Method and system for detecting malicious codes based on uniform resource locator
A malicious code detection and resource locator technology, which is applied in the fields of instruments, electrical digital data processing, computer security devices, etc., to achieve the effect of simple use, good detection rate, and improved detection rate
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the above-mentioned purposes, features and advantages of the present invention more obvious and easy to understand, the technical solutions in the present invention will be further detailed below in conjunction with the accompanying drawings illustrate.
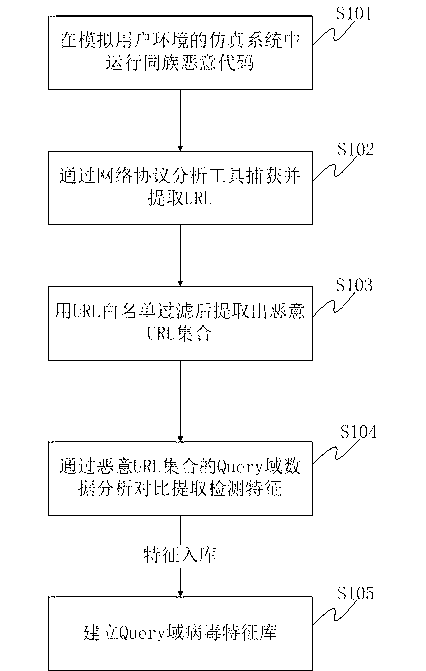
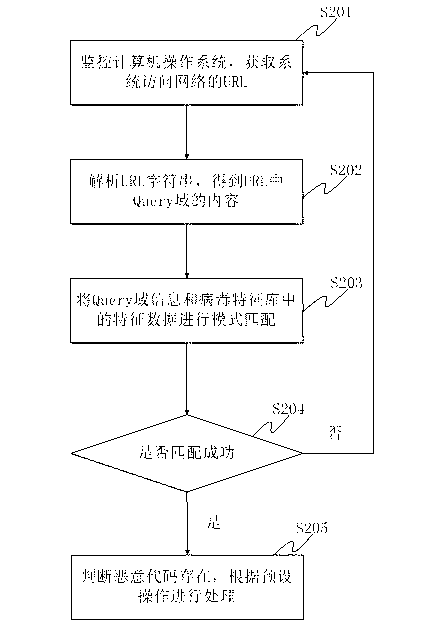
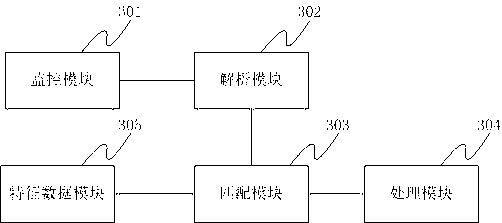
[0047] like figure 1 As shown, a method for extracting malicious code signatures based on uniform resource locators is provided, including:
[0048] S101: Put the malicious code of the same family into a simulation system (virtual machine or honeypot, including an environment that provides a trigger for normal operation of the malicious code) that simulates the user environment to run.
[0049] S102: The network communication data generated after the malicious code runs is captured and analyzed by a network protocol analysis tool, and the URL data therein is collected. The ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More