SM4 encryption and decryption method and circuit
An encryption, decryption, and circuit technology, applied in the field of information security, can solve problems such as consumption of storage resources and chip resource occupation, and achieve the effect of reducing storage resources
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
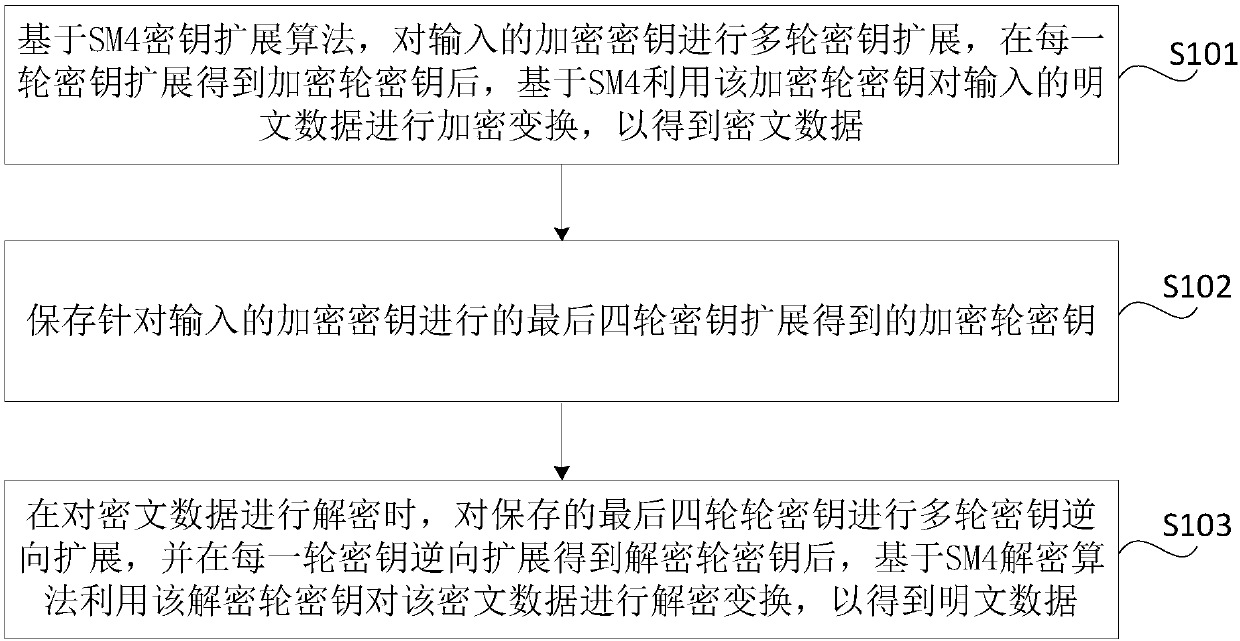
Image
Examples
Embodiment 1
[0047] Embodiment 1: Key Expansion
[0048] In the embodiment of the present disclosure, the length of the input encryption key is 128 bits, which can be expressed as MK=(MK 0 , MK 1 , MK 2 , MK 3 ), among them, MK i (i=0, 1, 2, 3) is 32 bits. Specifically, multiple rounds of key expansion can be performed on the encryption key according to formula (1) and formula (2), and the schematic diagram of the expansion is shown as the encryption algorithm figure 2 shown.
[0049] (K 0 ,K 1 ,K 2 ,K 3 )=(MK 0 ⊕FK 0 , MK 1 ⊕FK 1 , MK 2 ⊕FK 2 , MK 3 ⊕FK 3 ) (1)
[0050] RK i =K i+4 =K i ⊕T'(K i+1 ⊕K i+2 ⊕K i+3 ⊕CK i ), i=0,1,...,31 (2)
[0051] Among them, FK=(FK 0 ,FK 1 ,FK 2 ,FK 3 ) is a system parameter, FK is desirable 0 =(A3B1BAC6), FK 1 =(56AA3350), FK 2 =(677D9197), FK 3 =(B27022DC);CK i As a fixed parameter, CK can be set i,j for CK i The jth byte of j=0,1,2,3, then CK i,j =(4i+j)×7(mod 256); ⊕ represents XOR operation; T' represents syntheti...
Embodiment 2
[0054] Embodiment 2: Key Reverse Expansion
[0055] Since U=W⊕V can exchange the positions of the two variables arbitrarily and the decryption round key is the reverse order of the encryption round key, when decrypting the encrypted ciphertext data, the last four round keys saved can be (RK 31 ,RK 30 ,RK 29 ,RK 28 ) as the initial key, according to the formula (3) to carry out key reverse expansion, the schematic diagram of the key reverse expansion process is as follows image 3 shown.
[0056] RK i-4 =RK i ⊕T'(RK i-3 ⊕RK i-2 ⊕RK i-1 ⊕CK i ), i=31,30,...,0 (3)
[0057] Wherein, the definitions of the combined permutation operation T', the nonlinear transformation τ, and the linear transformation L' can refer to the relevant description of the above-mentioned key expansion, and will not be repeated here.
[0058] It can be seen that in the direction of decryption, by saving the last four round keys and performing key reverse expansion accordingly, all round keys RK...
Embodiment 3
[0059] Embodiment Three: Encryption Transformation
[0060] In the embodiment of the present disclosure, the lengths of the input plaintext data and the output ciphertext data are both 128 bits, with (X 0 ,X 1 ,X 2 ,X 3 ) represents the input plaintext data, with (Y 0 ,Y 1 ,Y 2 ,Y 3 ) represents the output ciphertext data, and the decryption round key RK is obtained in each round of key expansion i , after i=31,...,1,0, the input plaintext data can be encrypted and transformed according to formula (4) and formula (5) to obtain ciphertext data:
[0061] x i+4 =X i ⊕T(X i+1 ⊕X i+2 ⊕X i+3 ⊕RK i ) (4)
[0062] (Y 0 ,Y 1 ,Y 2 ,Y 3 )=R(X 32 ,X 33 ,X 34 ,X 35 )=(X 35 ,X 34 ,X 33 ,X 32 ) (5)
[0063] Among them, T represents the synthetic permutation operation, its input and output are both 32 bits, and it is formed by the coincidence of nonlinear transformation τ and linear transformation L, that is, T(·)=L(τ(·)); R represents the reverse sequence transform...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More