Intelligent contract vulnerability detection method and system
A smart contract and vulnerability detection technology, applied in the direction of instrument and platform integrity maintenance, character and pattern recognition, etc., can solve the problems of inaccurate results, long cycle, high cost, etc., and achieve convenient detection, high accuracy and fast speed Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] In view of this, the present invention provides a method and device for smart contract vulnerability detection to improve the developer's development efficiency and enhance the code Security, reducing developer time and investment costs.
[0027] The technical solution of the present invention is as follows: a method for smart contract vulnerability detection, the method comprising uploading smart contract code files;
[0028] Correspondingly, the smart contract code file is in a .sol file format.
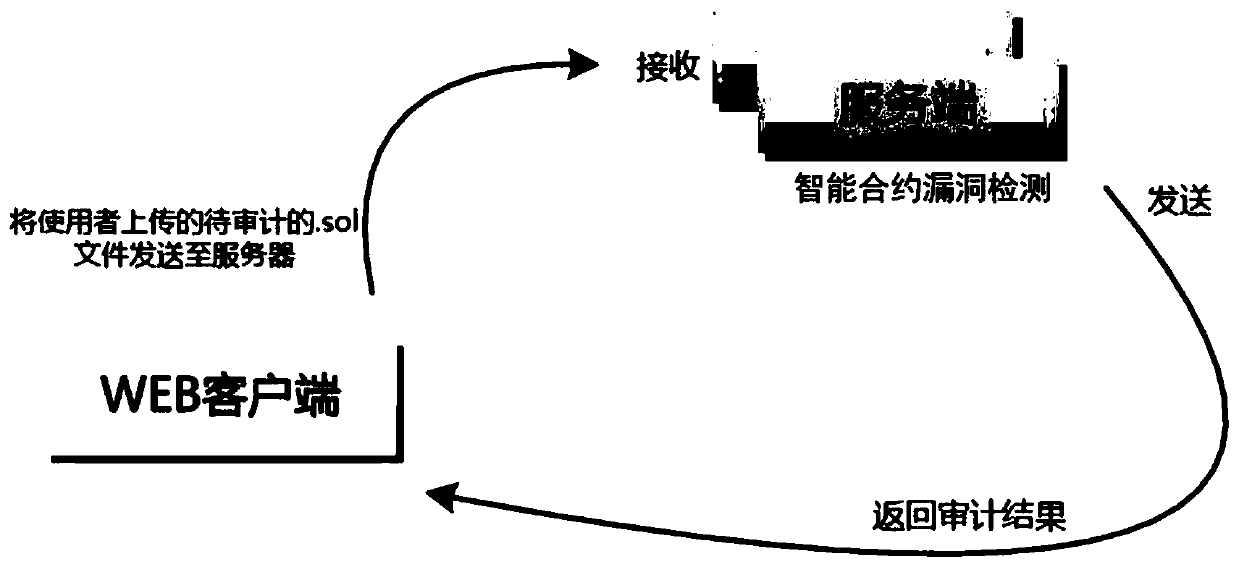
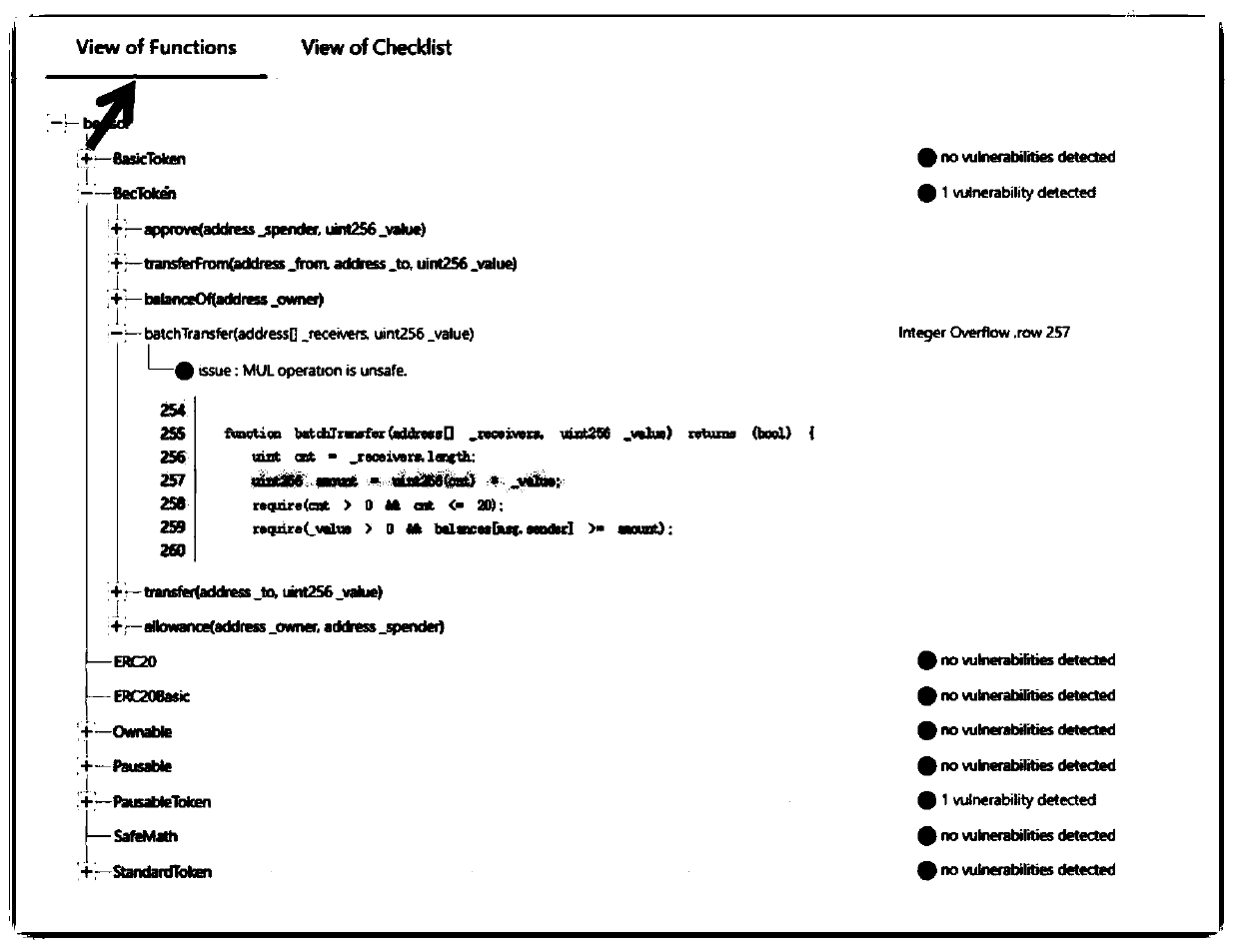
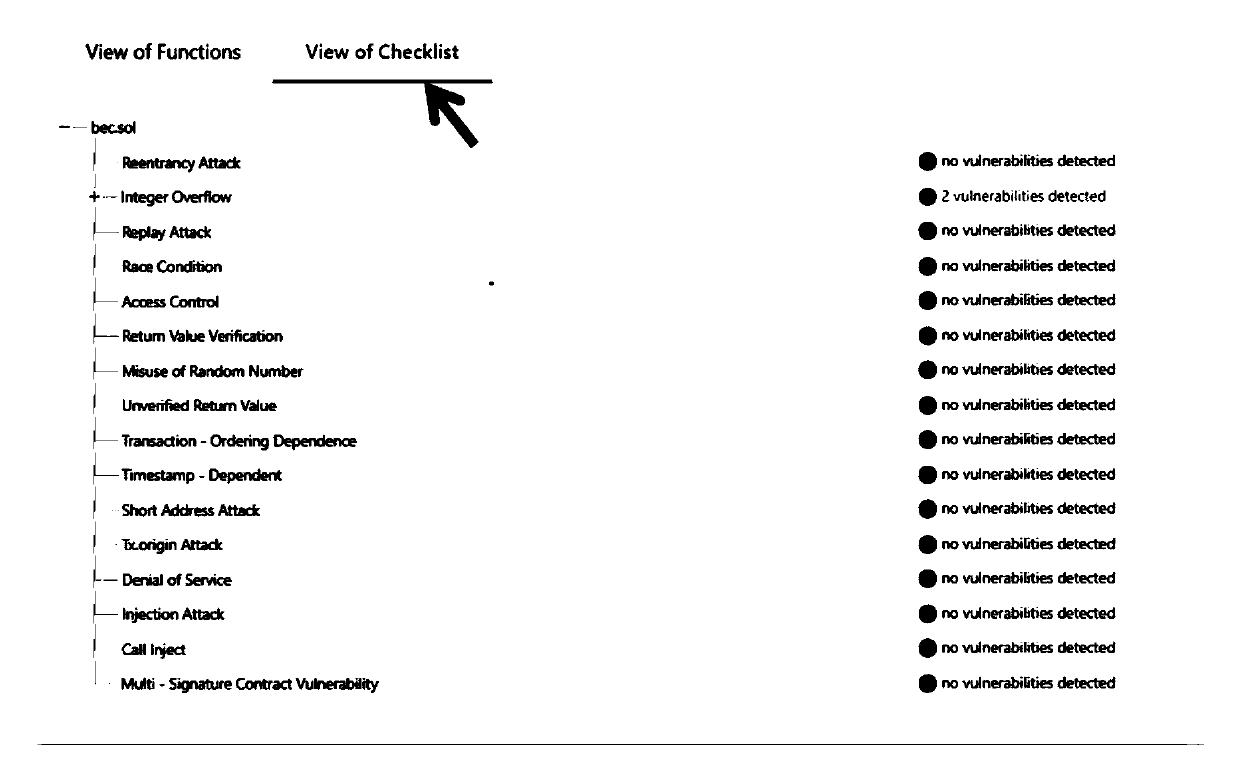
[0029] Such as figure 1 Shown is the function implementation topology diagram of the smart contract vulnerability detection method in this embodiment. Specifically, the .sol smart contract file to be audited is determined by the local client and uploaded to the server.
[0030] In this embodiment, the smart contract vulnerability detection method is an engine made through a series of technical detections for the smart contract written in Solidity and running on the Ethereu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More