Proxy re-encryption method and system for data sharing community
A technology of proxy re-encryption and data sharing, applied in the field of blockchain community applications, it can solve the problems of troublesome data sharers and lose the meaning of cloud data sharing, achieve high traceability, solve performance bottlenecks, and improve confidentiality.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0056] The specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. The following examples are used to illustrate the present invention, but are not intended to limit the scope of the present invention.
[0057] buy example one
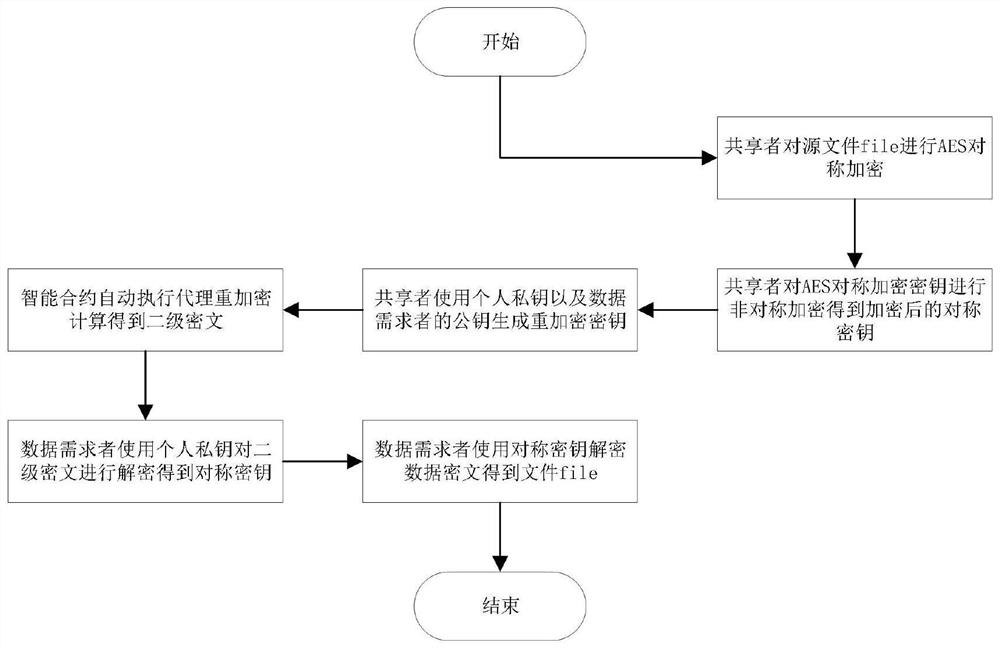
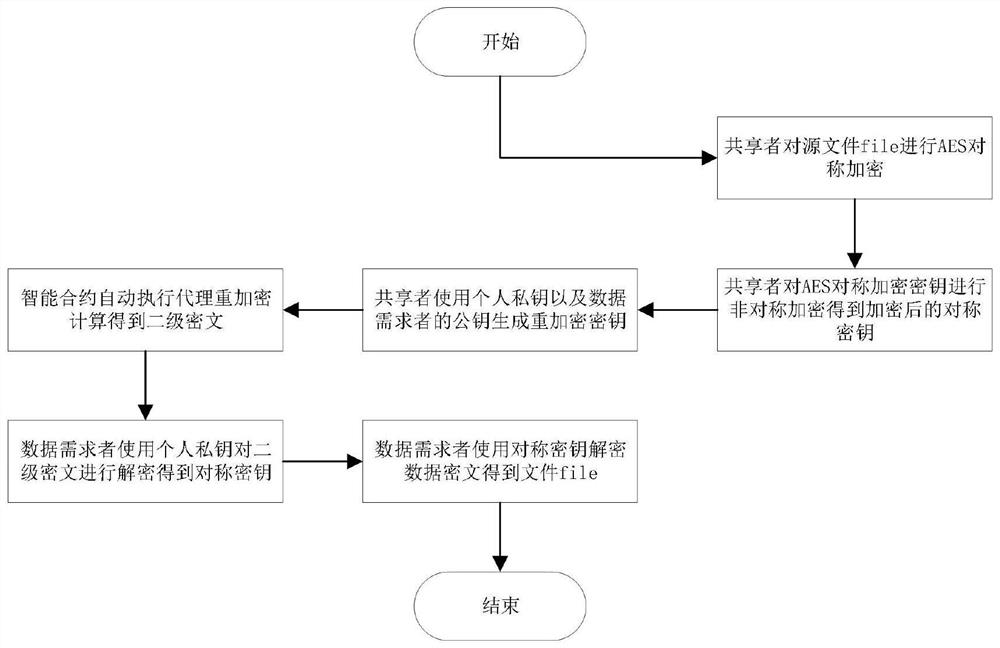
[0058] see figure 1 , a proxy re-encryption method used in the data sharing community. In the data sharing community, the proxy re-encryption technology is applied in two processes, namely data encryption and data decryption. This embodiment involves the application of proxy re-encryption technology in the community. The specific steps of data encryption and decryption are as follows:
[0059] Step 1: Sharer A uses the AES symmetric key S generated by the encryptor to use the data file file offline locally sysKey Perform data encryption, and the encrypted data ciphertext F sysEn , as shown in formula (1):
[0060] f sysEn =E AESencryption (f...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More