AKA identity authentication system and AKA identity authentication method based on symmetric key pool and relay communication
A technology for identity authentication and relay communication, applied in the fields of private identity authentication and key negotiation, it can solve the problems of easy cracking, inability to maintain the freshness or variable range of the key seed, and weak confidentiality, etc. True randomness and security, increased capacity and replaceability, and improved high security effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0067] instructions
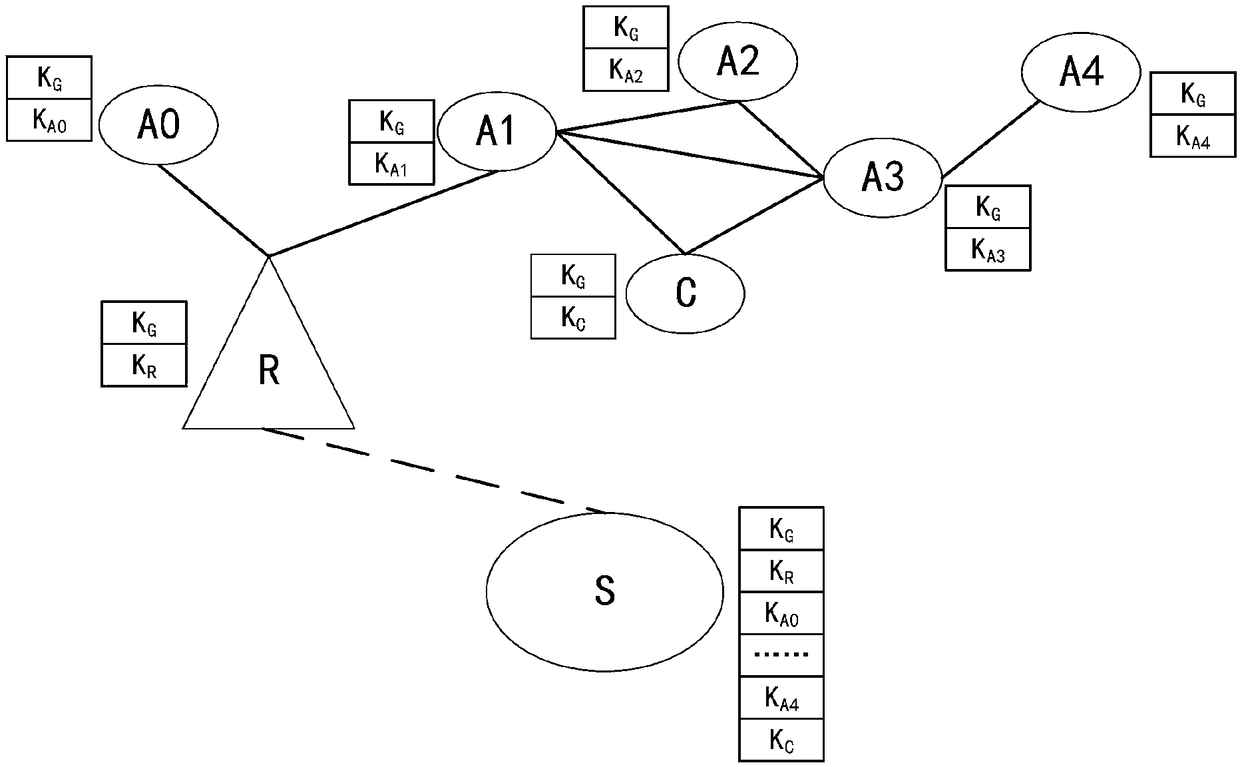
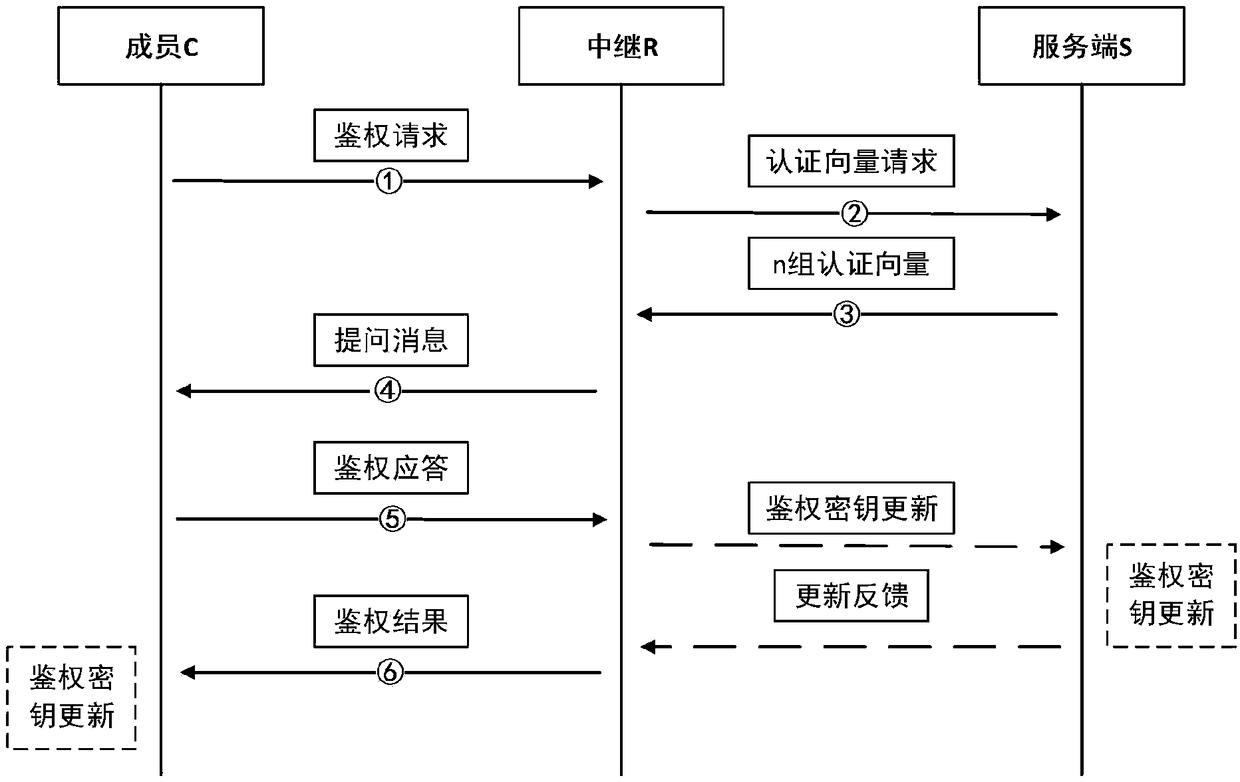
[0068] The scenario of this embodiment is as figure 1 As shown, in this figure, member R, member A0, member A1, member A2, member A3, member A4, and member C are all members of the same group, and member R is a relay unit.
[0069] In this figure, the active party participating in the authentication is C, which contains the private key pool K C and group key pool K G ; The passive party participating in the authentication is R, which contains the private key pool K R and group key pool K G .
[0070] The private key pool is a symmetric key pool between members and the server, and the group key pool is a symmetric key pool between members in the group.
[0071] Member S is the key management server and also serves as the server. Both member C and member R belong to S, which contains the private key pool and group key pool K of all members. G .
[0072] As a communication relay, member R has performed identity authentication and key negotiation with ...
Embodiment 2
[0131] instructions
[0132] Such as Figure 4 As shown, the identity authentication system of the present invention may include multiple key management servers, and different key management servers are located in different quantum network service stations. Each quantum network service station is in the quantum communication network, so quantum network service stations can share inter-station quantum keys through QKD, thus ensuring high information security.
[0133] Such as Figure 4 , in this figure, member R, member A0, member A1, member A2, member A3, member A4 and member C are all members of the same group, and member R is a relay unit. The active party participating in the authentication is C, which contains the private key pool K C and group key pool K G ; The passive party participating in the authentication is R, which contains the private key pool K R and group key pool K G ; Members S1 and S2 are key management servers, also serving as servers, member R belong...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com