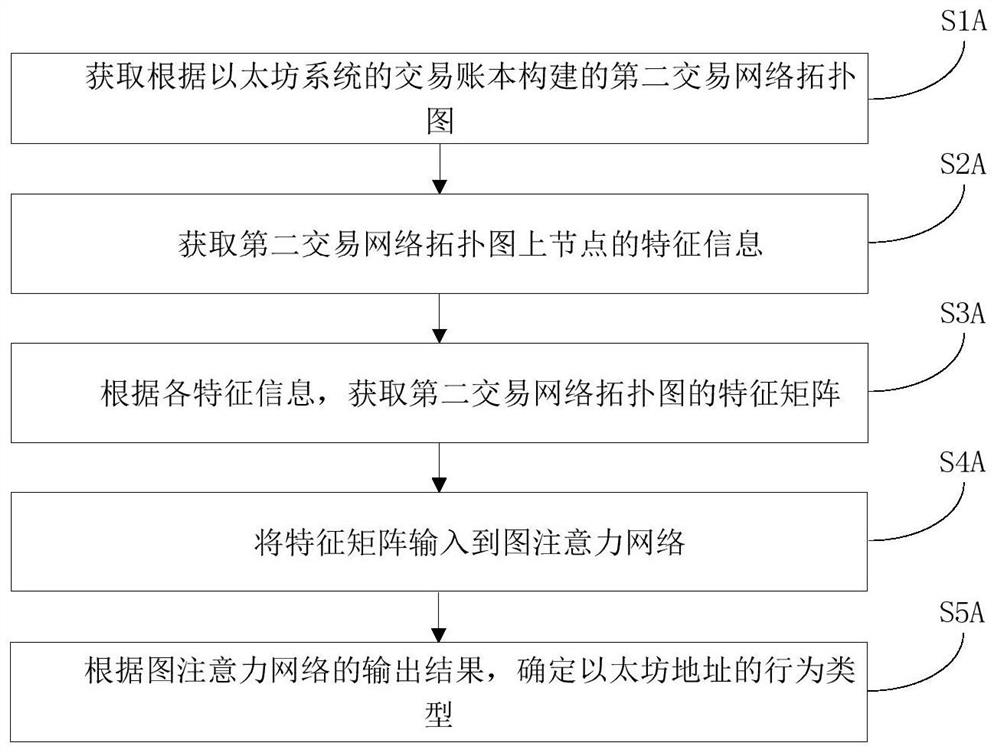
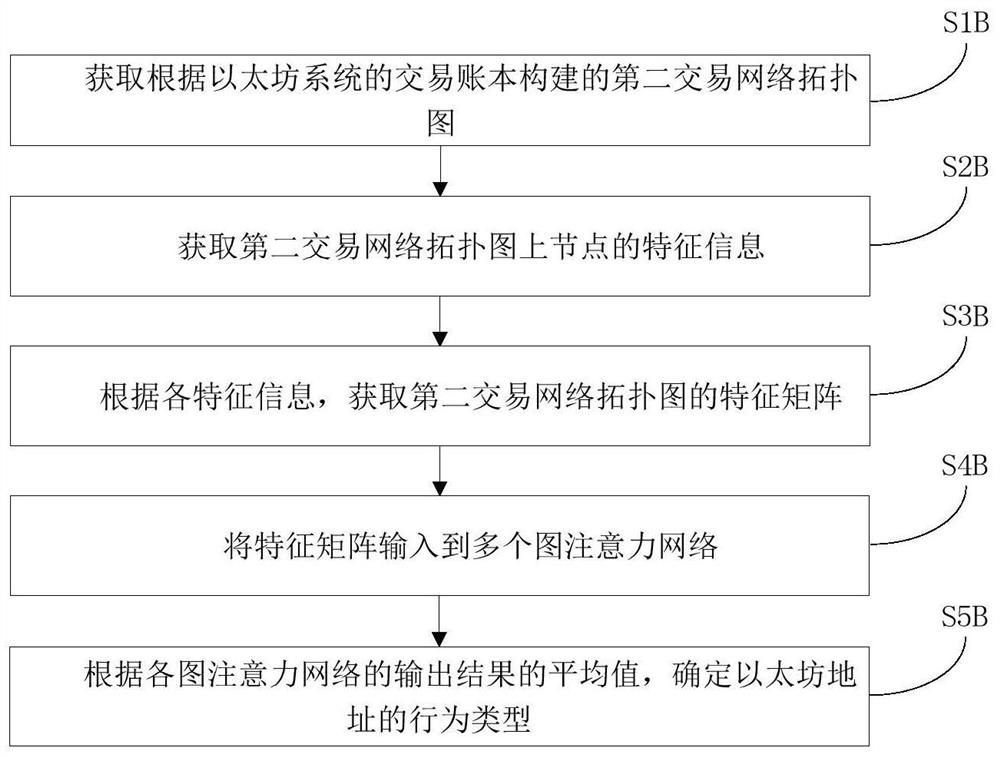
[0047] In the following embodiments, both the first transaction network topology diagram and the second transaction network topology diagram are transaction network topology diagrams, wherein "first" and "second" are used to distinguish transaction network topology diagrams in different processes, and the first The transaction network topology map and the second transaction network topology map may be the same or different. In this embodiment, the graph attention network used may be a graph convolutional neural network, GraphSAGE and other variants.
