Security monitoring service recovery method and system
A technology of security monitoring and recovery method, applied in the field of network communication, can solve the problems of client discarding, inconvenient maintenance, user inconvenience, etc., and achieve the effect of recovering security monitoring services
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0062] The technical solutions of the present invention will be described in further detail below with reference to the accompanying drawings and embodiments.
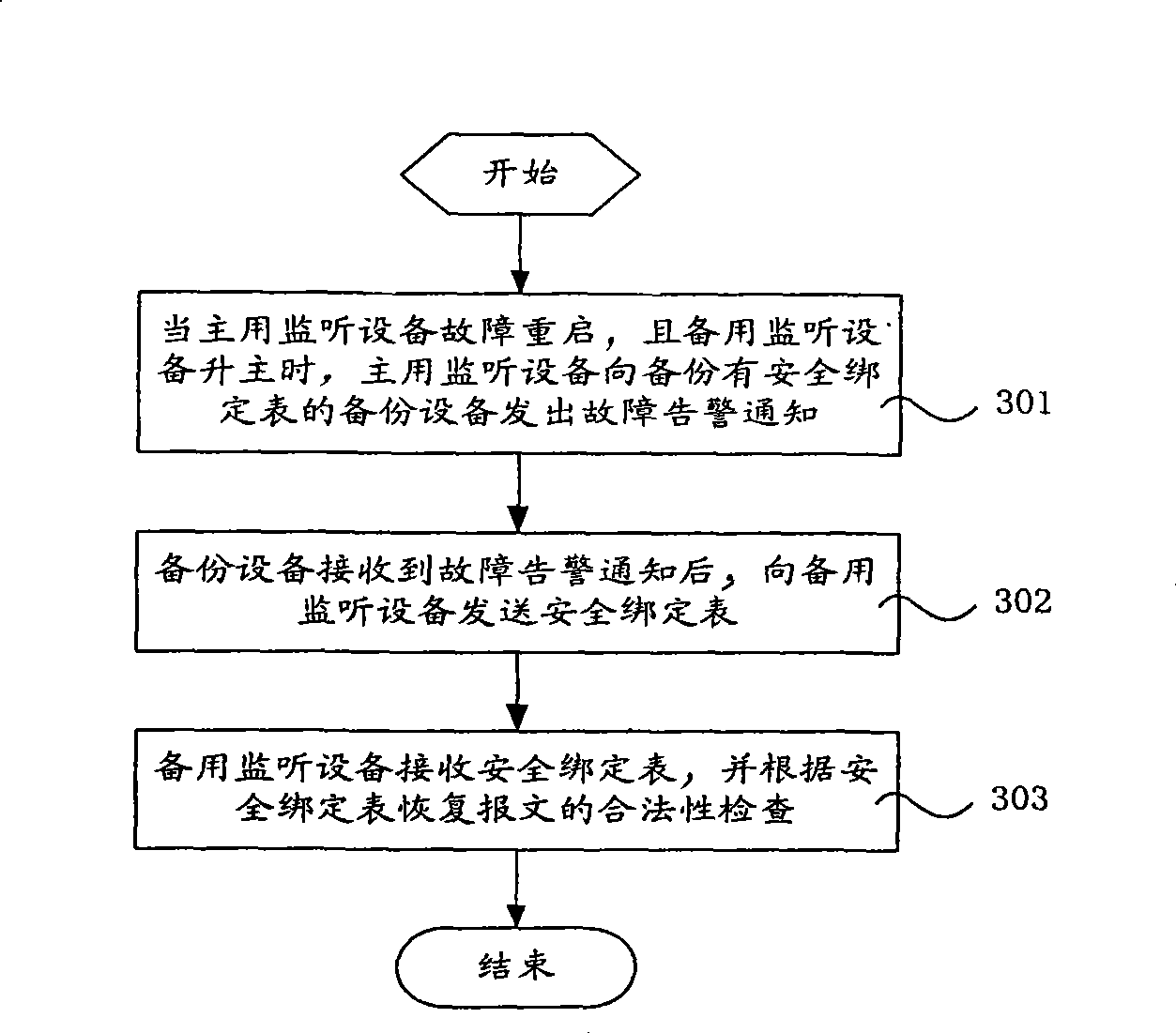
[0063] The present invention backs up the security binding table of the monitoring device through the backup device, and sends the backup security binding table to the monitoring device that continues the original business after the backup device fails, so as to quickly restore the security monitoring service on the monitoring device, Ensure the safety of users using services.
