A quantum-based privacy protection method for content-centric networks
A content-centric network and privacy protection technology, applied in key distribution, can solve the problems of easy leakage of privacy, insecure transmission channel, and inability to analyze ciphertext, etc., to achieve the effect of ensuring integrity and privacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
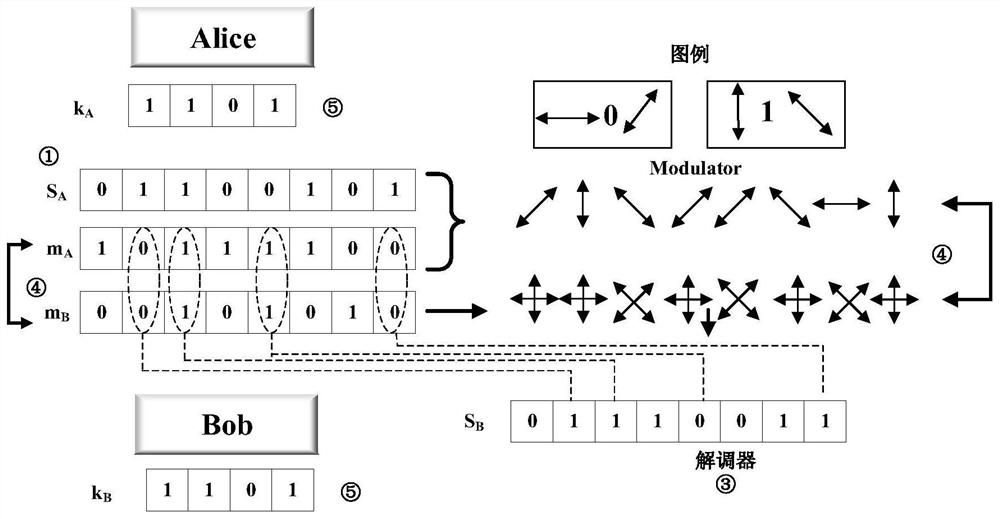
[0101] The technical solutions in the embodiments of the present invention will be clearly and completely described below with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only a part of the embodiments of the present invention, but not all of the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative efforts shall fall within the protection scope of the present invention.
[0102]Quantum cryptography was first proposed by Brassard and Benett in the 1970s. In quantum cryptography, the most striking feature is that these indivisible quantum and entangled states are directly bound by quantum mechanics. Therefore, some fundamental theorems in quantum mechanics play a crucial role in the field of quantum cryptography, these theorems include:
[0103] (1) It is impossible to obtain information from quantum st...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More