Privacy protection method in face authentication system based on edge calculation
A technology of edge computing and authentication system, applied in the privacy protection field of face authentication system, which can solve the problems of victim privacy, life, property impact, privacy leakage, sensitive face data, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0054] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
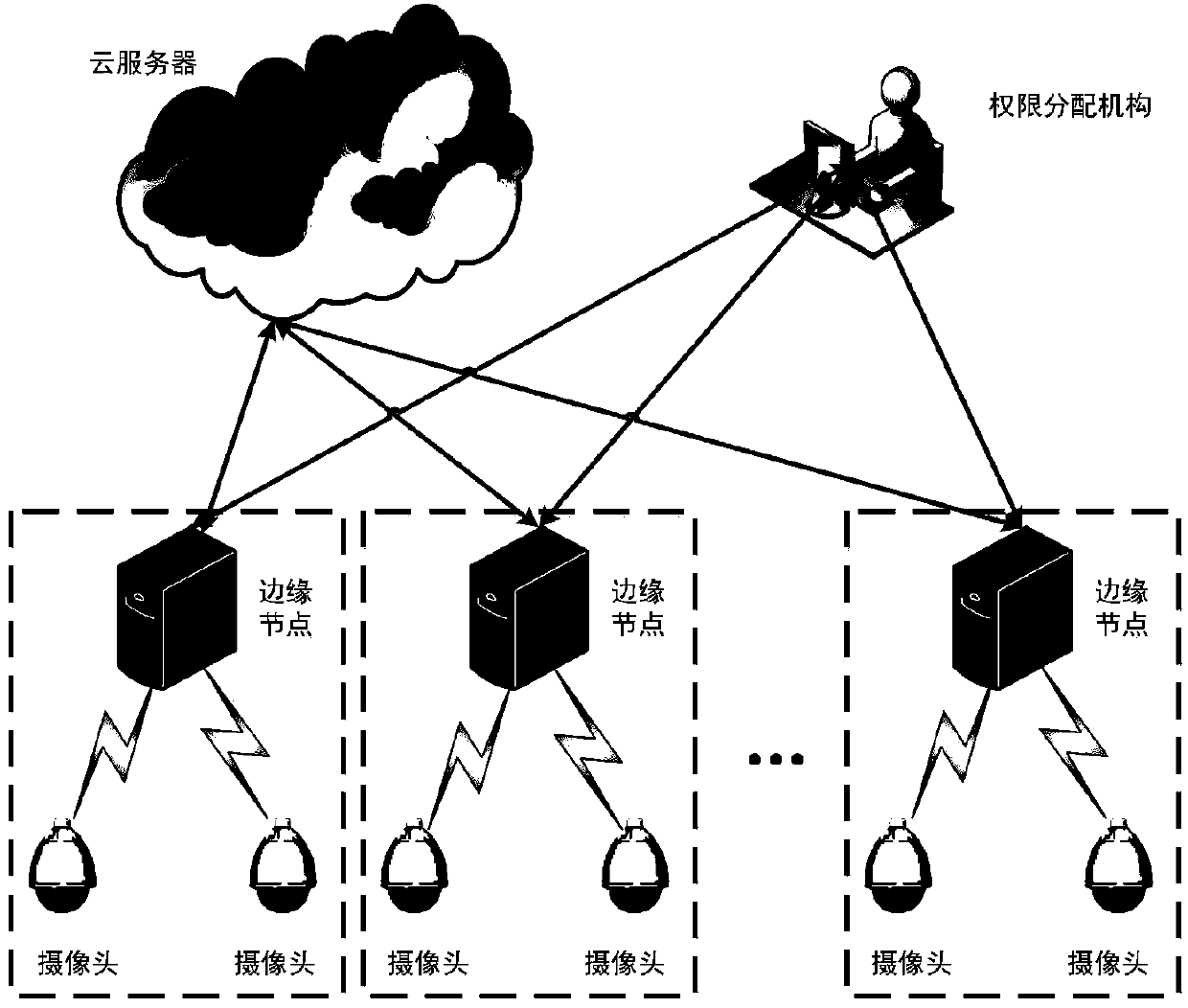
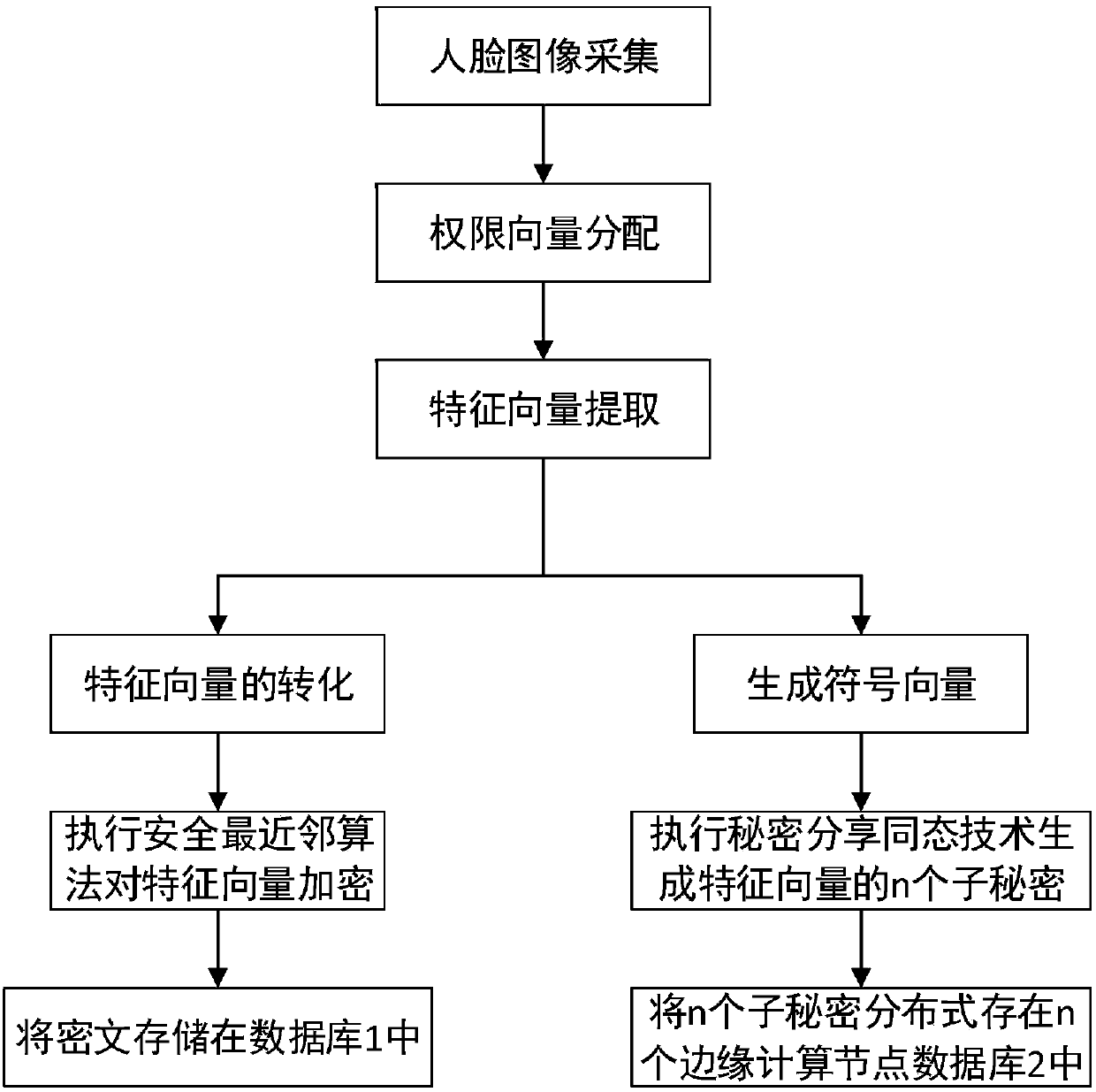
[0055] The invention adopts the safe nearest neighbor algorithm and the secret sharing homomorphic technology to realize the face recognition function under the ciphertext, so that the cloud server and the edge computing node can complete the user identity authentication function without violating the privacy of the user's face data.
