Website security detection system and method based on full flow
A security detection, full flow technology
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0041]The present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments. Note that the aspects described below in conjunction with the drawings and specific embodiments are only exemplary, and should not be construed as limiting the protection scope of the present invention.
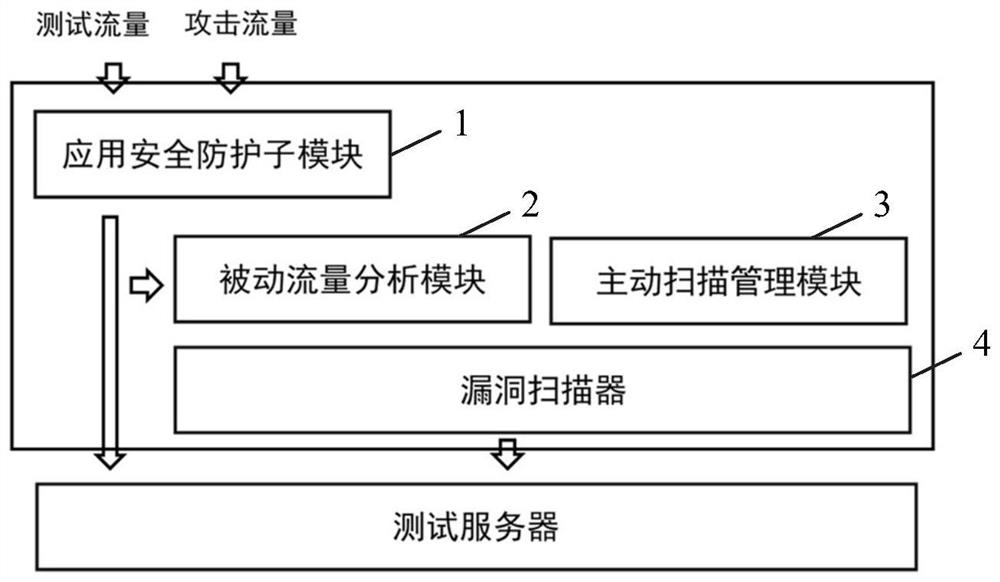
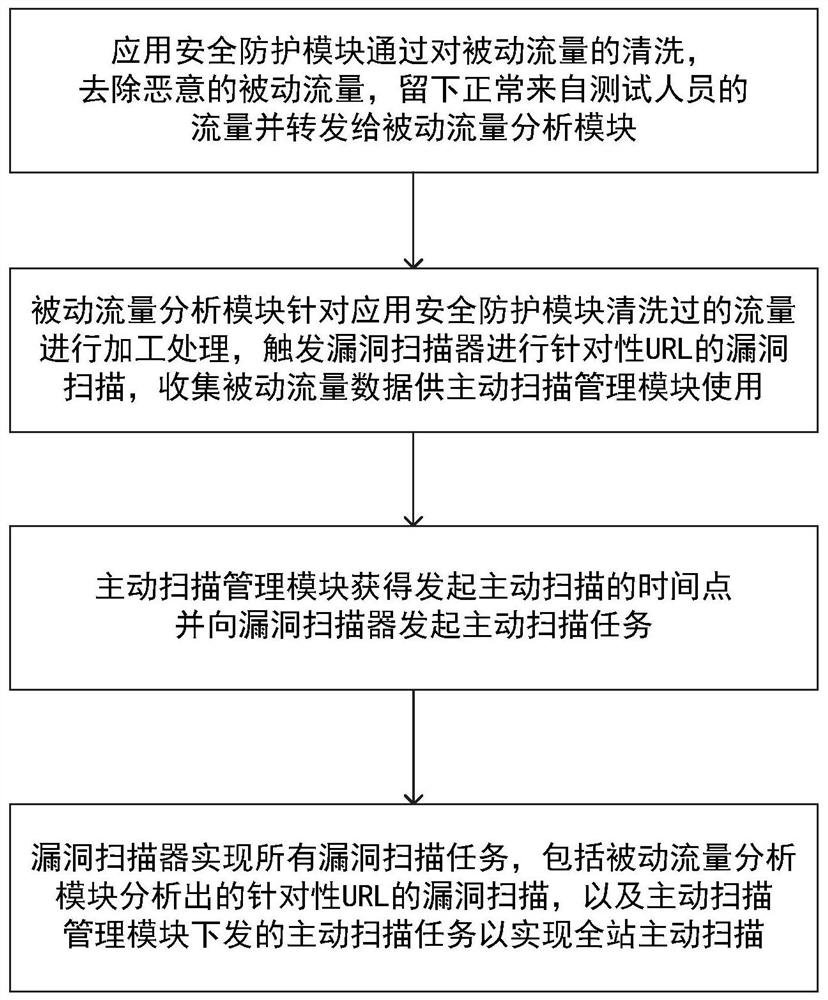
[0042] figure 1 The principle of an embodiment of the website security detection system based on full flow of the present invention is shown. See figure 1 , the website security detection system based on full traffic in this embodiment includes: an application security protection module 1 , a passive traffic analysis module 2 , an active scanning management module 3 , and a vulnerability scanner 4 .
[0043] The data transmission relationship between these four modules is: application security protection module 1 receives external test traffic and attack traffic, application security protection module 1 transmits data to passive traffic analy...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More