Method and system for protecting security of Internet by simulating biological neural network
A neural network and Internet technology, which is applied in the field of protecting Internet information security and simulating biological neural network to protect Internet security. The effect of improving the response speed
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0066] The specific implementation manner of the present invention will be described below in conjunction with the accompanying drawings.
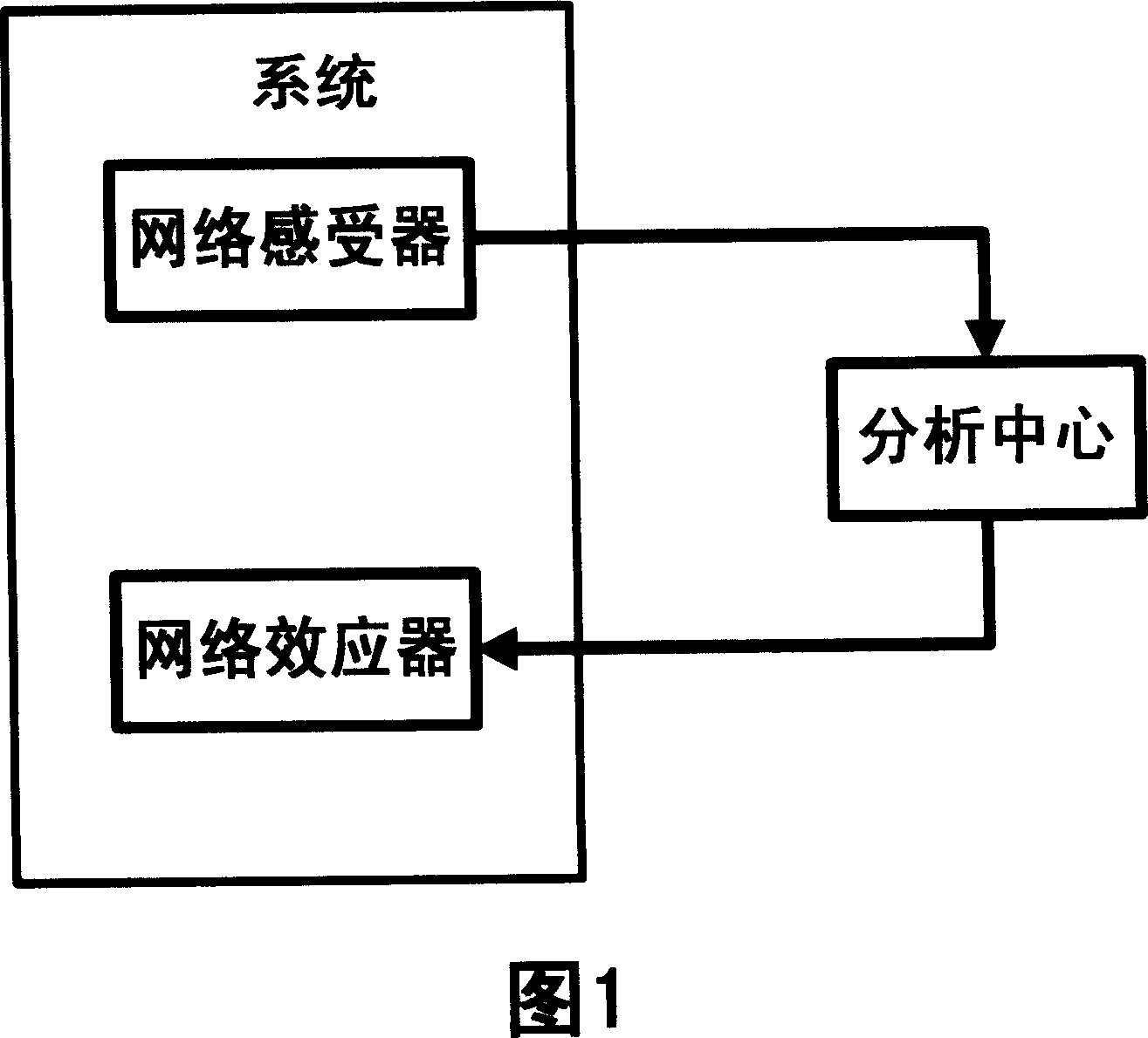
[0067] Fig. 1 is a system structure diagram of the present invention, the first part is the network sensor, the second part is the analysis center, and the third part is the network effector. Different from Update collecting local version information and Bug information, the network sensor part monitors and collects activity information and content-related information of local network communication in the present invention, and sends them to the information analysis center. Unlike Update, which downloads patches or libraries on the server, the analysis center will use the knowledge accumulated by the center to analyze the data submitted by the network sensor. If the data submitted by the network sensor has attack characteristics or contains prohibited information, the analysis center will instruct Shut down part or all of the connections o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More