IPSEC (internet protocol security) VPN (virtual private network) device, isolation method thereof and isolation system thereof
A technology for isolating systems and equipment, applied in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be described in further detail below with reference to the accompanying drawings and embodiments. It should be understood that the specific implementations described here are only used to explain the present invention, not to limit the present invention.
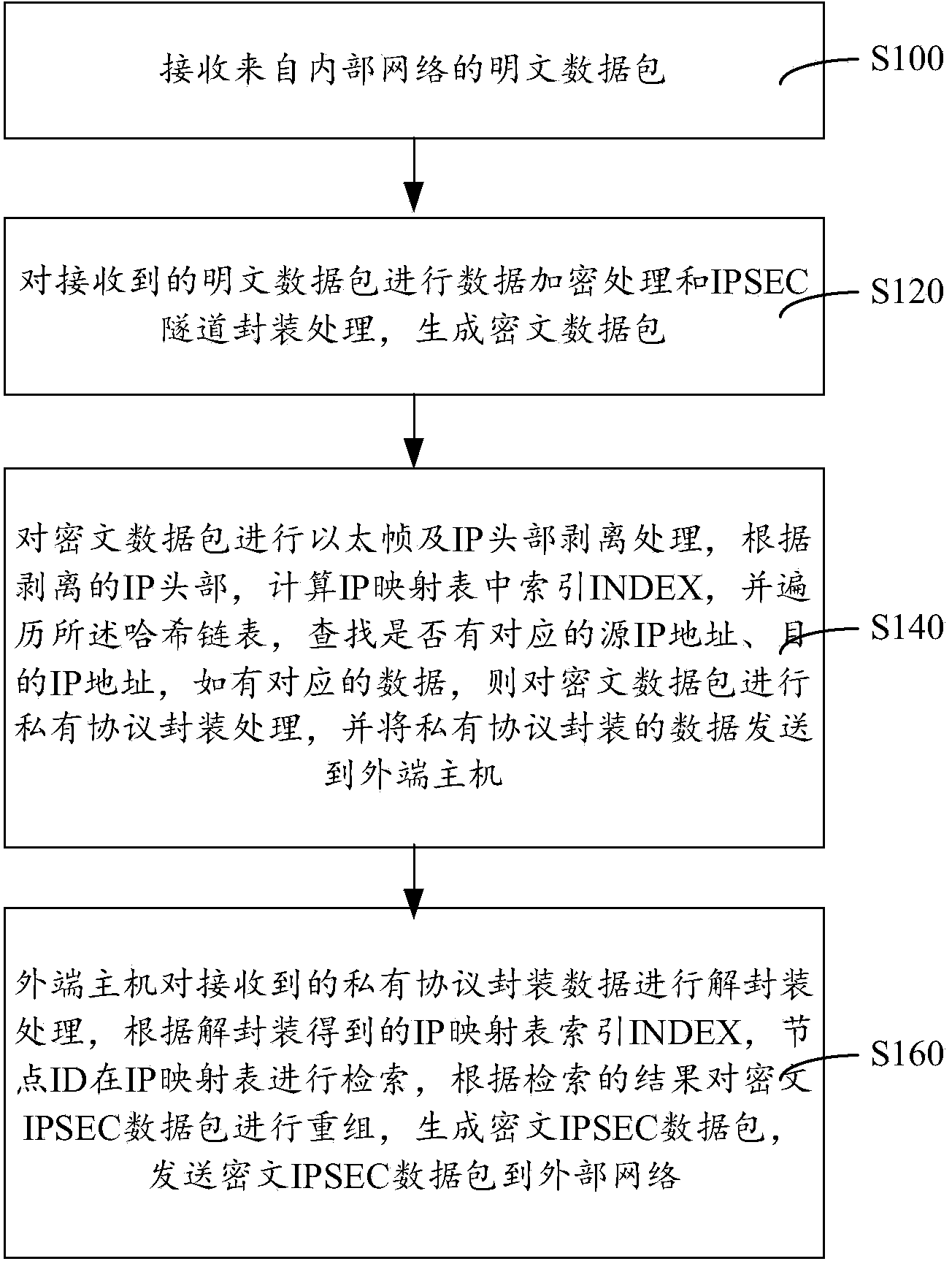
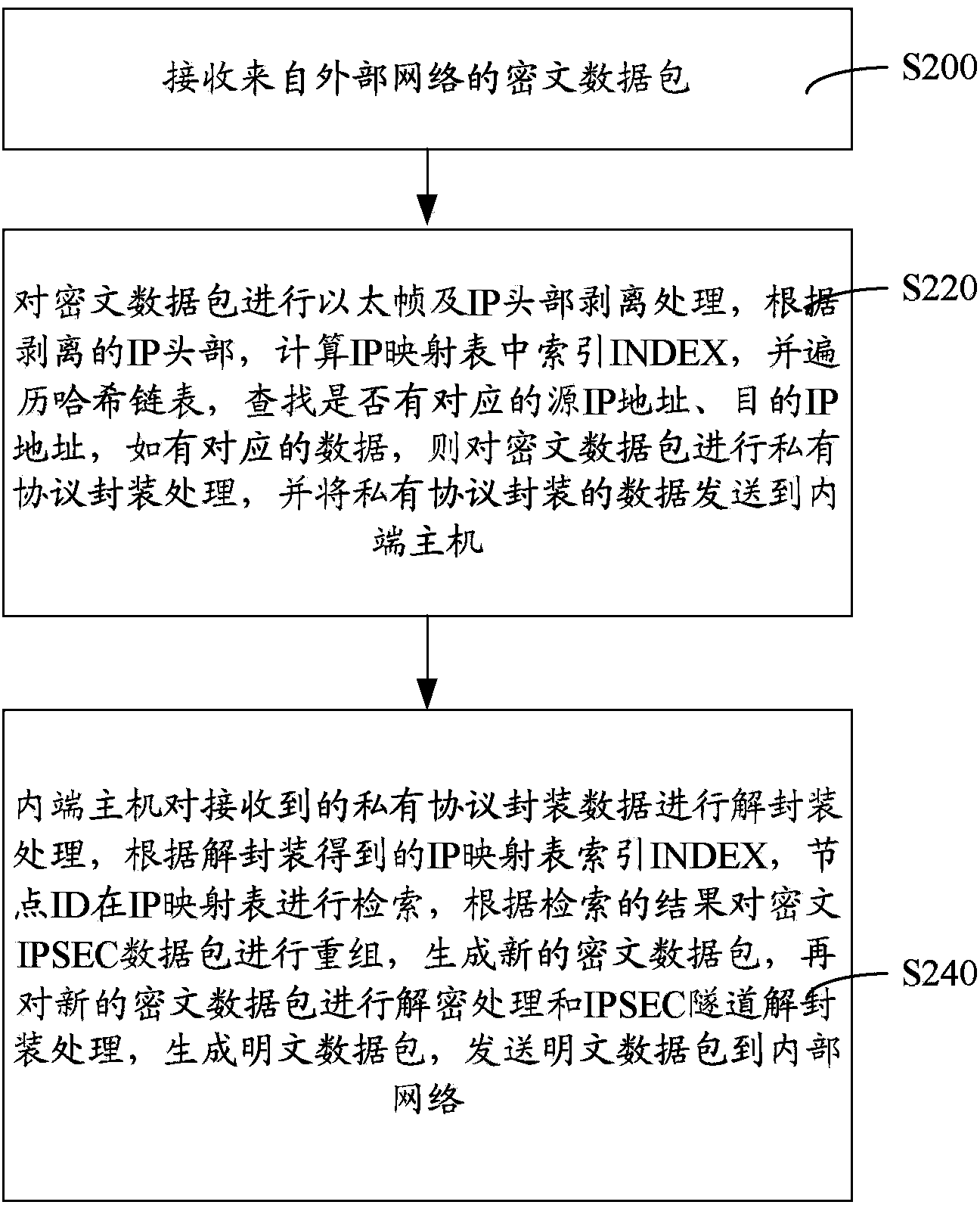
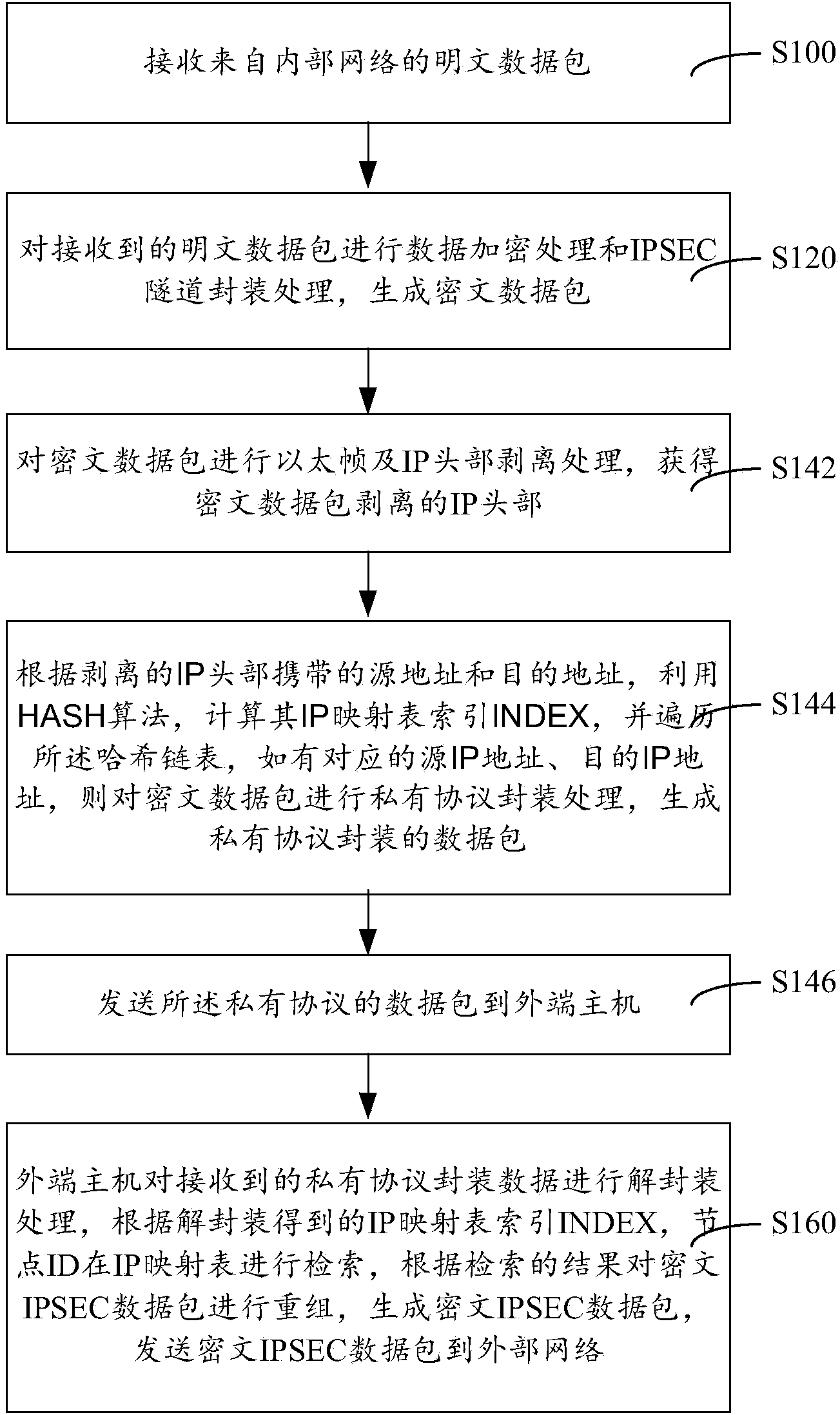
[0040] Such as figure 1 , figure 2 Shown, a kind of isolation method of IPSEC VPN equipment is characterized in that, comprises steps:
[0041] The same IP mapping table is maintained in the internal host and the external host, wherein the IP mapping table is a hash linked list, and the hash linked list defines the source address of the IP mapping table index INDEX and the data packet, the destination address and IP mapping ID information.
[0042] The IP mapping table is maintained and stored at both ends of the internal host and the external host, and the storage in the internal and externa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More