Malware detection system and method for mobile platforms
a malware detection and mobile platform technology, applied in the direction of wireless communication, unauthorized memory use protection, instruments, etc., can solve the problems of cumbersome and time-consuming re-assembling and uncompressing such data packets, inability to obtain the entire data, and difficulty in efficiently implementing comprehensive signature matching as virus or malware detection method on memory-constrained devices, such as mobile phones
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
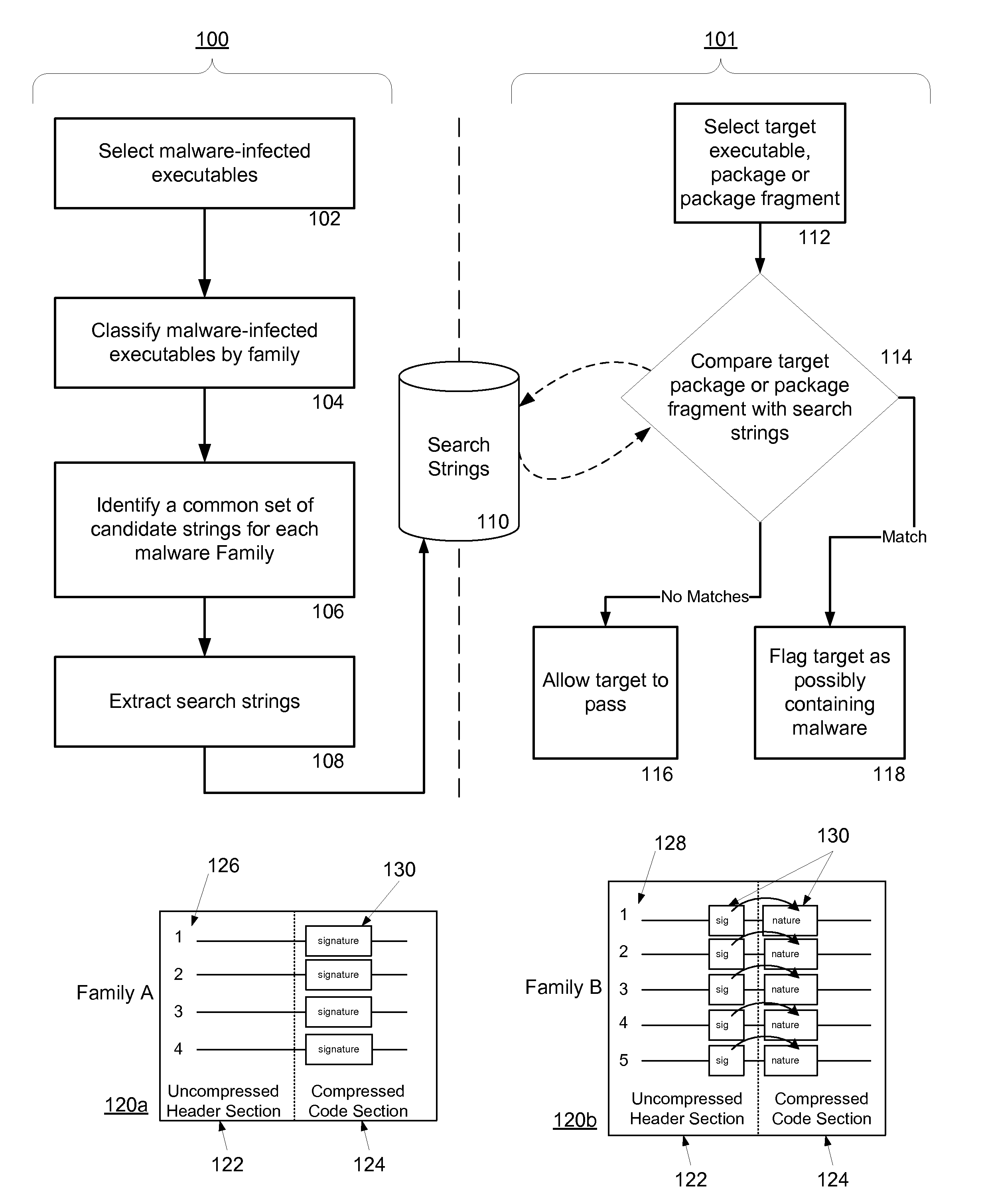
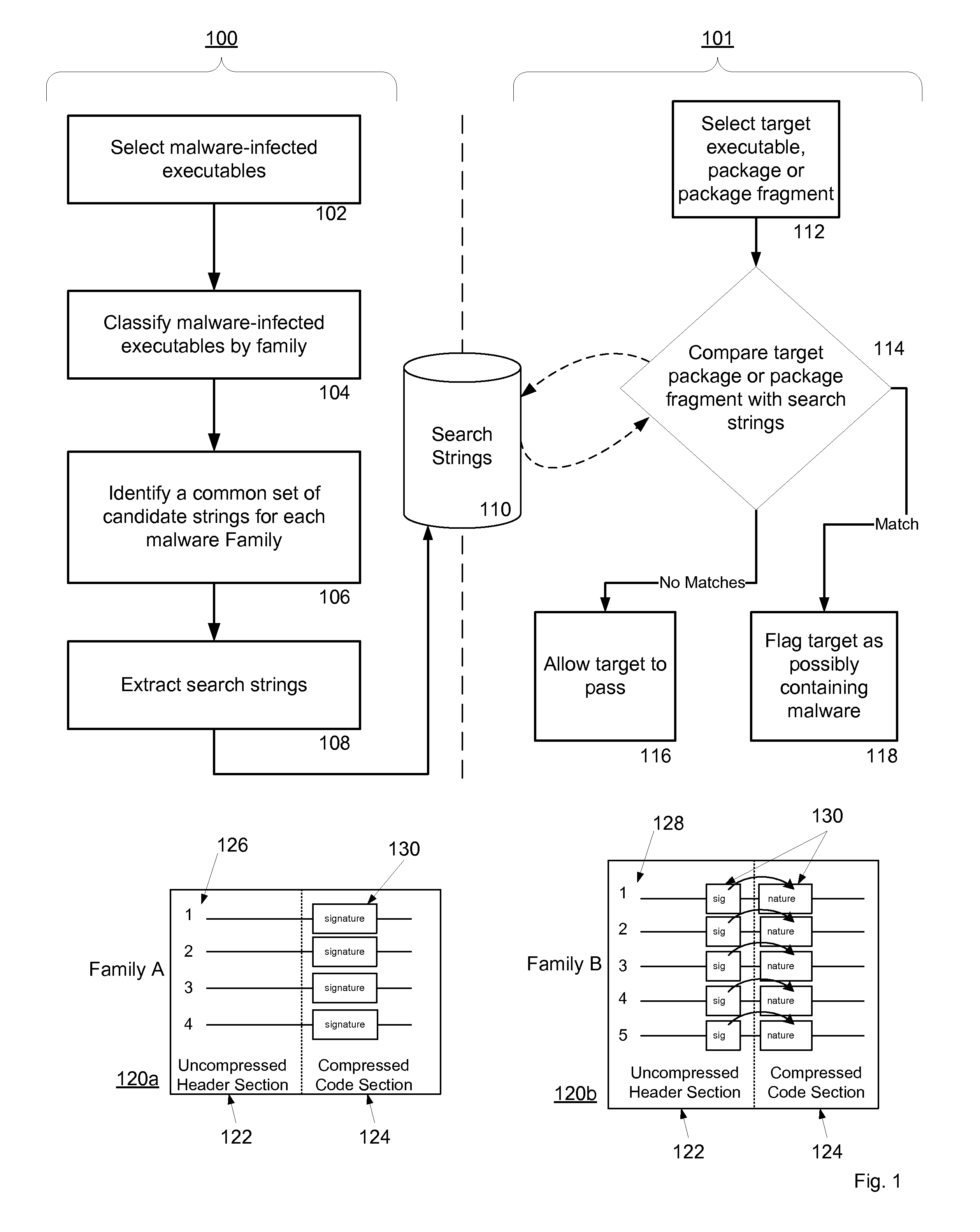
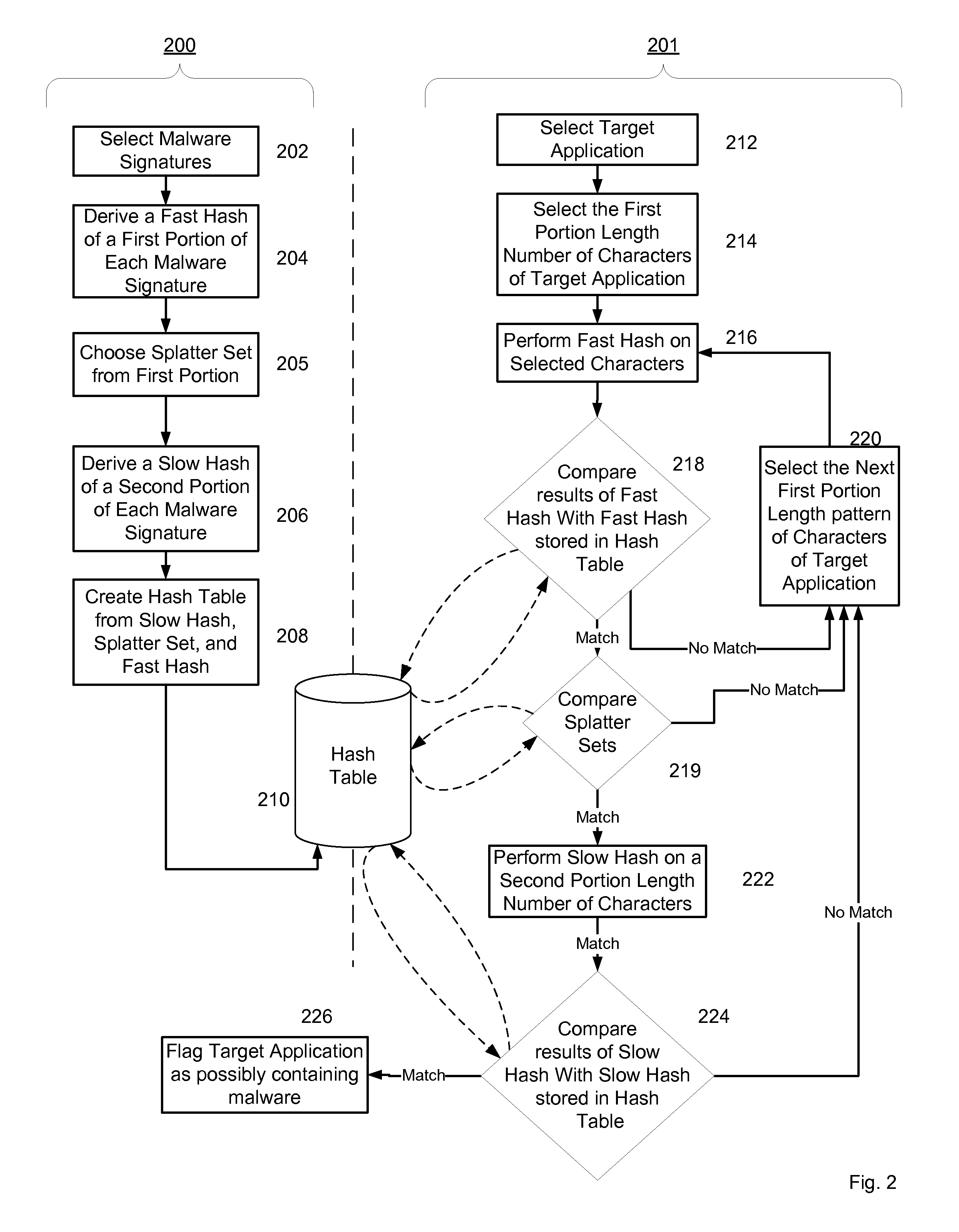
[0042]Exemplary embodiments of the present invention are detailed in FIGS. 1-15.
Malware Signature Detection Using a Mobile Application's Header and Compressed Code
[0043]Mobile applications are transported to mobile platforms across mobile networks using software installation files or SIS packages in the case of Symbian®, and CAB packages in the case of Windows Mobile®. These data packages are compressed before being sent across the mobile network and due to their large size they are often fragmented by the network in the process of being transported. The following detailed description discloses a method and system for detecting malware in these compressed and fragmented data packages without necessitating concatenating all the fragments back together or first decompressing the package in its entirety on a receiving mobile platform. For convenience, a mobile platform is a mobile telephone, a smart phone, a mobile computing device, a smart handheld device, a network element, or any co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More