Quantum secrete key distribution method based on DPI
A quantum key and secret key technology, applied in the field of DPI-based quantum secret key distribution, can solve the problems of limiting the scope of use of quantum secure communication, hindering the development process of practicality, generating speed and limited key quantity, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0038] The application principle of the present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
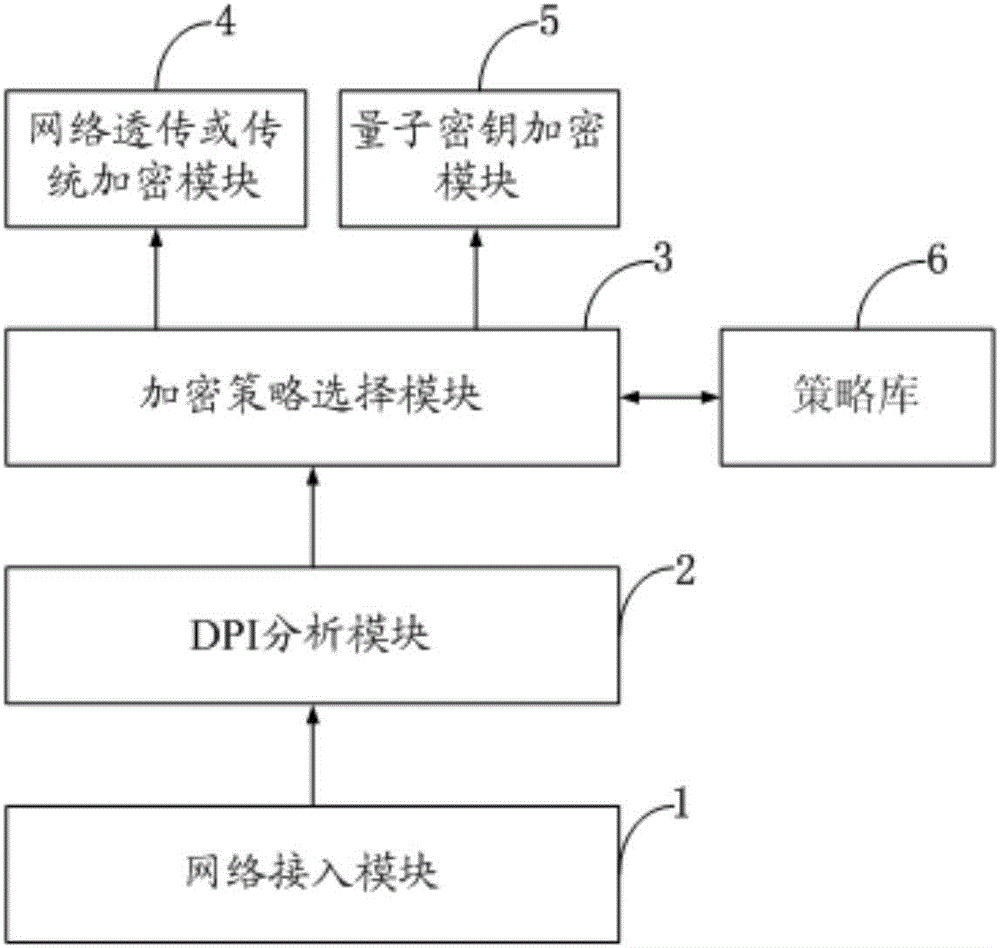
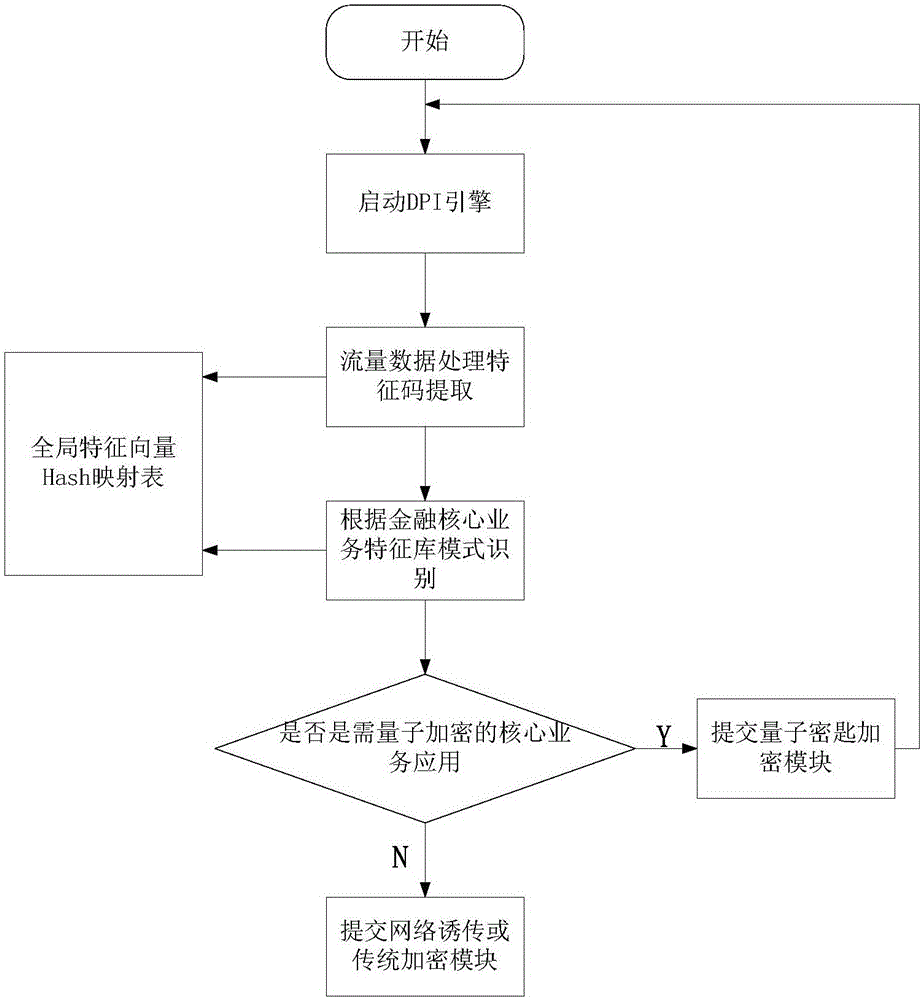
