Access control method and system based on security tag
A security label and access control technology, applied in the field of access control systems based on security labels, can solve the problem that information cannot be marked with security labels in real time, and achieve the effects of improving security and reliability, avoiding information leakage, and implementing a simple mechanism.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] The invention will be described in detail below in conjunction with the accompanying drawings and embodiments.
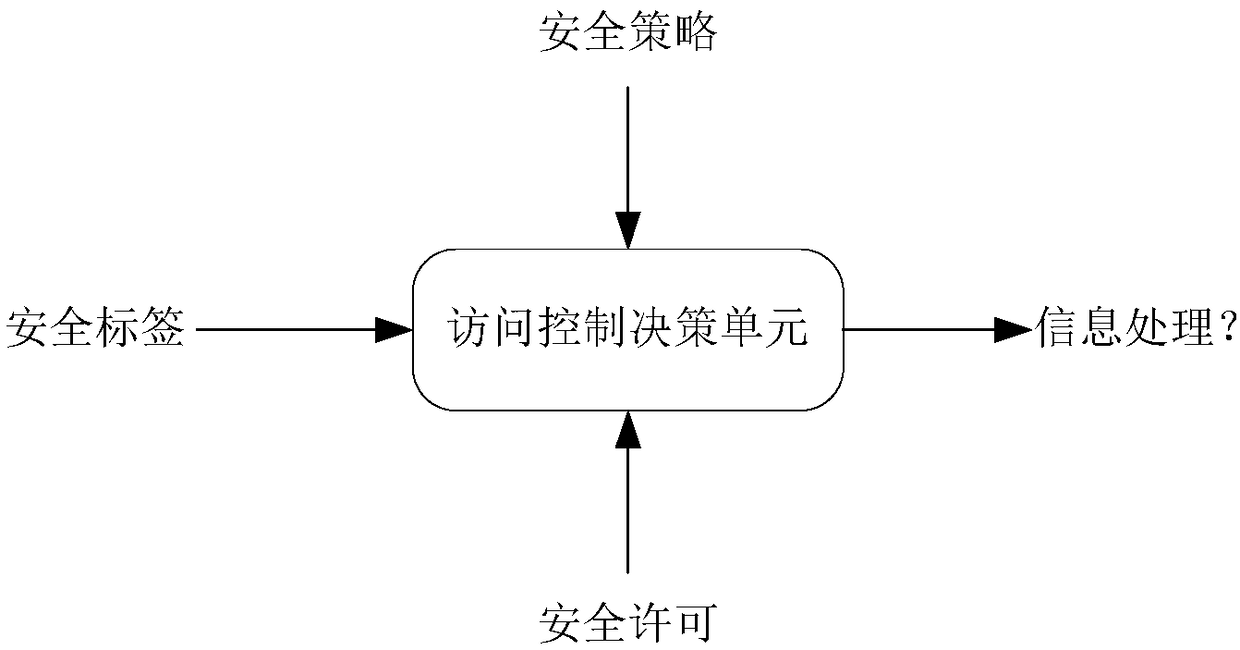
[0038] Such as figure 1 It is a schematic diagram of the access control method based on security labels. When the subject processes the information, the access control decision-making unit will check whether the security permission can match the security label of the information according to the security policy. If it can match, the subject is allowed to access the information, otherwise, the access is denied.
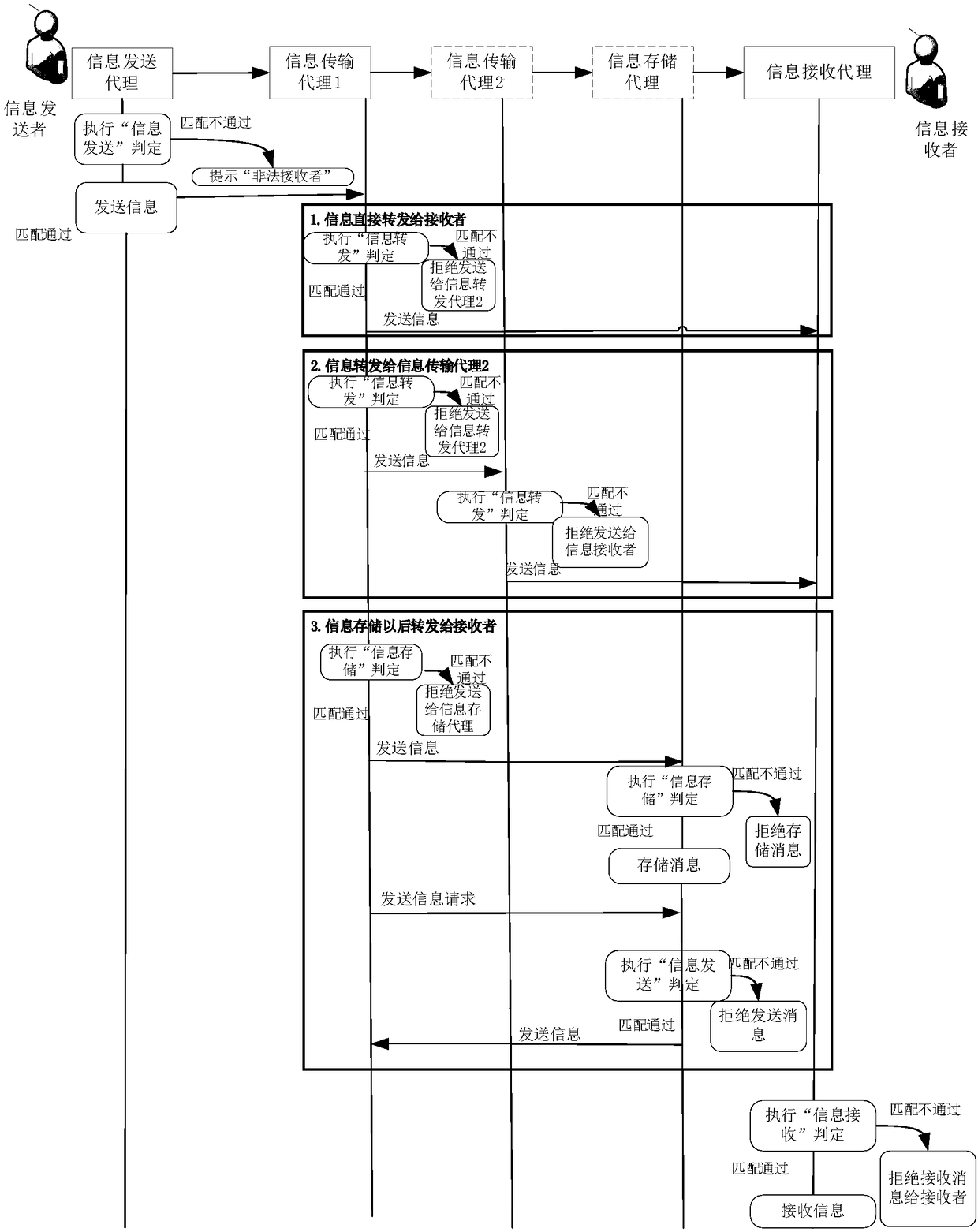
[0039] The core of the present invention is to control the subject's access to information according to the preset security policy. The specific implementation method is based on security labels, marking security permissions for information access subjects, marking security labels for information, and generating access control policies based on security requirements. When the information is in circulation, the access control mechanism is activated a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More