Intelligent key based on cloud-side management
A smart key and key technology, applied in the field of smart keys, can solve the problems of high safety performance, inability to effectively guarantee safety, copying of smart keys, etc., and achieve the effect of reducing replacement costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
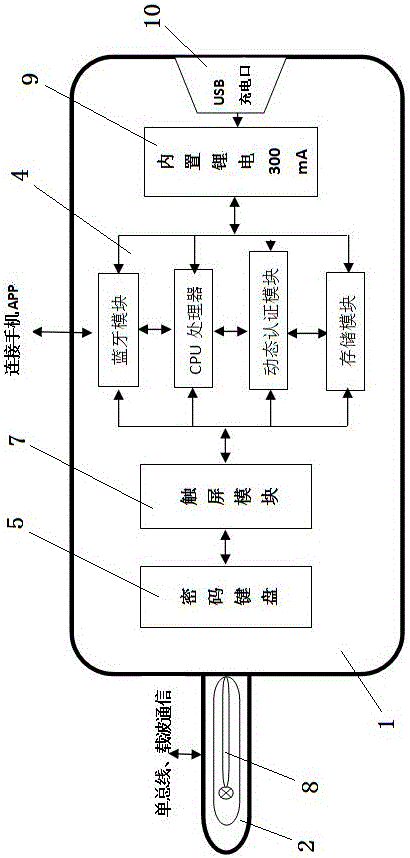
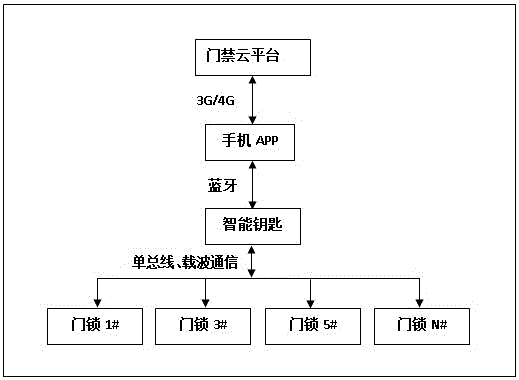
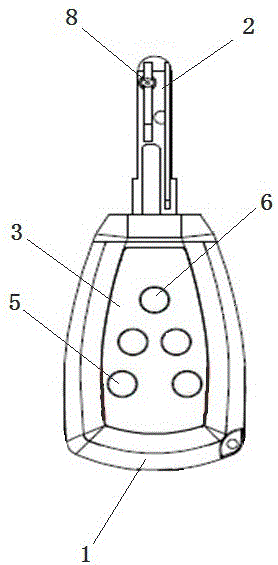
[0029] In practical applications, after the electronic key core 2 is inserted into the lock, the user enters the activation password of the ID identification module 8 through the password button on the key handle 1. After the ID identification module 8 is successfully activated, the sensor on the lock matches the ID The authorization in the recognition module 8 is identified, and the access control cloud platform is used for query verification. Only the key with the correct authorization can successfully open the door lock. The control chip 4 on the key handle 1 communicates with the APP client through a Bluetooth wireless signal. The APP client can edit the ID authority in the ID recognition module 8, and at the same time, the APP client can query which door the key has opened. lock.
[0030] When the smart key communicates with the lock cylinder, after obtaining the lock cylinder MAC address, the MAC address is used as the encryption factor for encrypted communication to ensure...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap