Encoding encryption application method for human face information
A technology of face information and encryption method, which is applied in the direction of instruments, digital data authentication, character and pattern recognition, etc., can solve the problems of high complexity and effect to be improved, and achieve the effect of promoting development and application
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
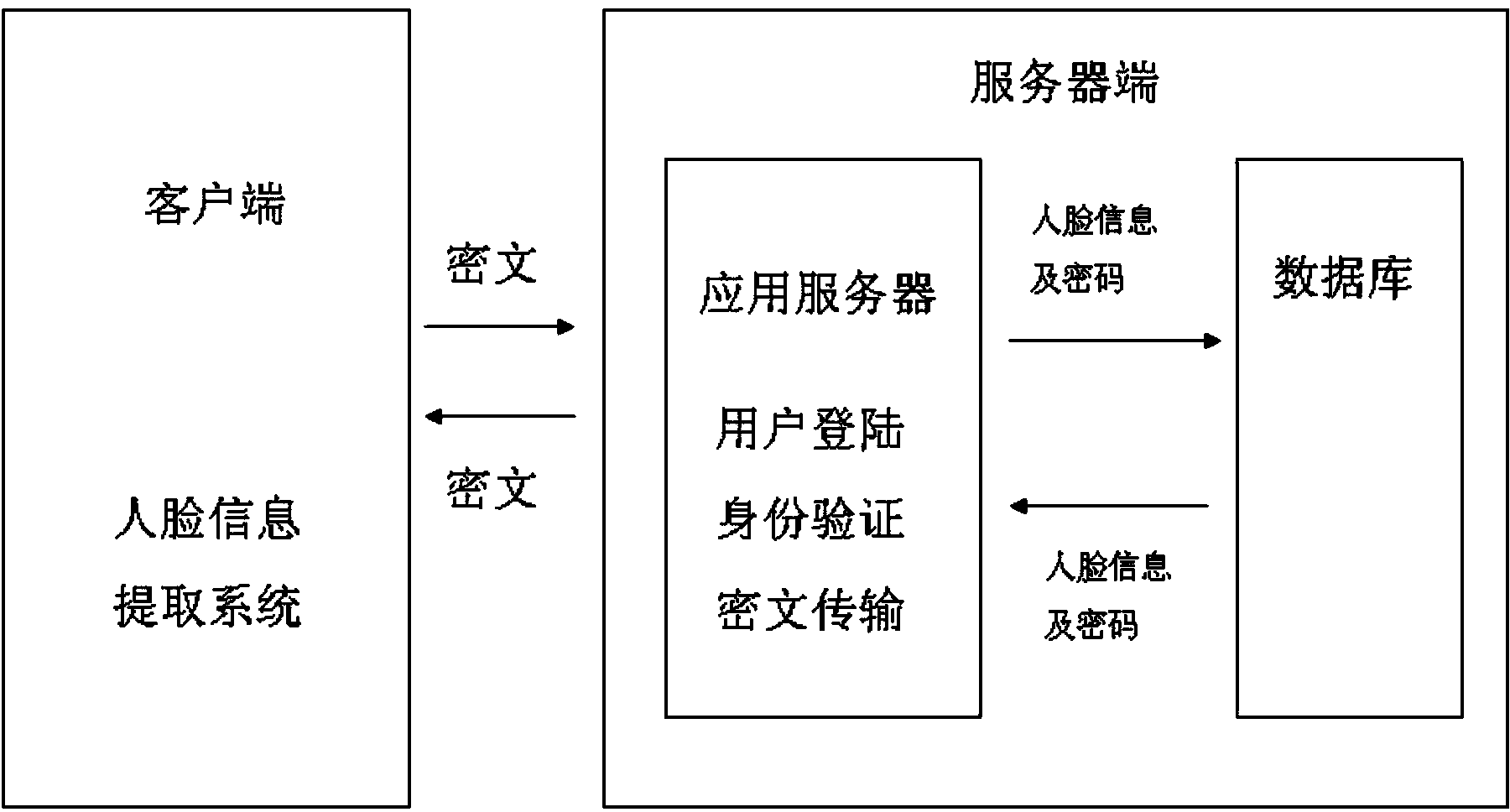
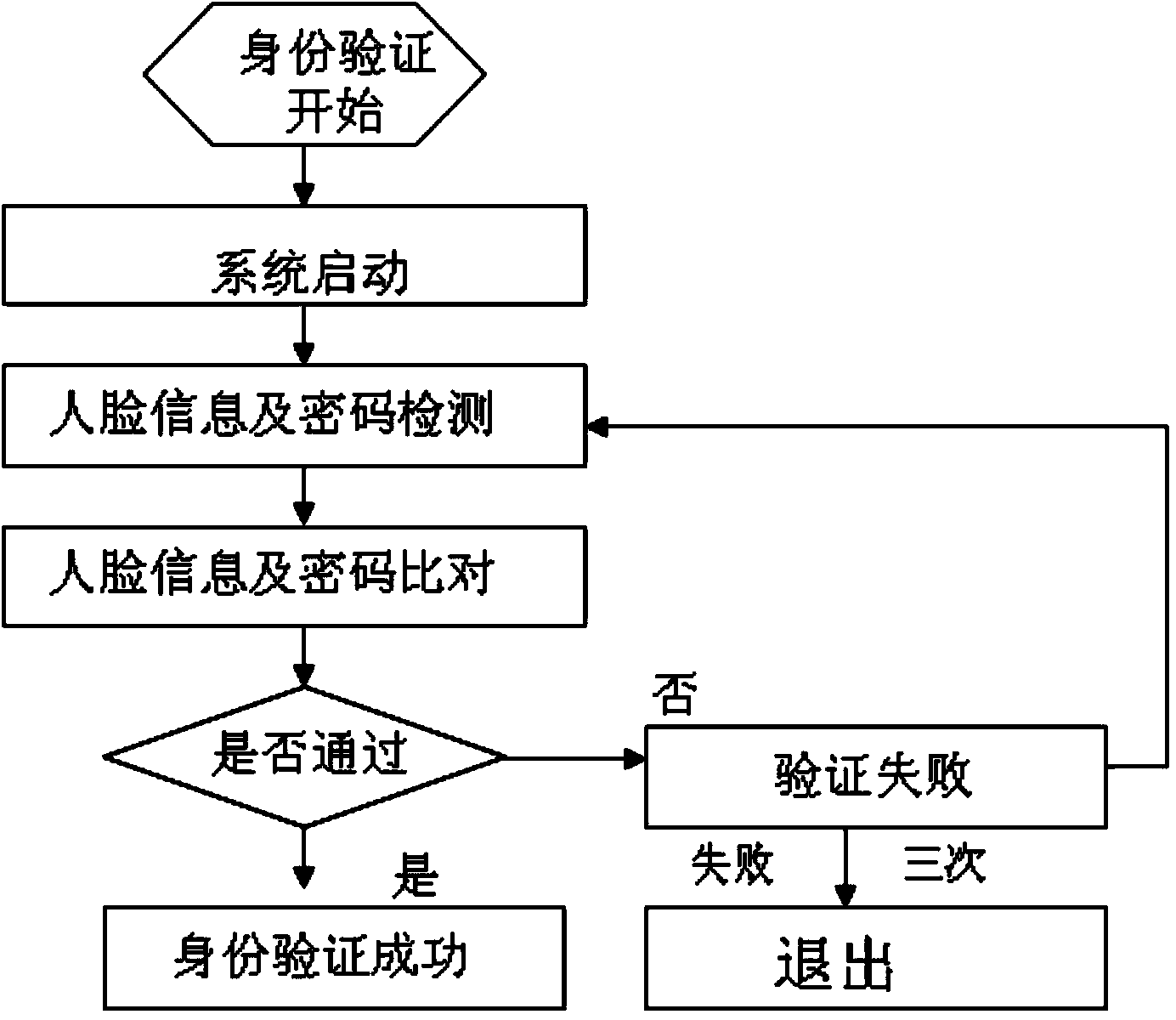
Method used
Image
Examples
Embodiment 1
[0027]User Zhang San first sets up an account in the bank and submits the face image information and the binary coding method of the selected face, which turns left to 1 and right to 0, and the identity verification password formed by three face-turning codes of 1, 0, and 1. The alarm password formed by two turns of 0, 1 and the backup password formed by six turns of 0, 1, 0, 1, 0, 1 are included in the database of the bank server. Then Zhang San needs to pay for online shopping through the client installed on the mobile phone. After logging in to the bank account, he first captures the face-turning images three times through the mobile phone camera and sends the ciphertext obtained through the symmetric encryption algorithm to the bank server. The bank server passes the three face-turning images through After feature extraction and template extraction, the face information of the three face turns is obtained. The bank server compares these face information with the face inform...
Embodiment 2
