Verifying method and system based on general weight discrimination framework
An authentication method and framework technology, applied in the direction of user identity/authority verification, radio/induction link selection arrangement, selection device, etc. The effect of reducing the burden of storage and encryption and decryption operations, ensuring reliability, and improving generality
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0058] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0059] In the present invention, the service entity and the EAC perform mutual authentication and key negotiation based on the public key mechanism. After the authentication is completed, the service entity and the EAC generate Ks for protecting the service communication between the service entity and the EAC.
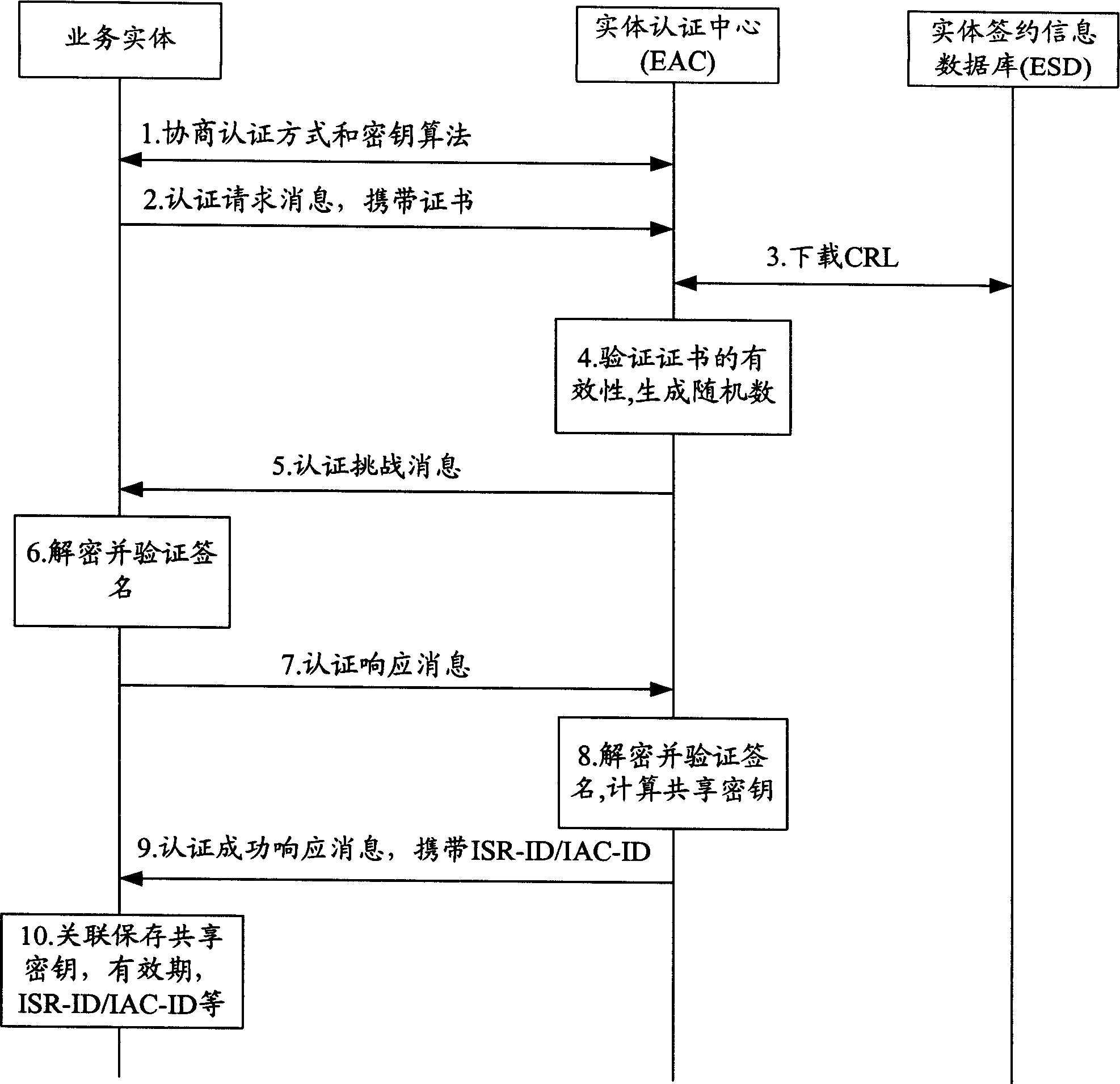
[0060] figure 2 It shows the implementation process of mutual authentication and key agreement between the business entity and the EAC in the first embodiment of the present invention, and the specific content is as follows:
[0061] 1. The business entity negotiates with the EAC to deter...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More