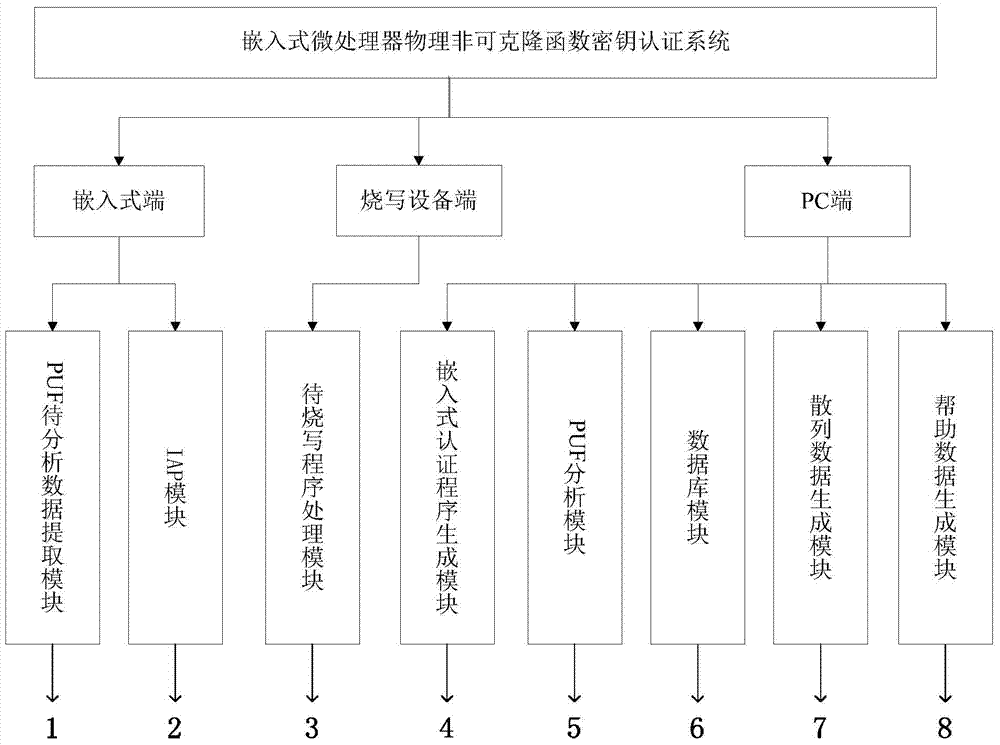
Embedded microprocessor unclonable function secret key certification system and method
A microprocessor and key authentication technology, applied in the direction of electrical digital data processing, instruments, calculations, etc., can solve the problems of lack of independent intellectual property rights, use restrictions, and high price of security products, so as to reduce the time of combination and reduce the cost , enhance the effect of versatility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
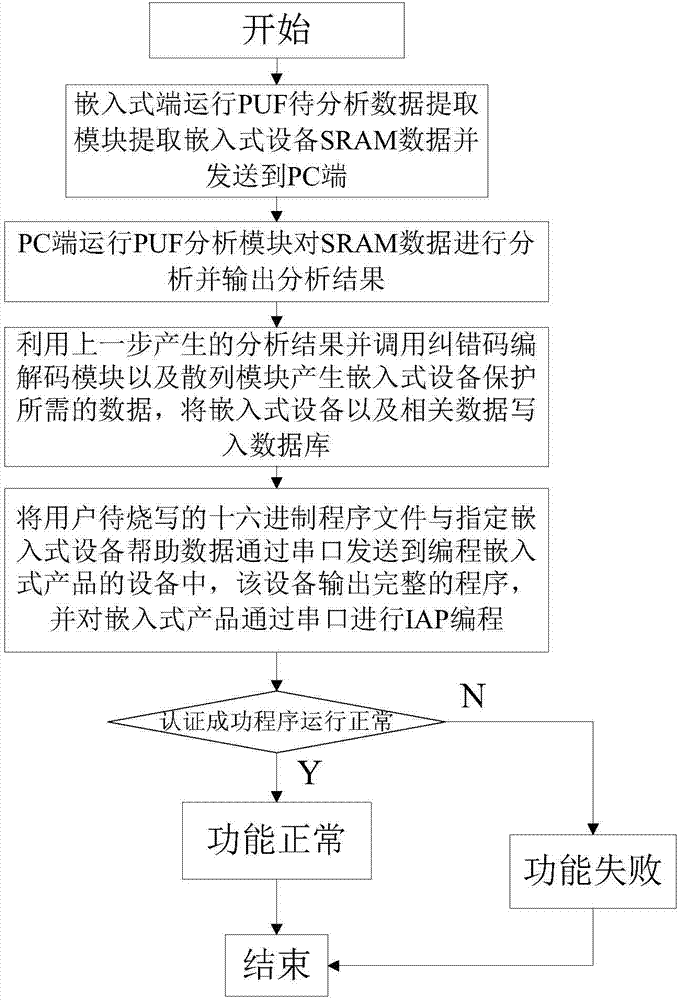
