Marine Big Data Sensitivity Assessment System and Prevention Methods for Confidentiality Needs
An evaluation system and big data technology, applied in the direction of digital data protection, etc., can solve the problems of classification result interference, inaccurate classification results, slow recognition speed, etc., to improve efficiency and accuracy, facilitate open sharing, and fast recognition speed Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0055] This embodiment provides a marine big data sensitivity assessment system for confidentiality requirements, which mainly includes the following parts;
[0056] The data feature extraction module is used to extract data samples and metadata information from the structured ocean secret raw data, and use natural language processing related technologies to extract keywords, subject words, and associated words from unstructured ocean secret information documents to establish a corpus , and perform feature extraction to form a sensitive feature library; it is used to extract its data attribute features from the target processing data of marine big data, and prepare for the next step of matching with the sensitive feature library to find sensitive data.
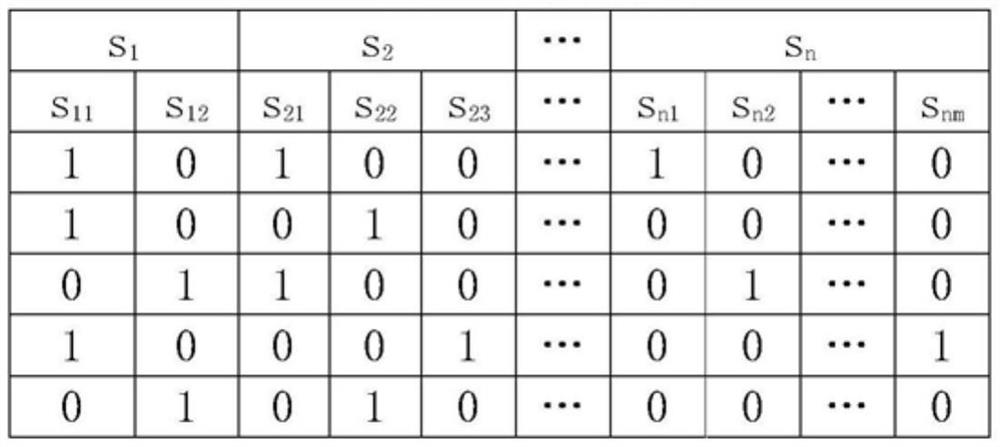
[0057] The sensitive feature matching module is used to match the target processing data features in the marine big data with the sensitive feature library, analyze the similarity between the target processing data set and the ...
Embodiment 2
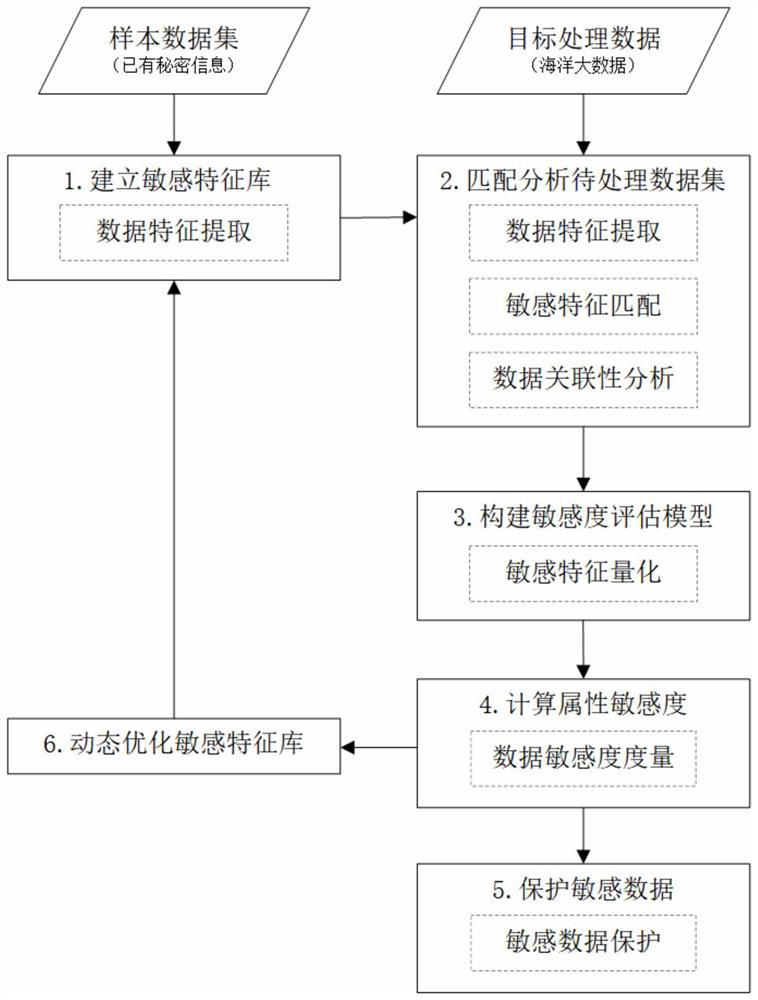
[0063] The prevention method based on the marine big data sensitivity assessment system for confidentiality requirements described in Embodiment 1, that is, the identification, evaluation and protection of sensitive data, through the identification of sensitive content, the correlation analysis of sensitive data, the sensitivity of sensitive data Evaluate, accurately discover sensitive information hidden in big data, effectively prevent illegal users from stealing sensitive information hidden in big data through data mining, data integration and data correlation analysis, and realize reliable protection of sensitive information.
[0064] combine figure 1 As shown, the method of the present embodiment includes the following steps:
[0065] Step 1: Establish a sensitive feature database.
[0066] Starting from the relevant regulations on the scope of secrets in marine work, the formed secret information and internal business information, reverse analysis is used to extract the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com