SDN switch flow table encrypting method based on FPGA
An encryption method and switch technology, applied in data exchange network, computer security device, internal/peripheral computer component protection, etc., can solve the problem that the memory is easy to be read and modified, and achieve the effect of reducing processing time and increasing security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0020] The following takes NetMagic as an example to further describe the present invention in detail. It should be noted that the parameters in the embodiments do not affect the generality of the present invention.
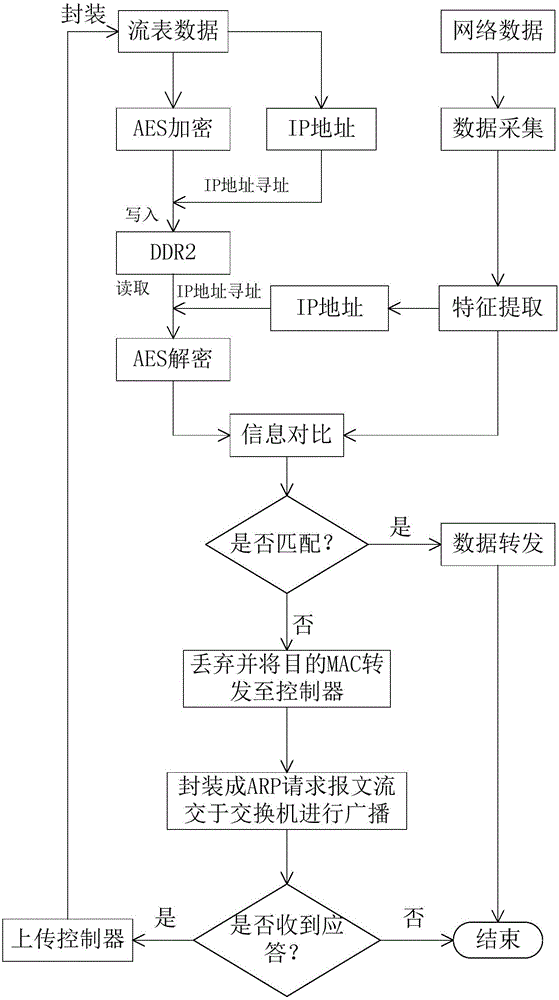
[0021] An FPGA-based SDN switch flow table encryption method, such as figure 1 As shown, the specific steps include the following:
[0022] Step S1, the host computer downloads the specified flow table to the internal FPGA through the nmac protocol.
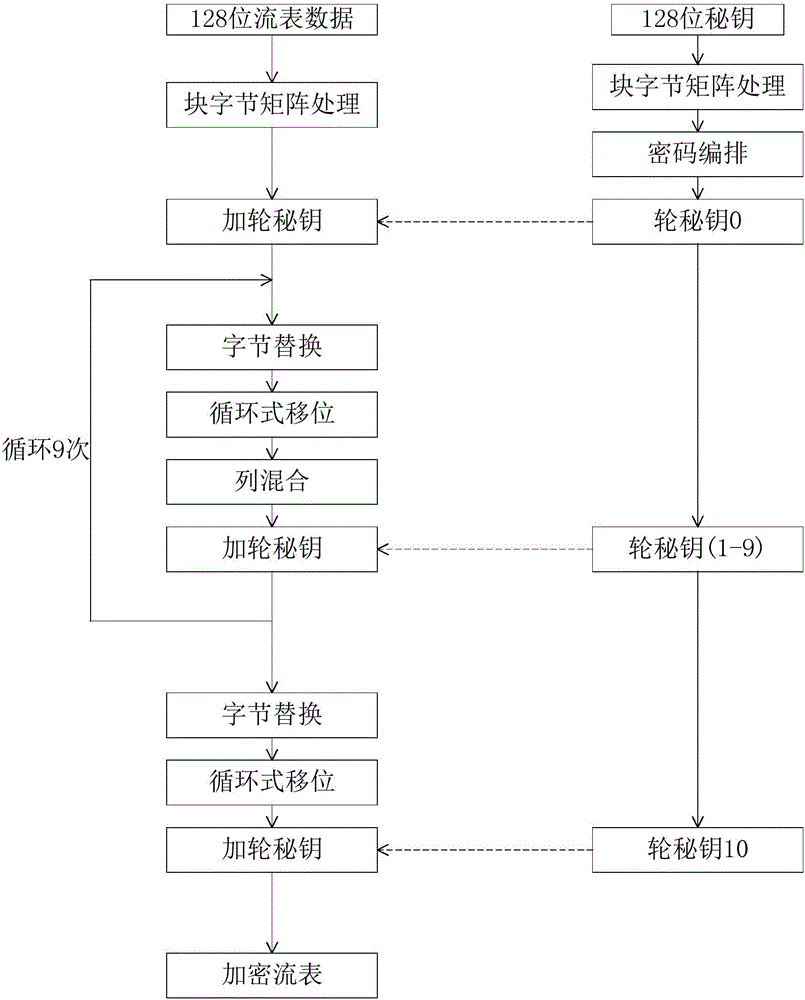
[0023] Step S2, the FPGA obtains the IP address by extracting the flow table, and then encrypts the received flow table through the AES encryption algorithm. The specific encryption process is as follows: figure 2 As shown, the IP address is mapped into a 26-bit DDR2 write address through the Hash operation, and the corresponding flow table ciphertext is written into the address.
[0024] Step S3, the FPGA collects data in the rx_tx_1000 module from the data stream sent by the client, and extracts features from t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com