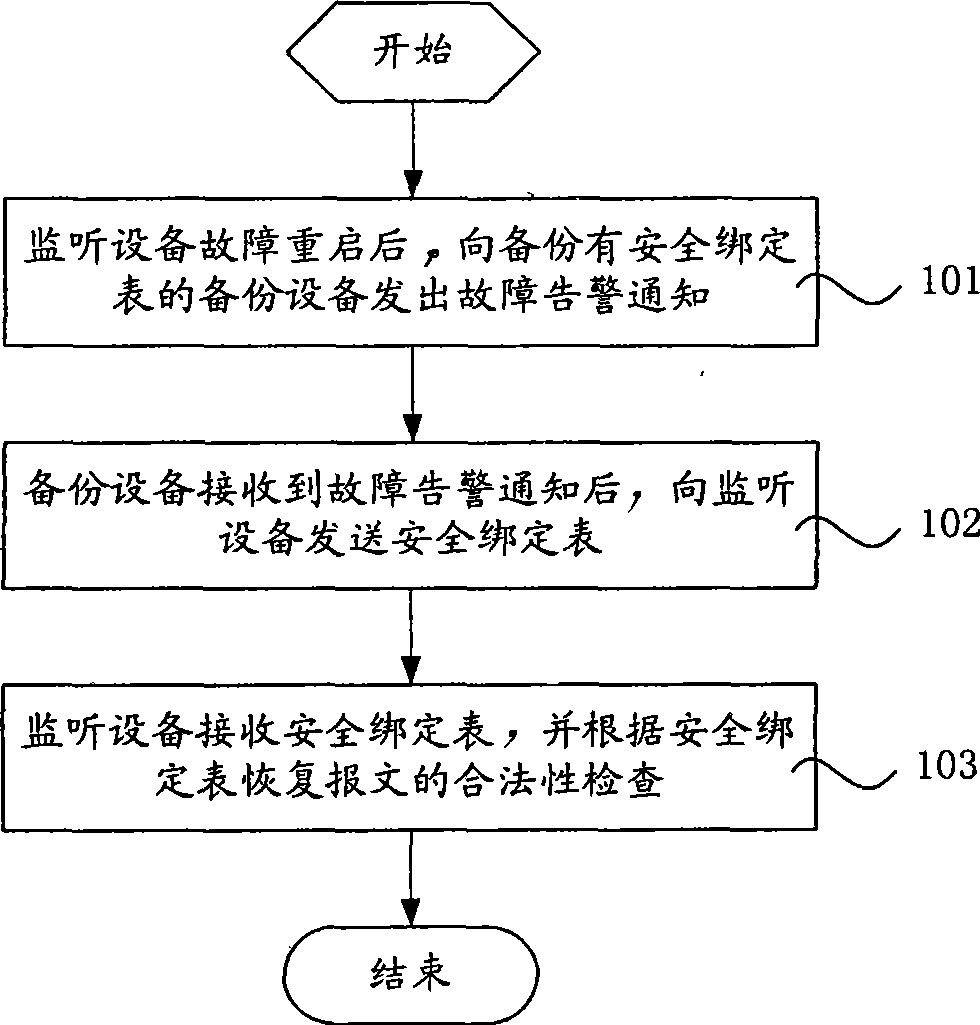
[0064] Such as figure 1 As shown, it is a schematic flow chart of an embodiment of the method for restoring the security monitoring service under the single-unit network of the present invention. This embodiment includes the following steps:
[0065] Step 101, after the monitoring device fails and restarts, send a fault alarm notification to the backup device with the backup security binding table;
[0066] Step 102, after the backup device r...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More