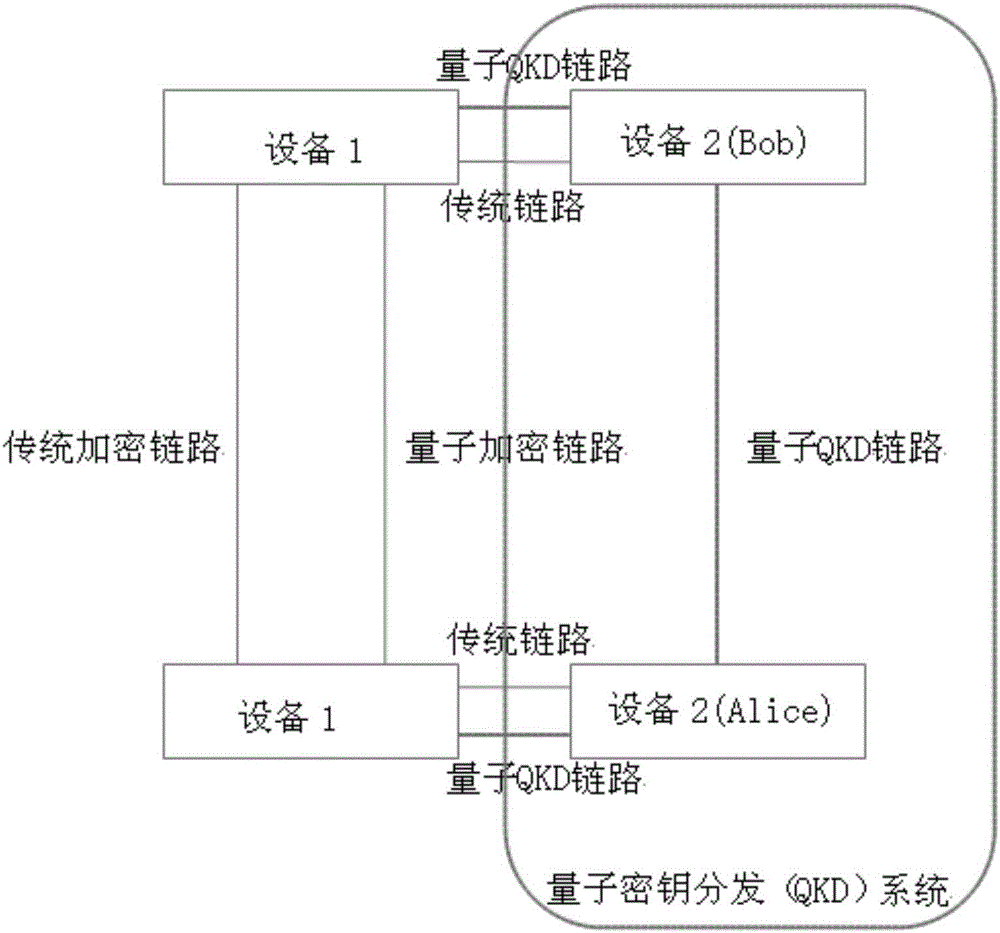
[0039] figure 1 The structure of the DPI-based quantum secret key distribution method of the present invention is shown, as shown in the figure, the present invention is implemented in this way, a kind of DPI-based quantum secret key distribution method includes network access module 1, DPI (based on depth Packet detection technology) analysis module 2, encryption strategy selection module 3, network transparent transmission or traditional encryption module 4, q...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More