Method and system for protecting data realized by microprocessor
A microprocessor and data protection technology, applied in digital data protection, electrical digital data processing, internal/peripheral computer component protection, etc., can solve problems such as encrypted data security threats, and achieve the effect of not easy to trace
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
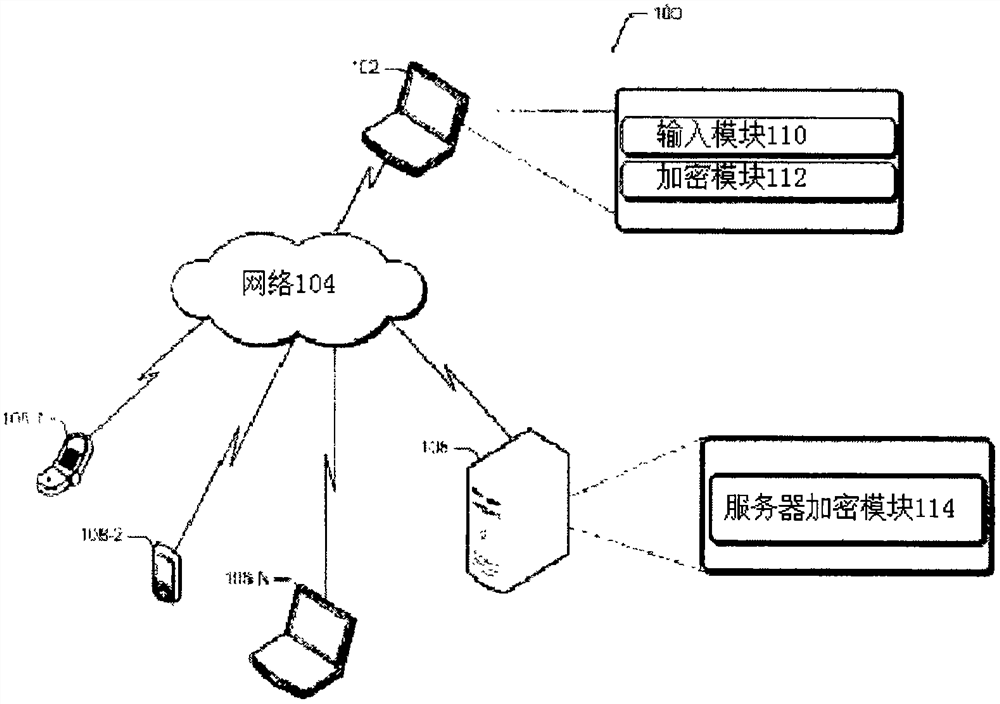
[0014] figure 1 Illustrated is a network environment 100 implementing a data security system 102 in accordance with an embodiment of the inventive subject matter. In network environment 100 , data security system 102 is connected to network 104 . In addition, a server 106 and one or more communication devices 108 - 1 , 108 - 2 , . In one example, data security system 102 may be implemented as a mainframe computer, workstation, personal computer, multi-processor system, laptop computer, network computer, minicomputer, server, or the like. Additionally, the data security system 102 may include multiple servers to perform mirroring tasks for users to alleviate congestion or minimize traffic. Additionally, data security system 102 may be connected to communication device 108 via network 104 . Examples of client devices 108 include, but are not limited to, personal computers, smartphones, PDAs, and laptop computers. The communication link between the communication device 108 an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More