Identity authentication method of heterogeneous blockchain in cross-chain scenario
A technology of identity authentication and blockchain, applied in the usage of multiple keys/algorithms, public keys for secure communication, digital transmission systems, etc., to achieve the effect of improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] The present invention will be further described below in conjunction with the accompanying drawings.
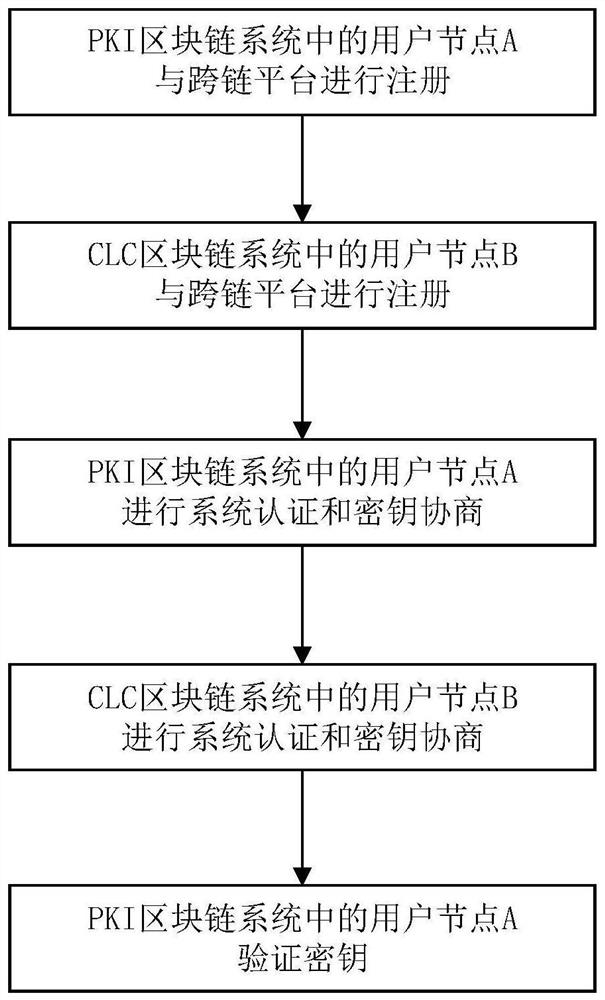
[0044] Refer to attached figure 1 , to further describe the specific steps of the present invention.
[0045] Step 1. User node A in the PKI blockchain system registers with the cross-chain platform.
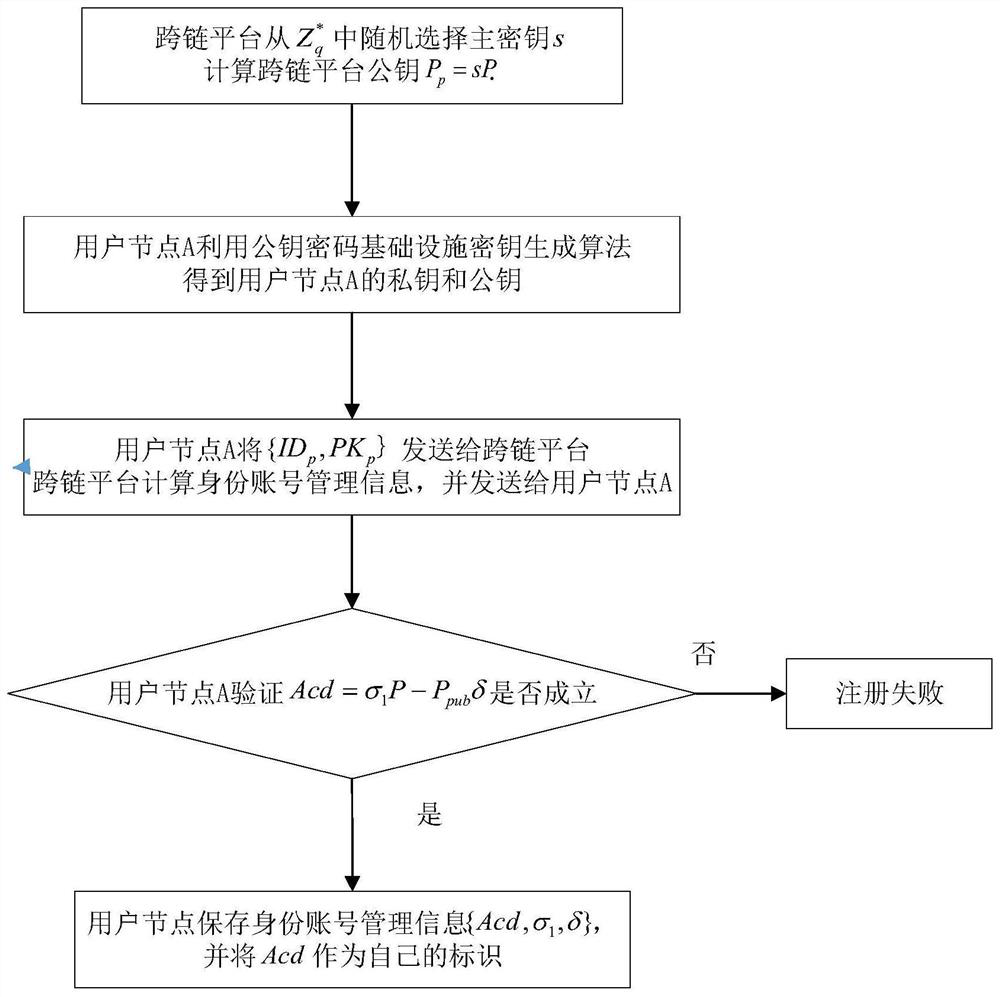
[0046] Refer to attached figure 2 , to further describe step 1 of the present invention.
[0047] Cross-chain platform from Randomly select the master key s, and calculate the cross-chain platform public key P p =sP, where P represents the additive cyclic group G 1 A generator in , Denotes a finite field Z q = {0,1,...,q-1} The set after removing element zero.
[0048] The PKI blockchain system selects user node A, and uses the public key cryptography infrastructure key generation algorithm to obtain the private key x of user node A p and public key PK p ;
[0049] The steps of the public key cryptography infrastructure key generation algorithm are as follo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More