Single decoy state quantum digital signature method
A decoy state quantum and digital signature technology, applied in digital transmission systems, secure communication devices, electromagnetic wave transmission systems, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
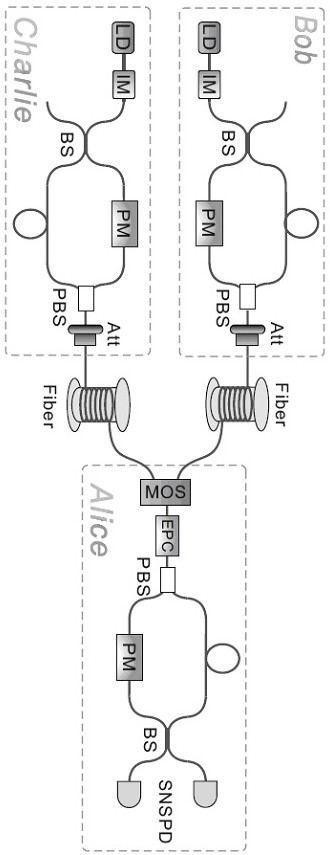
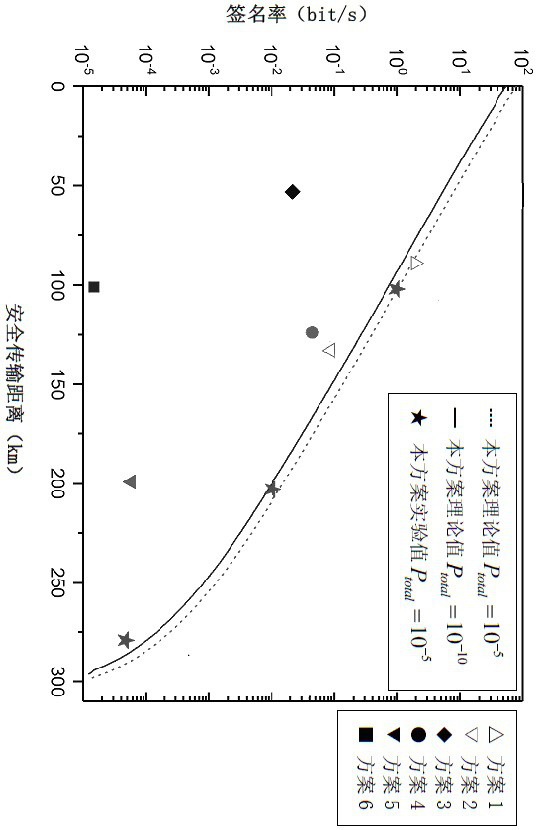
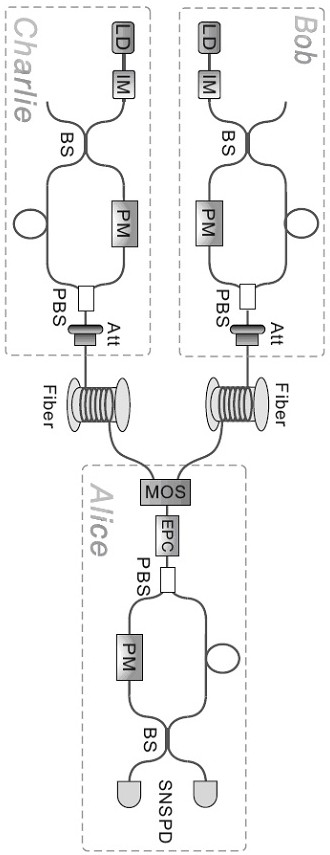
[0014] In order to deepen the understanding of the present invention, the present invention will be further described below in conjunction with the examples, which are only used to explain the present invention, and do not constitute a limitation to the protection scope of the present invention. like Figure 1-2 As shown, the present embodiment provides a single decoy state quantum digital signature method, the method includes three participants: a signer Alice and two signature accepting objects Bob and Charlie, the method includes two stages: distribution phase and message phase, the specific methods are as follows:
[0015] In the distribution phase, the key generation protocol is executed by Bob-Alice and Charlie-Alice respectively to generate key strings; for the information m∈{0,1} that needs to be signed, Bob or Charlie randomly selects a bit b∈{0, 1}, base Intensity λ∈{μ,ν} to prepare N t quantum states and send them to Alice; Alice randomly chooses the basis To ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More