SM9-based key policy attribute-based encryption method
An attribute-based encryption and policy technology, which is applied in the field of information security, can solve the problems of inability to realize fine-grained access control of data, and achieve high efficiency, strong security, and the effect of protecting information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0059] In order to make the purpose, technical solutions and advantages of the embodiments of the present application clearer, the technical solutions in the embodiments of the present application will be clearly and completely described below in conjunction with the drawings in the embodiments of the present application.
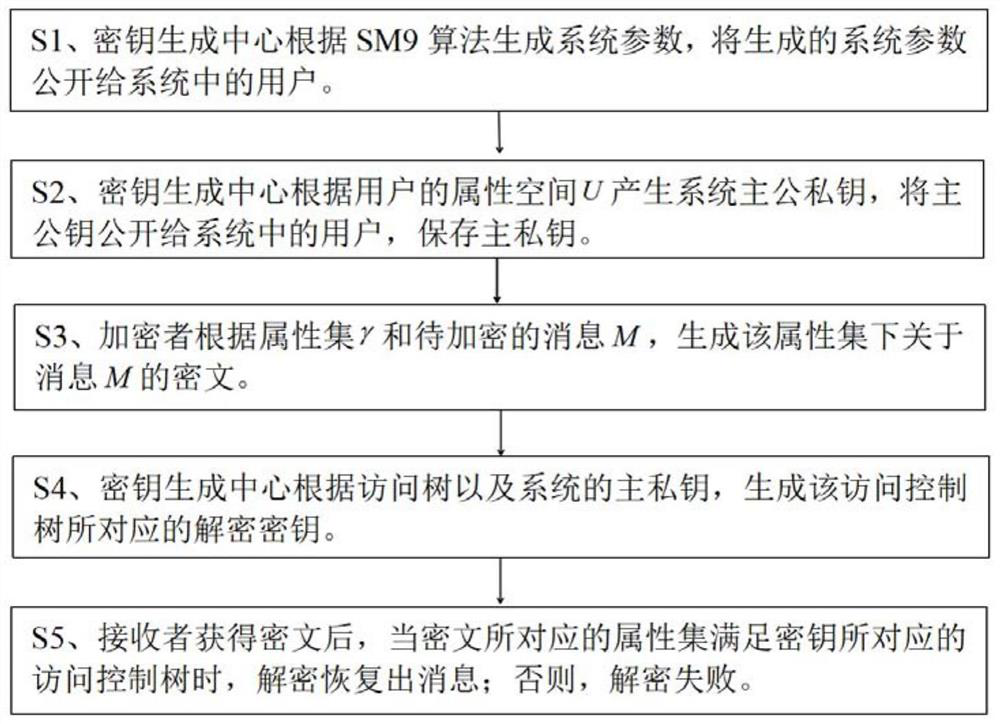
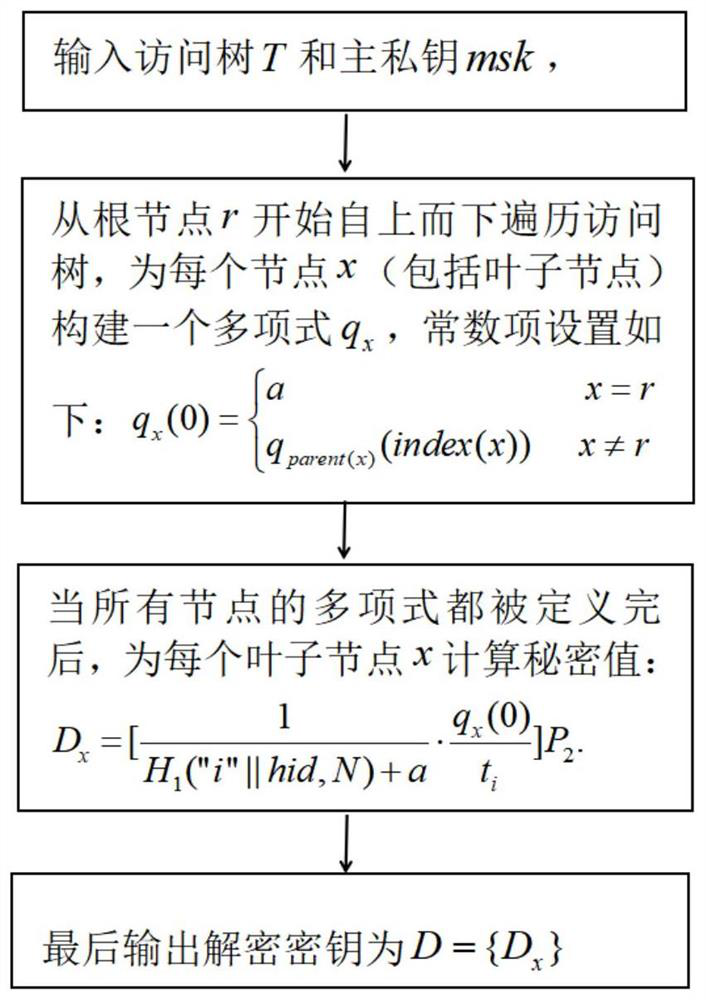
