Identity-based safety signature method
A security signature and identity technology, applied in security devices, electrical components, wireless communications, etc., can solve problems such as insufficient computing power, small storage space, and limited power supply
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0052] The present invention will be further described in conjunction with the following specific embodiments. The specific examples are to further describe the present invention in detail, without limiting the protection scope of the present invention.
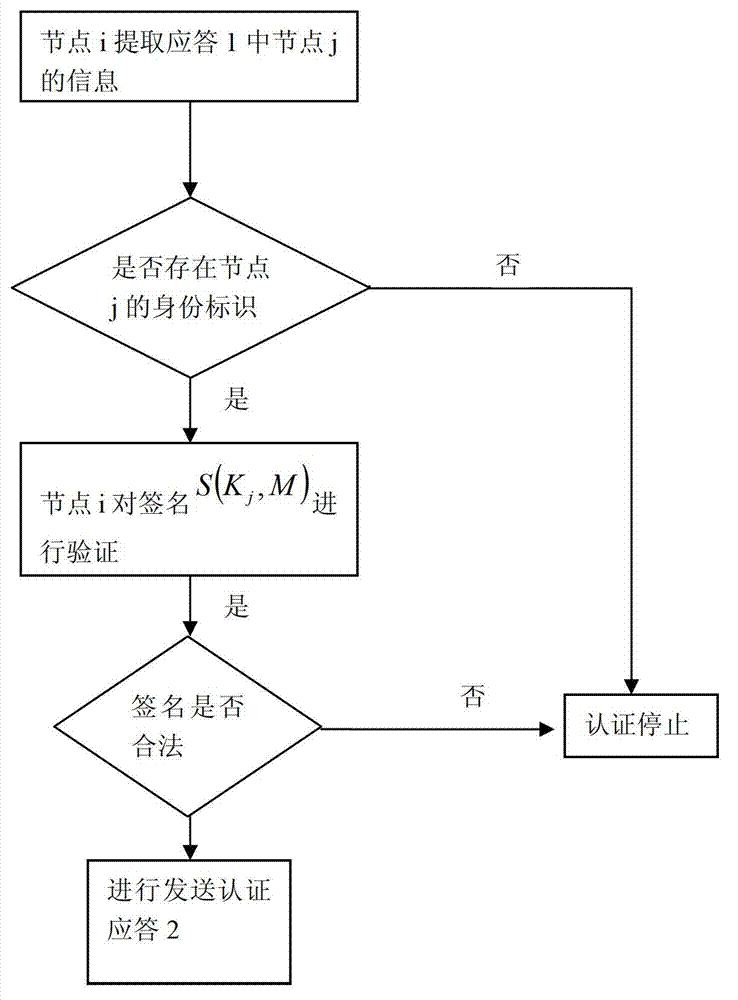
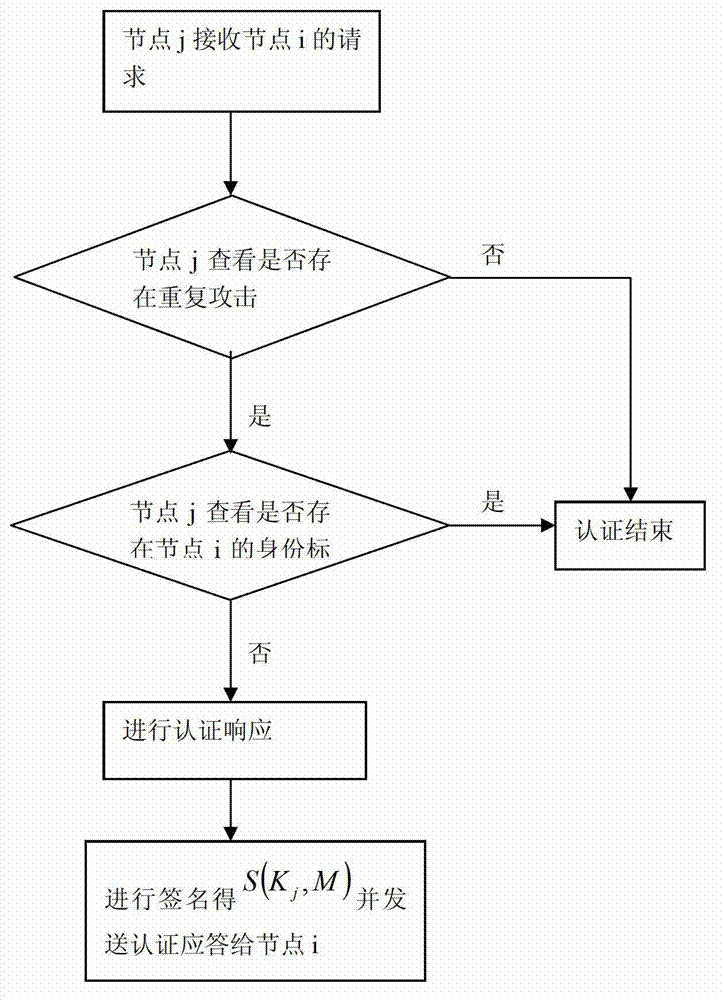
[0053] An identity-based secure signature method, comprising the steps of:
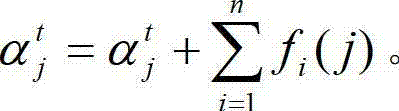
[0054] (1) Offline key distribution, generate system parameters and master key: run the nodes in the system, generate parameter k, calculate elliptic curve E(Fp), and calculate output is {q,G 1 ,G 2 ,e,g,g 1 ,h,α}, where q is a prime number, input k to generate a large prime number Q, and establish two groups with order Q: additive cyclic group G 1 , and the multiplicative cyclic group G 2 Making the CDH problem difficult, build a bilinear map e:G 1 ×G 1 →G 2 , arbitrarily choose a generating element p∈G 1 ; Then the master key of the system is generated by the nodes in the system System public parameters g,h∈G 1 , g 1 =g α ∈G 2 and the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More