Method and system for securely storing data and accessing data
A technology for securely storing and accessing data, applied in the information field, it can solve the problems of memory data leakage and easy cracking of encryption algorithms, so as to prevent data leakage and facilitate viewing and use.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
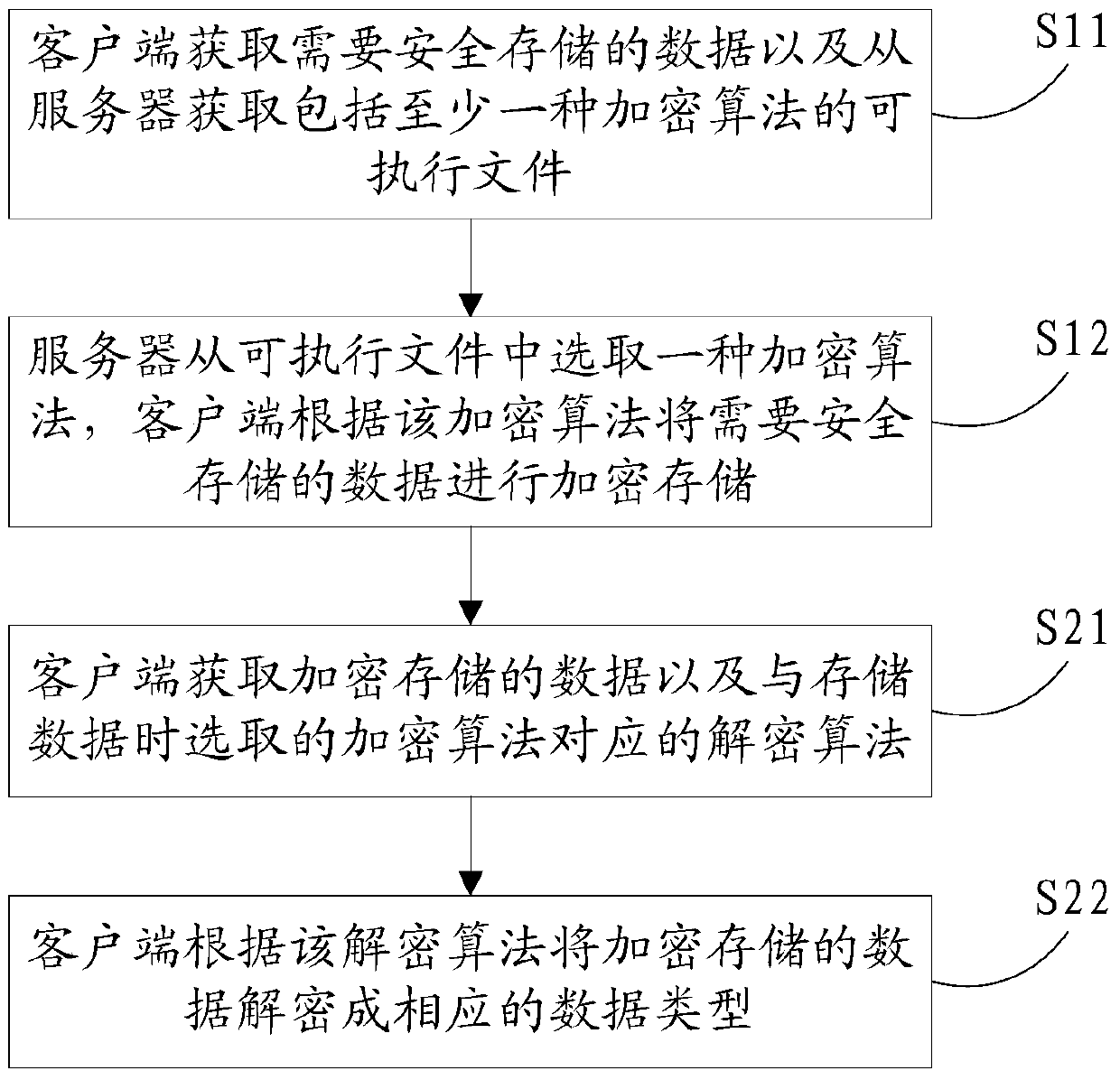
[0069] Please refer to figure 1 , Embodiment 1 of the present invention is:
[0070] a method of securely storing data and accessing data, including storing data and accessing data;
[0071] Stored data includes:
[0072] S11. The client obtains the data that needs to be safely stored, and obtains from the server an executable file including at least one encryption algorithm and a decryption algorithm corresponding to the encryption algorithm; specifically: the client obtains the encrypted dynamic link library from the server, and The dynamic link library is decrypted into an executable file, and the executable file is loaded into a specified program of the client; the executable file includes at least one encryption algorithm;
[0073] S12. The server selects an encryption algorithm from the executable file, and the client encrypts and stores the data that needs to be stored safely according to the encryption algorithm; specifically: the client converts the data that needs ...
Embodiment 2
[0082] Please refer to figure 2 , the second embodiment of the present invention is:
[0083] A system for safely storing data and accessing data, characterized in that it includes: a client 2 and a server 1; the server 1 is used to store at least one executable file including at least one encryption algorithm, and obtain it from the client 2 Select an encryption algorithm for client 2 in the executable file of ;
[0084] The client 2 includes:
[0085] The first acquisition module 21 is configured to acquire data that needs to be safely stored and acquire an executable file including at least one encryption algorithm from a server;
[0086] The first conversion module 25 is used to convert the data that needs to be safely stored into a character string;
[0087] The second conversion module 26 is used to convert the character string into a binary array;
[0088] The encryption module 22 is used to encrypt and store the data that needs to be safely stored according to the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More