Unsupervised autonomous attack detection method in endogenous security system
A security system and attack detection technology, applied in transmission systems, neural learning methods, biological neural network models, etc., can solve the problems of unsupervised attack recognition and localization, low recognition rate, and lack of reliable pre-annotated data based on machine learning methods.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
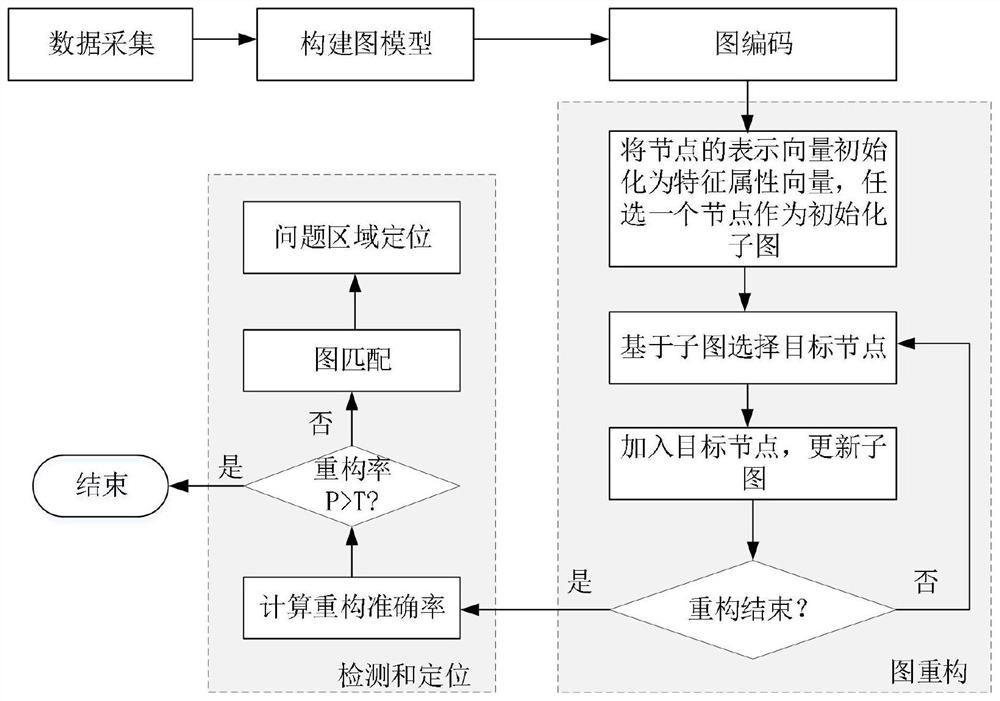
[0037] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
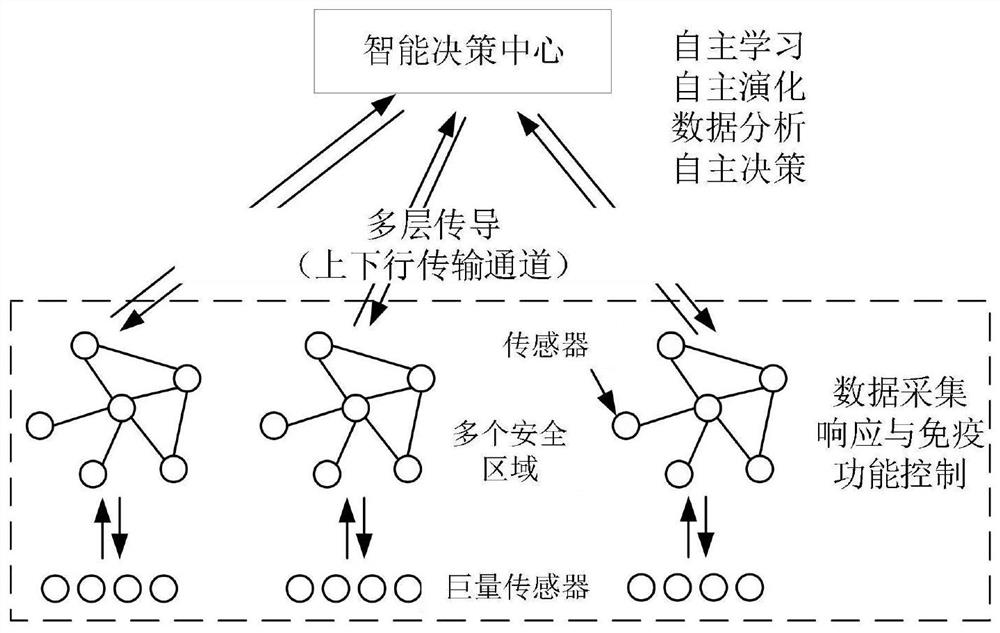
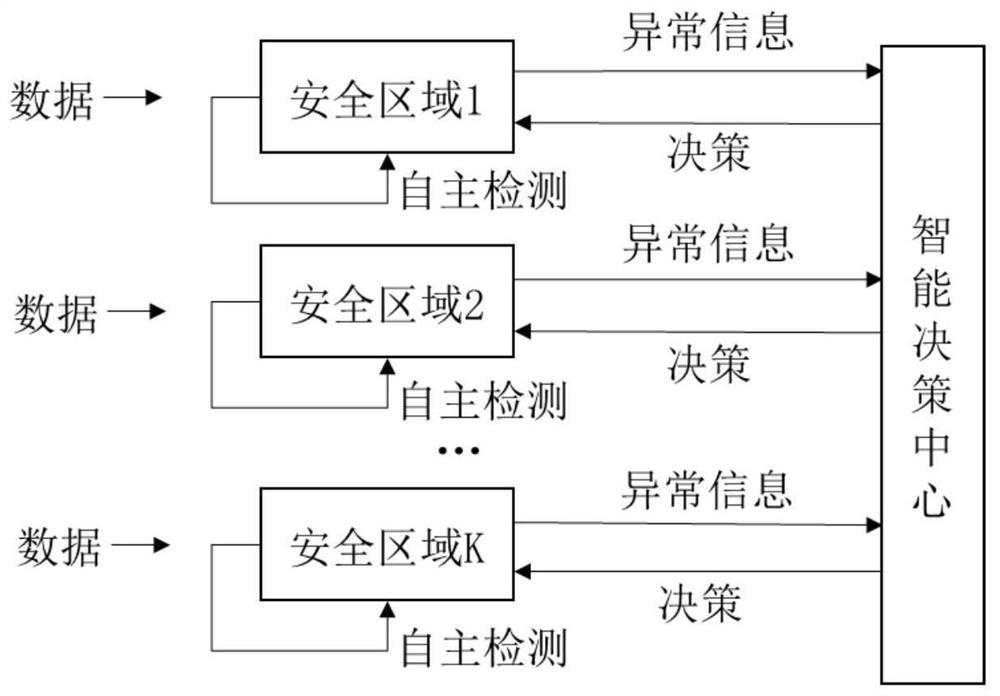
[0038] An approach for unsupervised autonomous attack detection in endogenously secure systems such as figure 1 As shown, the attack on the target node is to change some attributes of the node by perturbing a certain node on the graph.
[0039] Such as figure 1 As shown, the change to the system structure is to change the overall structure of the graph by applying disturbance to the overall structure of the graph. The disturbance to the graph structure includes ad...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More