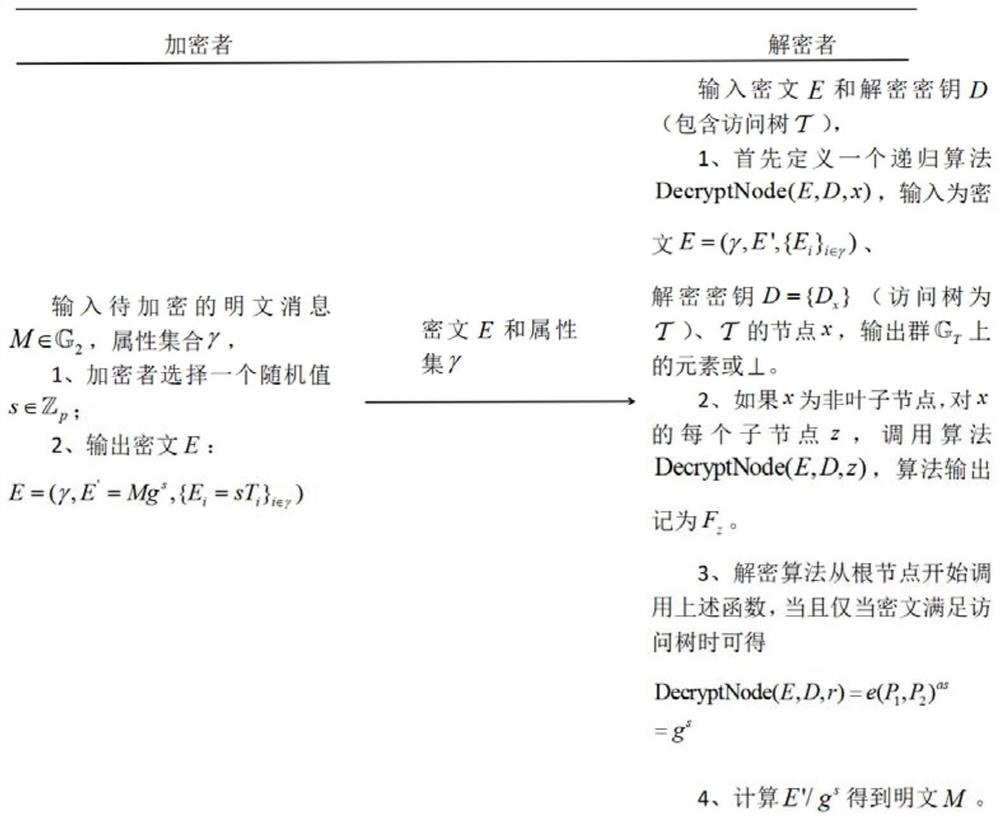
[0060] Such as Figure 1 to Figure 3 As shown in one of the above, the most critical idea of the present invention is: combining the SM9 identification encryption algorithm, representing the user's identification as a set of descriptive attributes, by associating the user's key with the access control tree, the encrypted ciphertext and properties for fine-grained access control of encrypted data.
[0061] Please refer to figure 1 , a SM9-based key policy attribute-based encryption method, which comprises steps:
[0062] S1. The key generation center generates system parameters according to the SM9 algorithm, and discloses the generated system parameters...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More