A data security sharing method suitable for hybrid cloud environment
A data security and hybrid cloud technology, applied in user identity/authority verification, transmission systems, electrical components, etc., can solve problems such as increasing the burden on data owners, and achieve the effect of easy data re-encryption, easy implementation, and low resource overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] The technical solution of the present invention will be further described in detail below with reference to the drawings and embodiments. The following examples are implemented on the premise of the technical solution of the present invention, and detailed implementation manners and processes are given, but the protection scope of the present invention is not limited to the following examples.
[0044] In order to better understand the method proposed in this embodiment, a company encrypted file sharing event is selected. In the event, there are one data owner, two access users (user A has the attributes of "technical department, "manager"; user B has the attributes of "personnel department" and "supervisor") and a shared file.
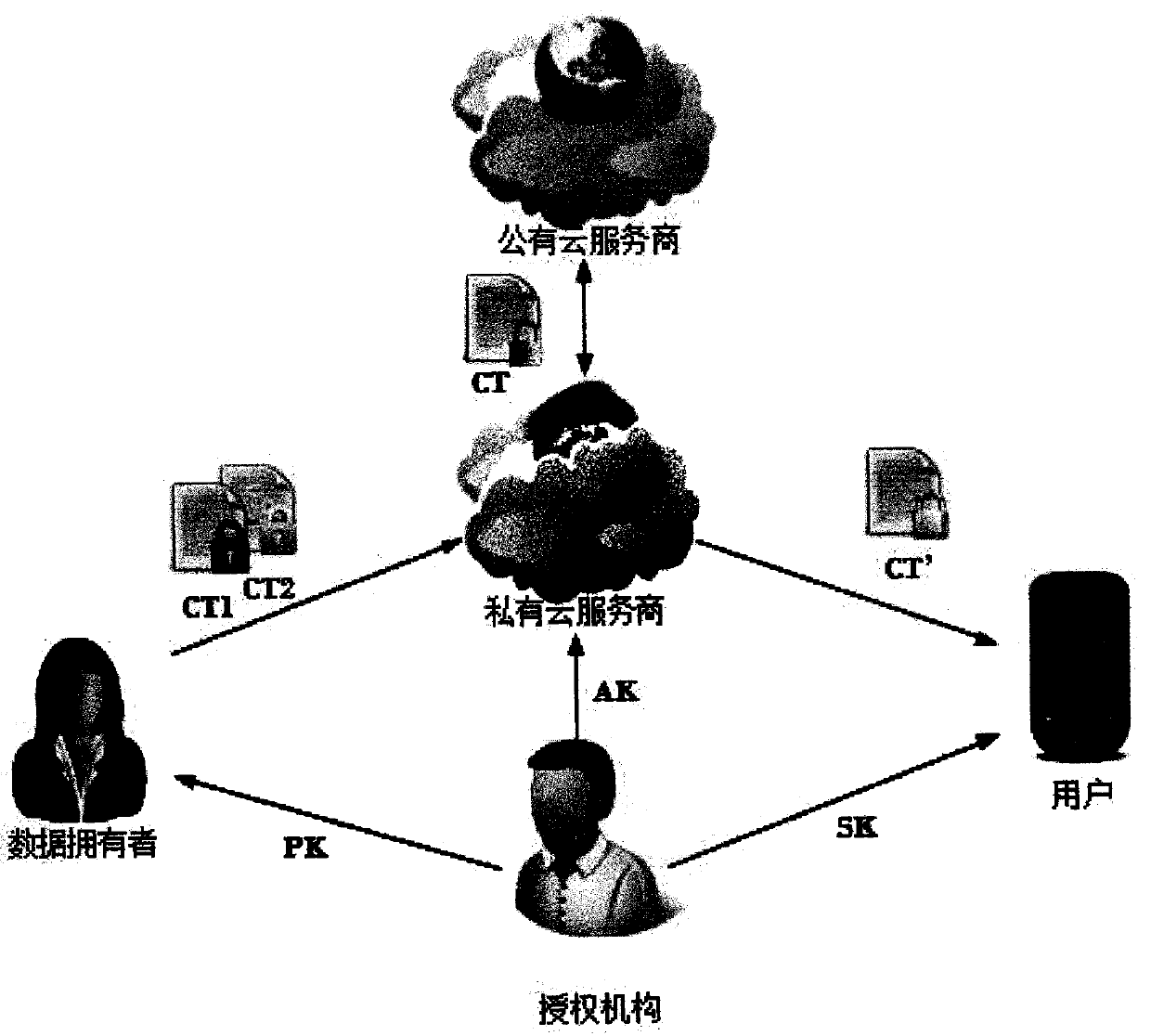
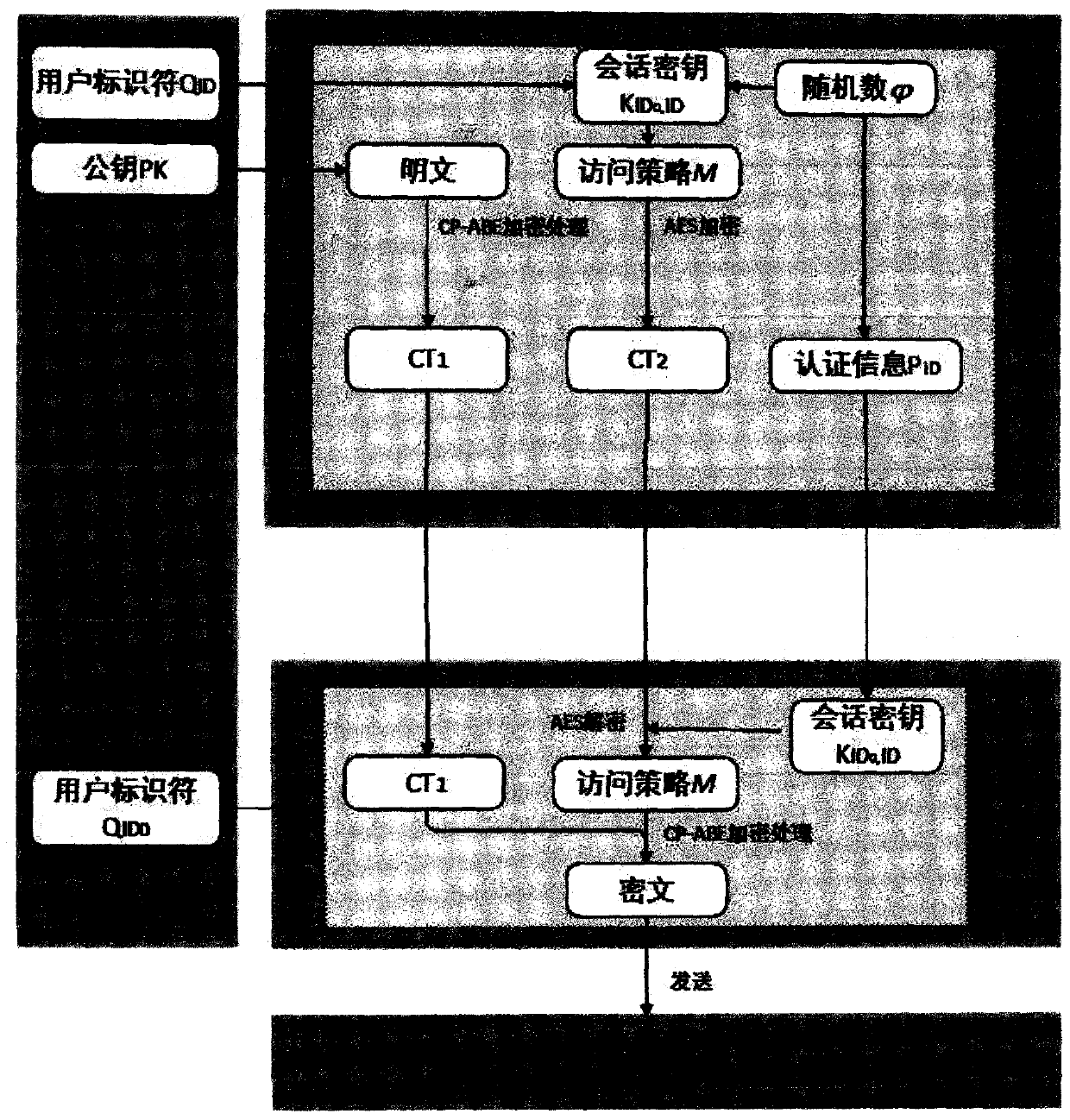
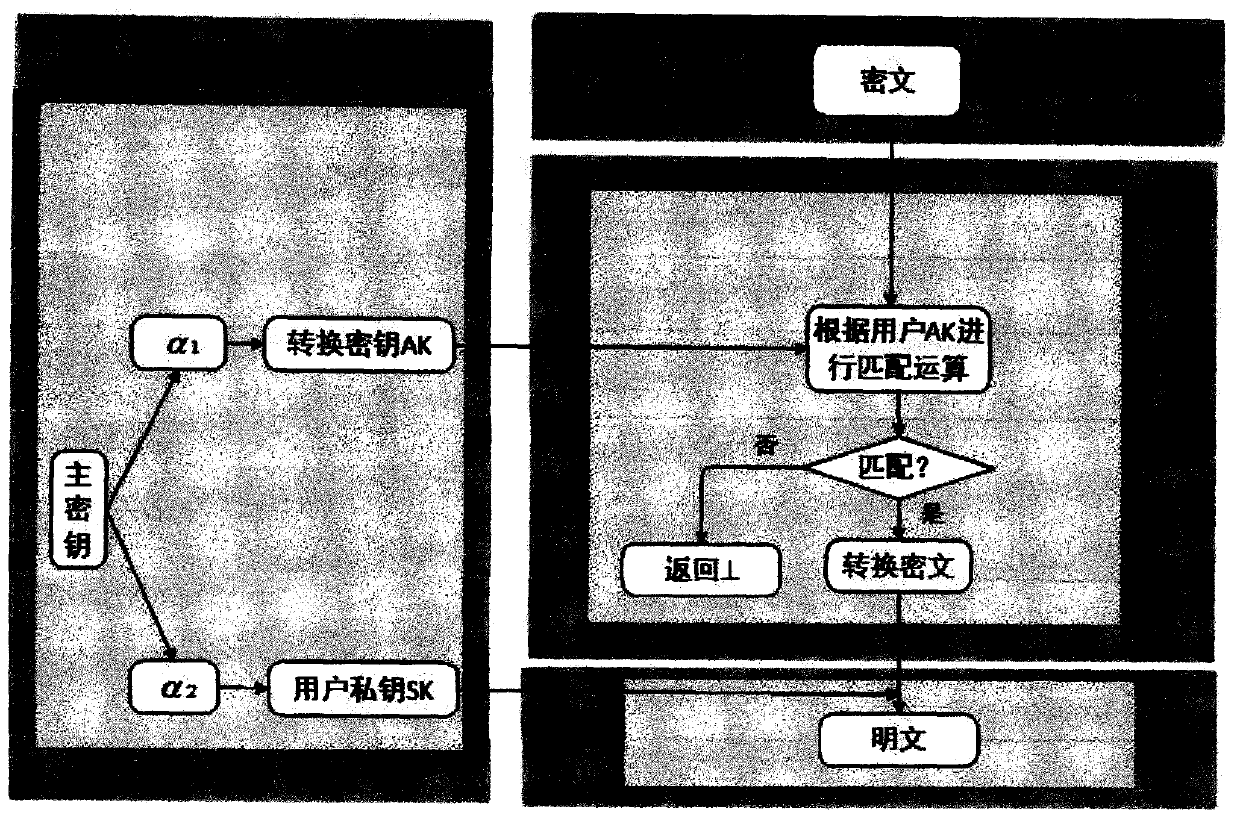
[0045] Such as the structure diagram of the method of the present invention ( figure 1 ), the specific implementation steps of this embodiment are as follows:
[0046] 1. System initialization
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More