Network security equipment based on NAT method
A technology of network security and conversion method, applied in the field of network security equipment, can solve the problems of large size of the security router, no dustproof, anti-collision, damage to the security router, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
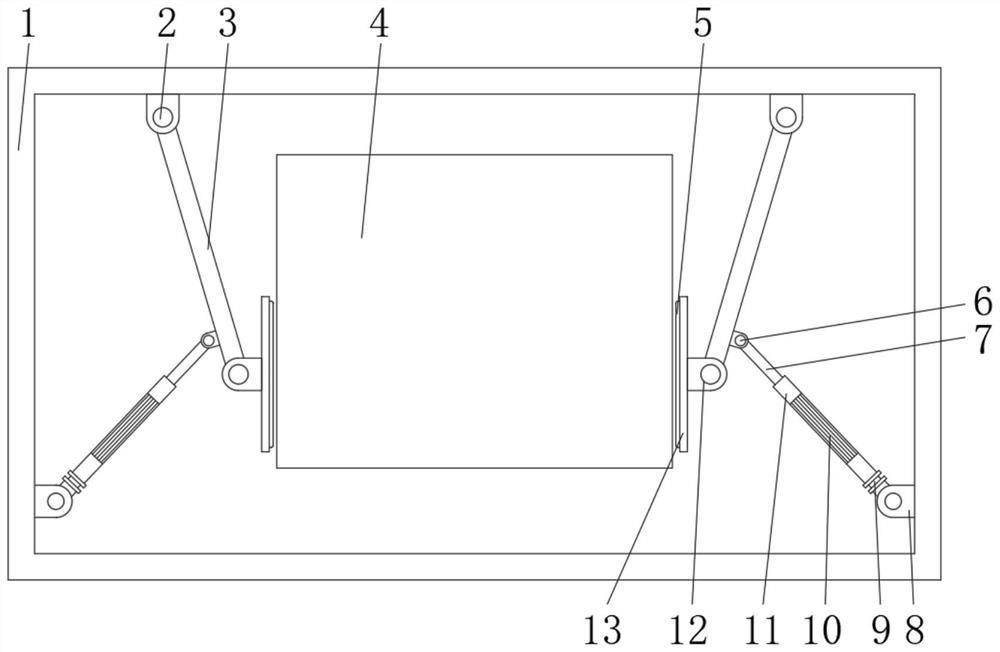
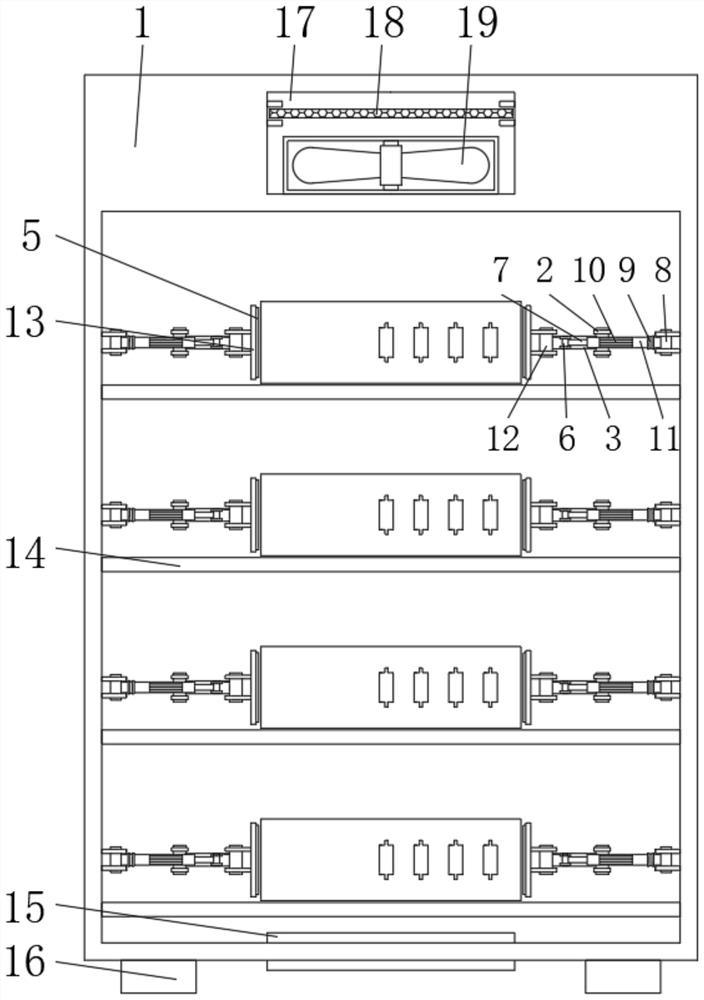
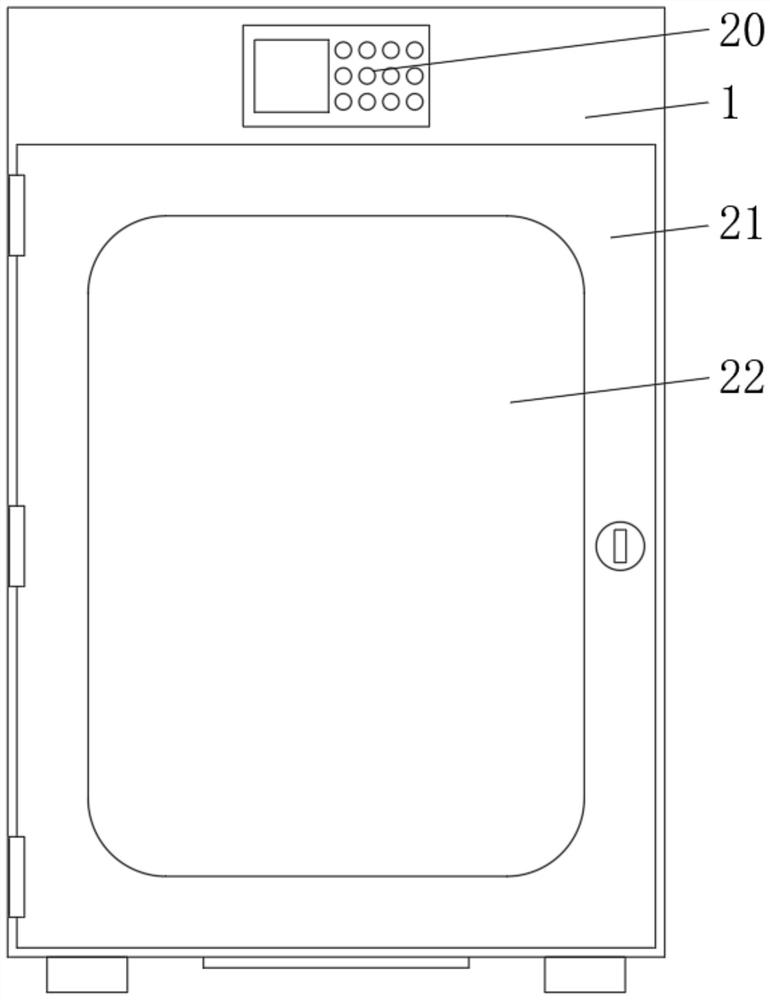
[0032] The following is attached Figure 1-4 The principles and features of the present invention are described, and the examples given are only used to explain the present invention, and are not used to limit the scope of the present invention. In the following paragraphs the invention is described more specifically by way of example with reference to the accompanying drawings. Advantages and features of the present invention will be apparent from the following description and claims. It should be noted that all the drawings are in a very simplified form and use imprecise scales, and are only used to facilitate and clearly assist the purpose of illustrating the embodiments of the present invention.
[0033] It should be noted that when a component is said to be "fixed" to another component, it can be directly on the other component or there can also be an intervening component. When a component is said to be "connected" to another component, it may be directly connected to ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More