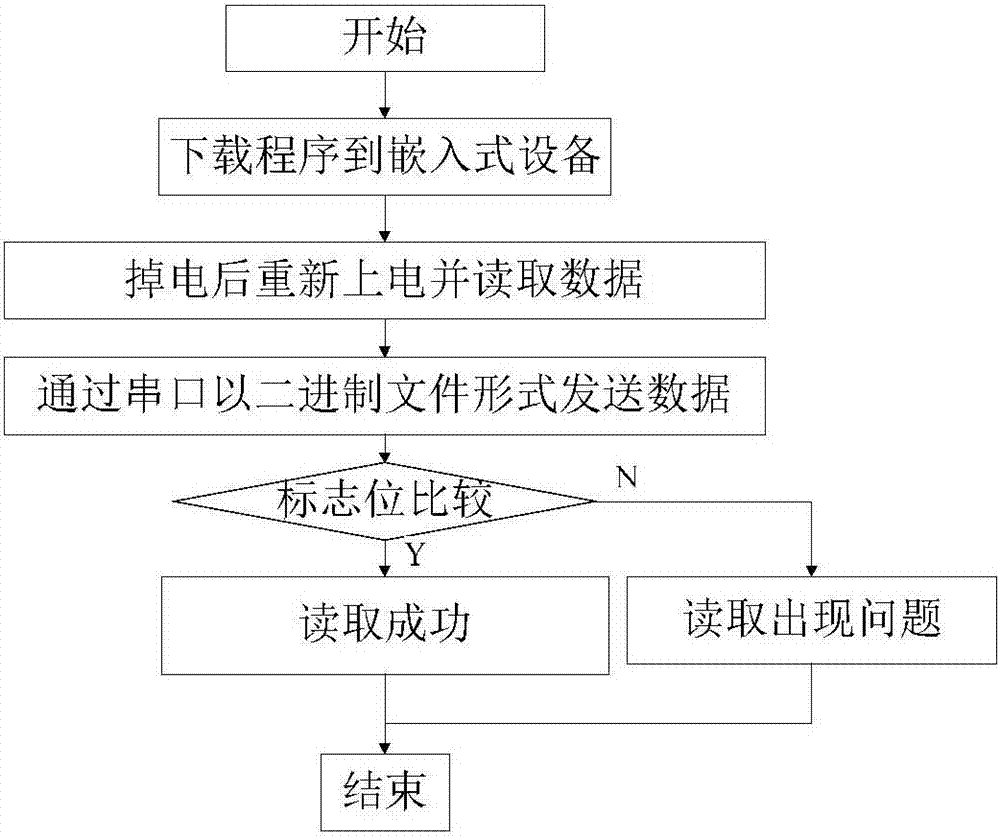
[0039] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not constitute a conflict with each other.
[0040] At present, the software of many embedded products lacks protection, or the software is encrypted by a common key encryption method. In this case, the attacker can use physical attack to physically attack the memory storing the key and easily obtain the key information, and then can copy and steal the embedded software and further threaten the security of the embedded device. Embedded so...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More