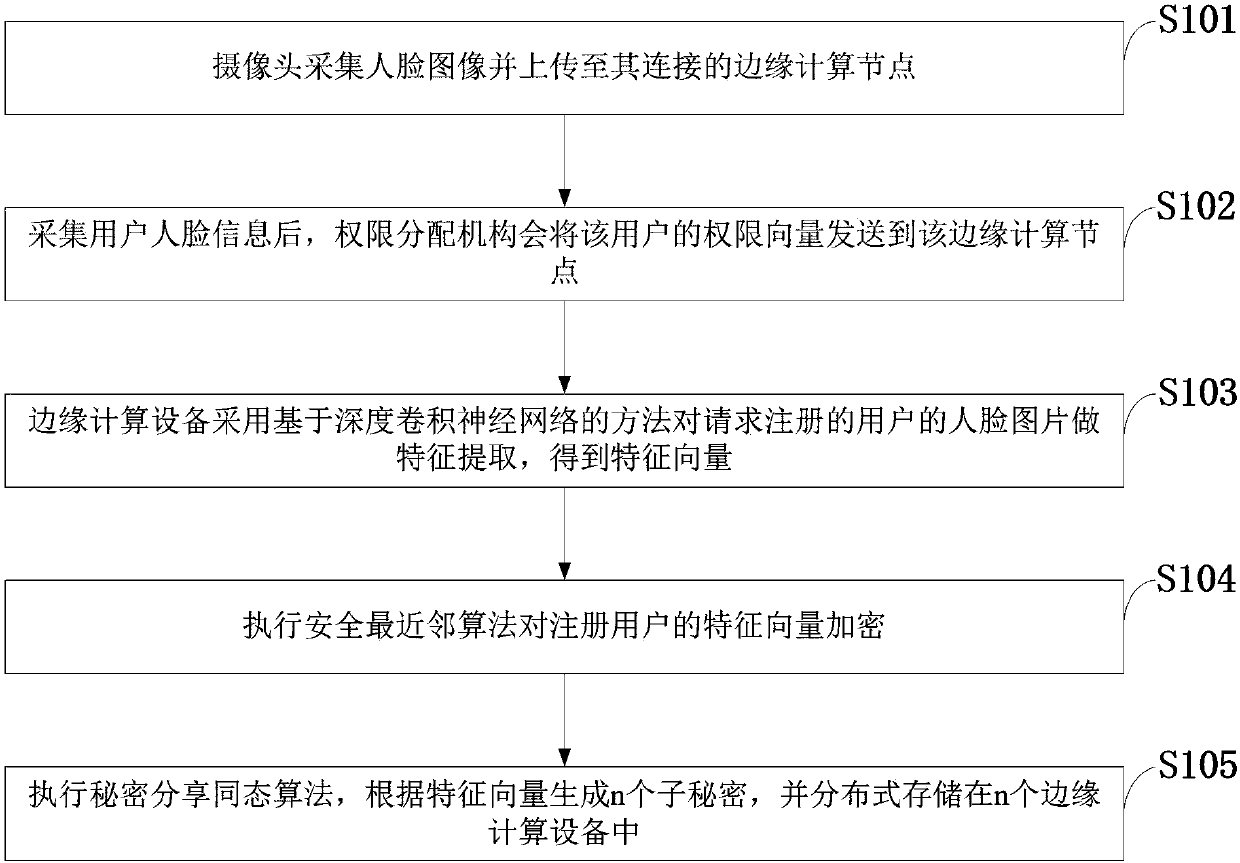
[0056] Such as figure 1 As shown, the privacy protection method in the face authentication system based on edge computing provided by the embodiment of the present invention includes the following steps:
[0057] S101: The camera collects the face image and uploads it to the edge computing n...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More