[0032] After a prison system sets up an access control system network, it first collects the face image information submitted by the prison guards and the unified coding method of turning right to 1 and turning left to 0, and the selected 1, 1, 1 authentication password , 0, 1 two face-turning alarm passwords to be included in the database of the access control system server. Prison guard A usually goes to work through the ciphertext obtained by the asymmetric encryption algorithm through the client terminal with the camera installed at each cell door of the prison, using the face image information selected by him three times and the identity verification password formed by the face encoding. Identity verification to enter and exit the prison access control system. If the prison guard is threatened by criminals, an alarm will be prompted through the face information and the alarm password formed by it twice to inform other prison guards to provide support, and the access contro...
Embodiment 3
[0034] Li Si installs an authentication system with a camera on the safe so that the safe can only be opened after successful authentication. Then Li Si submitted his face image information and the encoding method that he selected for the left-turned face and the right-turned 0, and the 1, 0, 1, 0, 1, 0 authentication password formed by six turns of face, three times The 1, 0, 1 alarm password formed by face-turning and the 0, 0, 0, 1, 1 backup password formed by 5 face-turning are recorded in the database of the safe server. At this point the client and server are merged together. When needing to open the safe behind Li Si, he can log in, verify his identity and open it through the password information formed by his selected face image information and its face rotation code.
[0035] When Li Si forgot his identity verification password, he could log in and get back or reset his identity verification password by selecting the backup password formed by the face image informati...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More