Cloud data safe deleting system and method without support of trusted third party
A cloud and data file technology, applied in the transmission system, electrical components, etc., can solve the problem of increasing the cost of hackers collecting keys or attacks, achieve encryption efficiency and data security improvement, get rid of single control, and key security protection Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] In order to make the objectives, technical solutions and advantages of the present invention clearer, the following further describes the present invention in detail with reference to the accompanying drawings and embodiments. It should be understood that the specific embodiments described herein are only used to explain the present invention, but not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not conflict with each other.
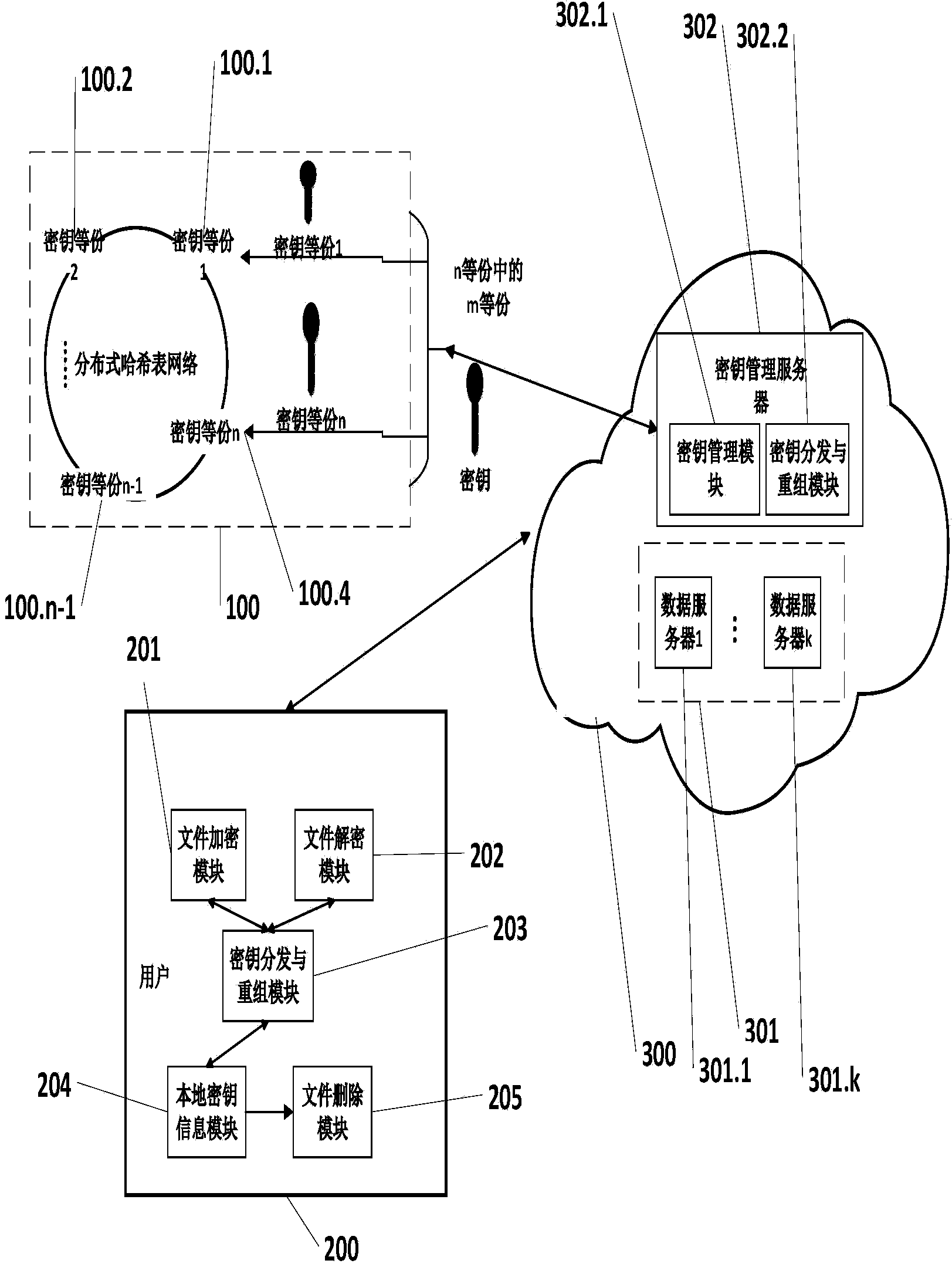
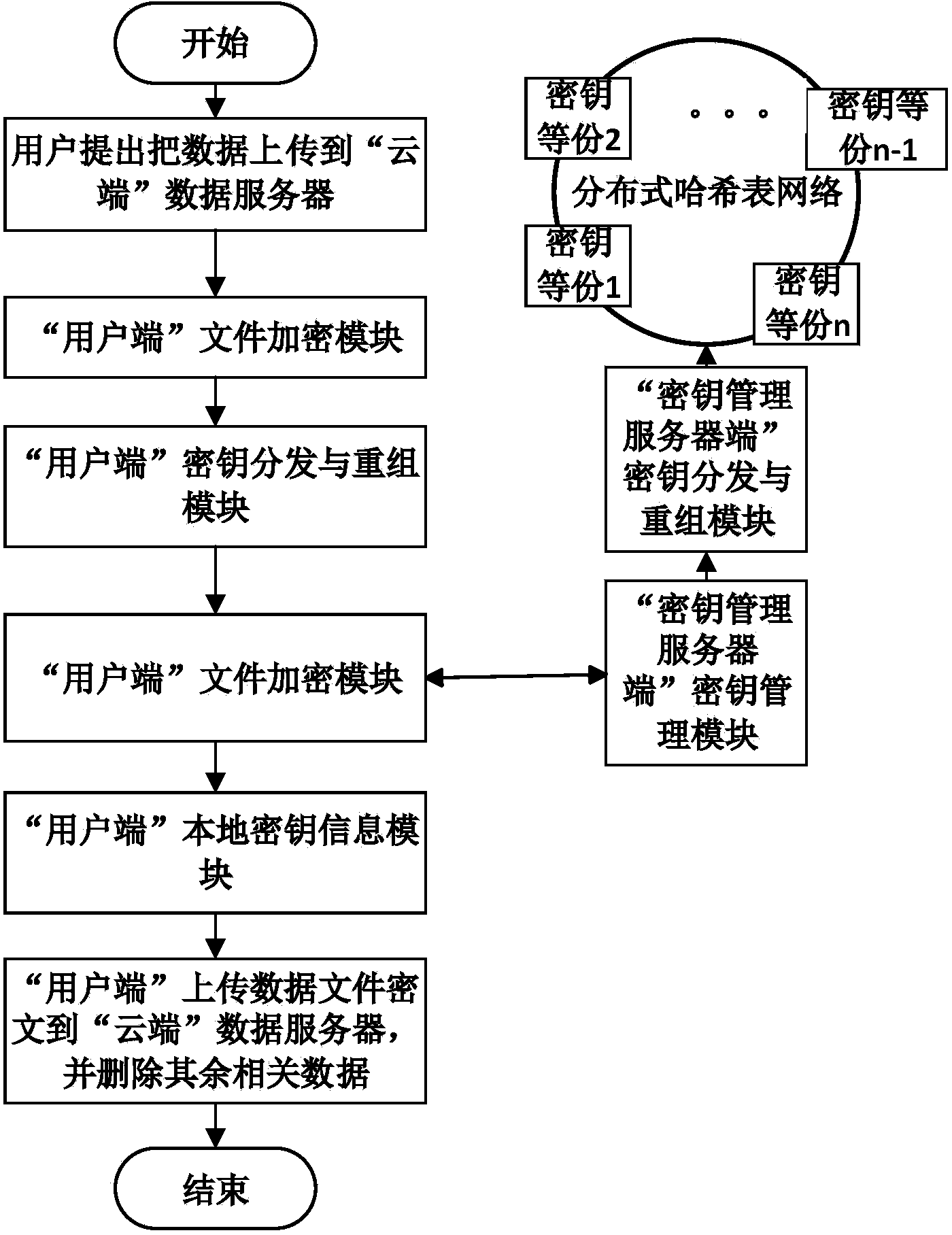
[0045] Such as figure 1 As shown, a system and method for secure deletion of cloud data without the support of a trusted third party is composed of a distributed hash table 100, a client 200, and a cloud 300. The details are as follows:
[0046] The distributed hash table 100 stores ciphertext fragments of data file decryption keys.
[0047] The client 200 is used for encrypting data files, decrypting ci...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More