Network protection method and system based on false topology generation and system architecture
A topology generation and network technology, applied in the field of network security, can solve problems such as spoofing
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
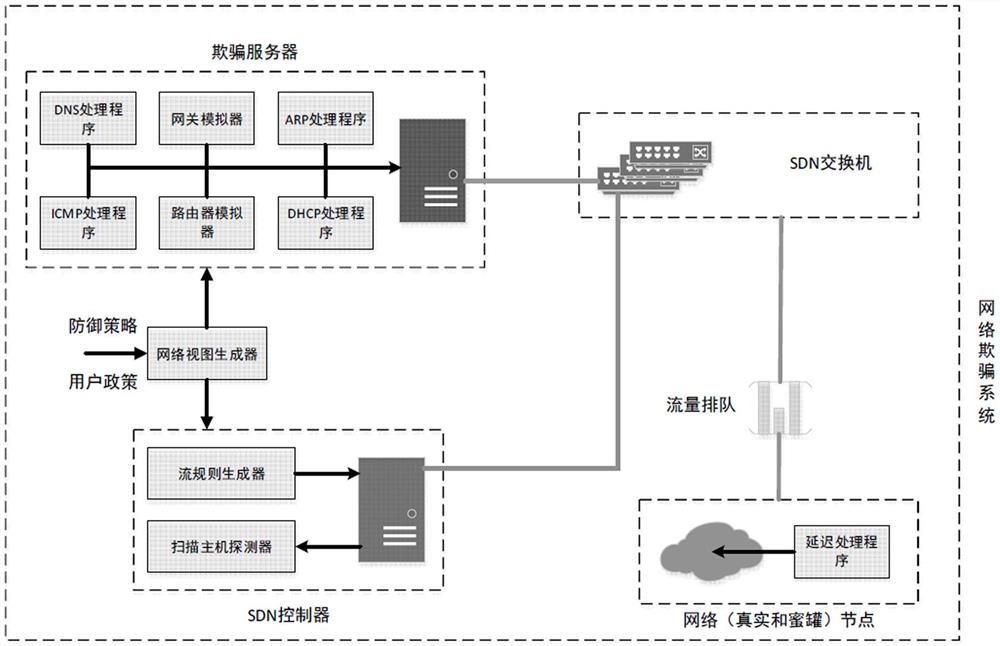
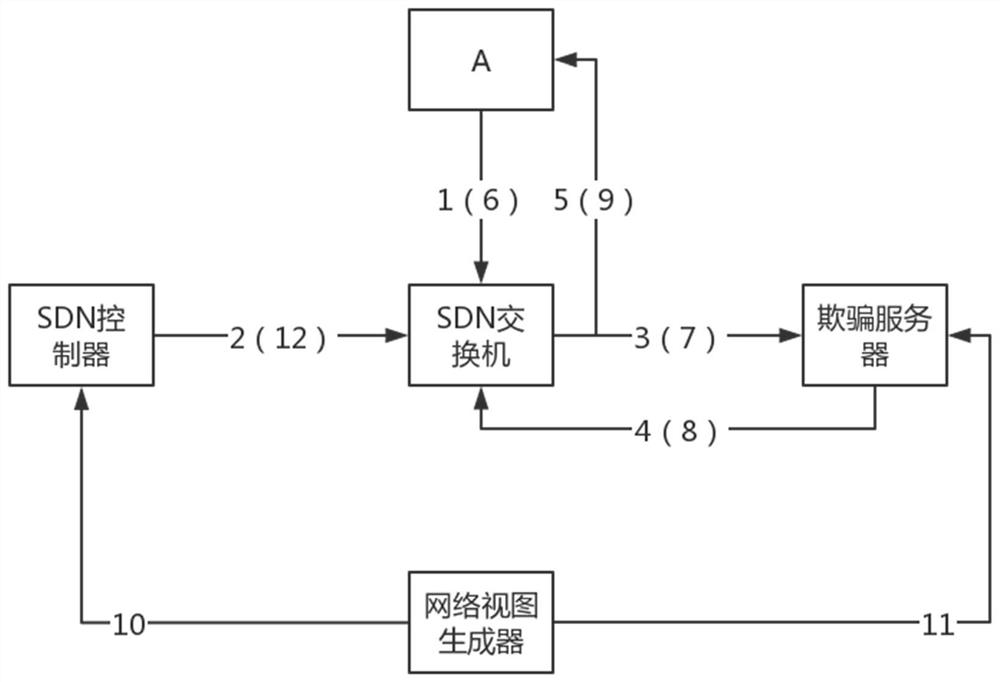
[0029] In order to make the purpose, technical solution and advantages of the present invention more clear and understandable, the present invention will be further described in detail below in conjunction with the accompanying drawings and technical solutions.
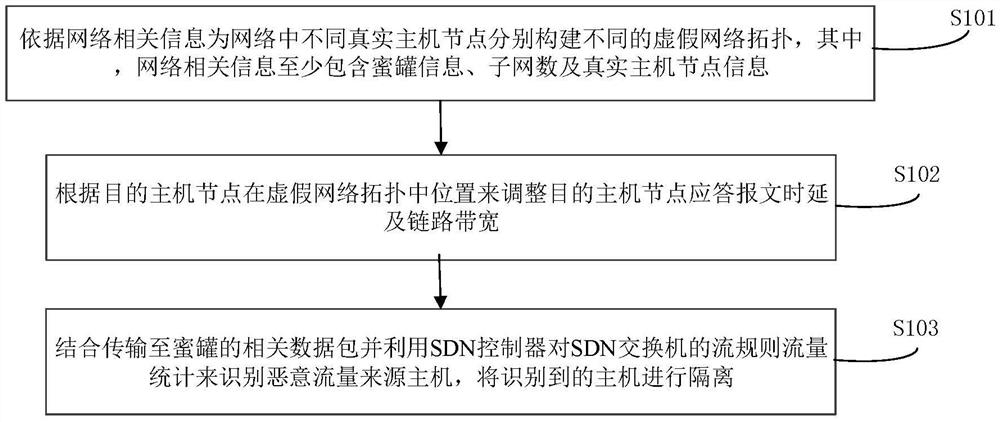
[0030] Embodiment of the present invention, see figure 1 As shown, a network protection method based on false topology generation is provided to deceive internal attackers to improve network security, including the following content:
[0031] S101. Constructing different false network topologies for different real host nodes in the network according to network-related information, wherein the network-related information at least includes honeypot information, number of subnets, and real host node information;
[0032] S102. Adjust the response message delay and link bandwidth of the destination host node according to the location of the destination host node in the false network topology;
[0033] S103. Combining rel...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More