Privacy protection method in edge computing environment
An edge computing and privacy protection technology, applied in the field of privacy protection, can solve problems such as a large amount of communication load and decoding complexity, and achieve the effect of reducing decoding complexity, computing delay, and communication load.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
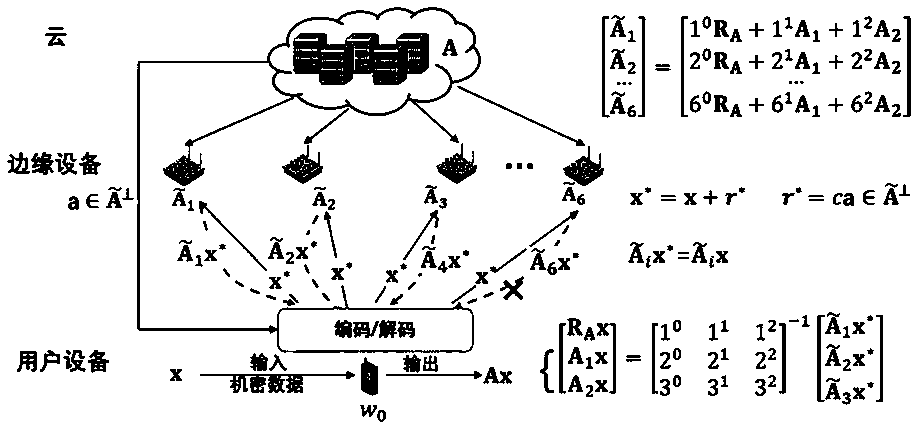
[0039] Embodiment: Provide a computing framework for secure coding edge computing based on orthogonal vectors. On the basis of ensuring data privacy and completing computing tasks, the method reduces communication load and user input by specially designing a coding scheme for user-side input data. The complexity of device decoding.
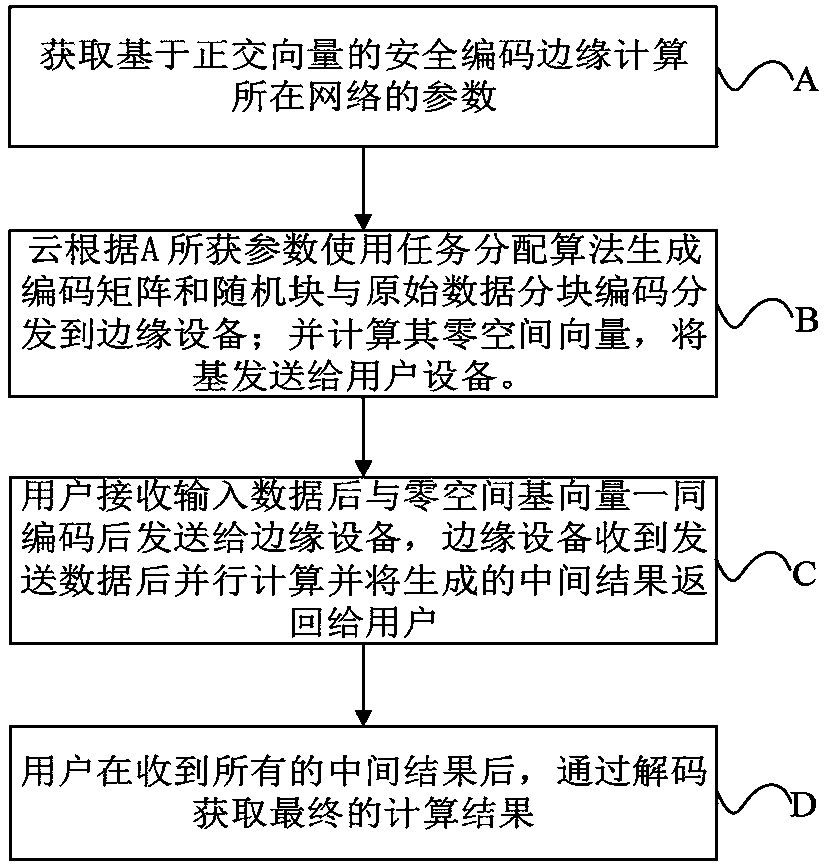
[0040] see figure 1 Shown is the flow chart of constructing edge computing based on secure coding.
[0041] Specific methods include:
[0042] A: Obtain the parameters of the network where the secure coding-based edge computing is located,
[0043] The parameters include:
[0044] A1: Edge device set W={w 1 ,w2 ,…,w p};
[0045] A2; Number of edge devices p ;
[0046] A3: Computing Task Scale m , n ;
[0047] A4: The number of partitions of the data matrix k ;
[0048] A5: Data Matrix Block A ;
[0049] A6: Input vector x ;
[0050] A7: User's computing tasks A x;
[0051] A8: Safety adjustment parameters s ;
[0052] A9: fi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More