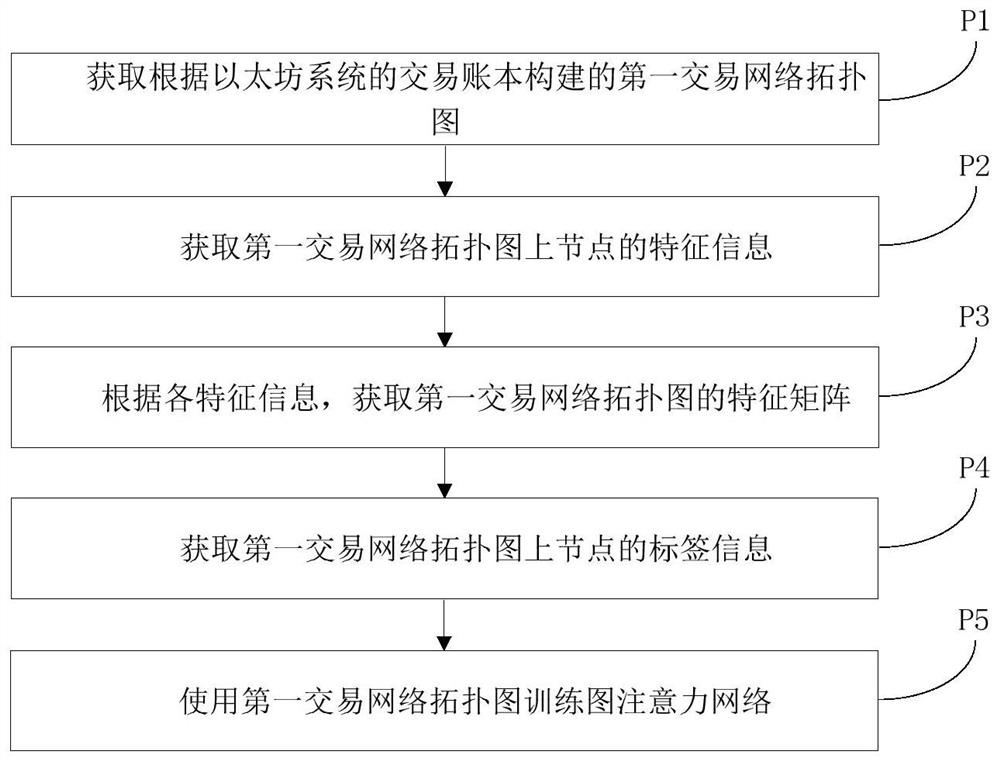
[0048] In this example, refer to figure 1 , the graph attention network training method includes the following steps:
[0049] P1. Obtain the topological map of the first transaction network constructed according to the transaction book of the Ethereum system;
[0050] P2. Obtain the characteristic information of the nodes on the topological map of the first trading network;
[0051] P3. Obtain the feature matrix of the first ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More