Content sharing privacy protection method for resisting collusion attacks
A privacy protection and content technology, applied in the field of privacy protection, can solve the problems of low cache privacy risk and content request delay, less consideration to prevent network attacks such as collusion, and inability to resist collusion attacks, etc., to achieve low cache privacy risk and Content request delay, suitable for privacy protection, and the effect of reducing CCN energy consumption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0075] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
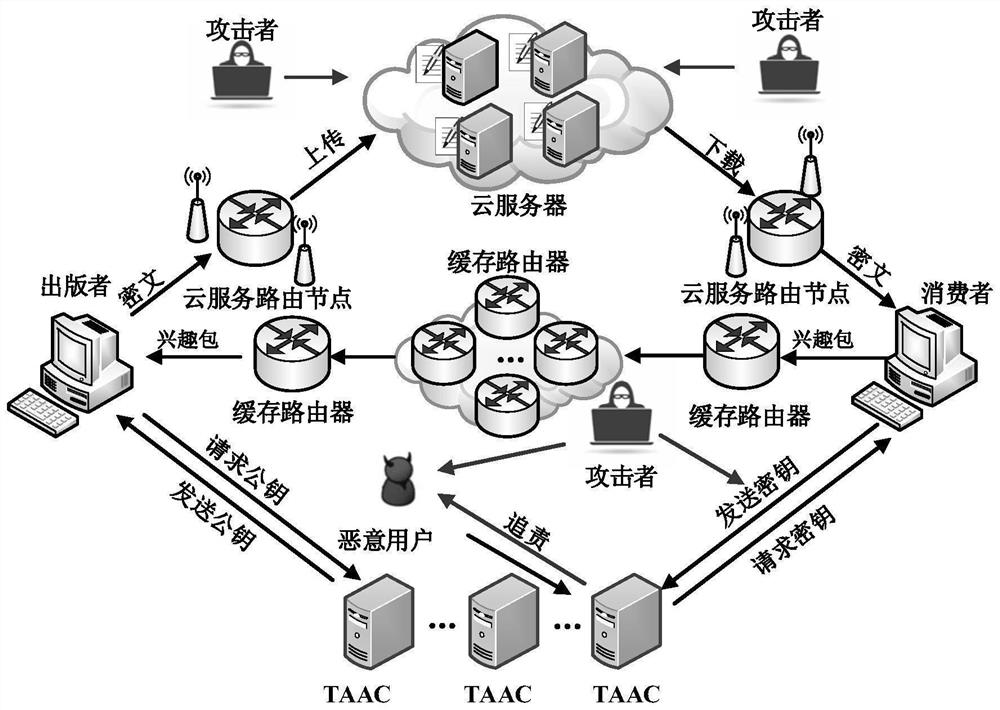
[0076] In order to overcome the security flaws of the Shahriar scheme and improve its execution efficiency, the present invention proposes a privacy protection method for content sharing that can resist collusion attacks. First, the scheme model is given, such as image 3 Shown, and then give the specific construction method, and finally, whether it can resist collusion attack is given a security proof.
[0077] Such as image 3 As shown, the entity of the pr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More