Kernel code pointer integrity protection method based on ARM pointer verification
An integrity protection and pointer technology, applied in program/content distribution protection, digital data protection, instruments, etc., can solve problems such as the inability to automatically identify data pointers, and achieve the effect of reducing performance overhead and saving time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] In order to make the purpose, technical solution and advantages of the present application clearer, the technical solution of the present application will be clearly and completely described below in conjunction with specific embodiments of the present application and corresponding drawings. Apparently, the described embodiments are only some of the embodiments of the present application, rather than all the embodiments. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
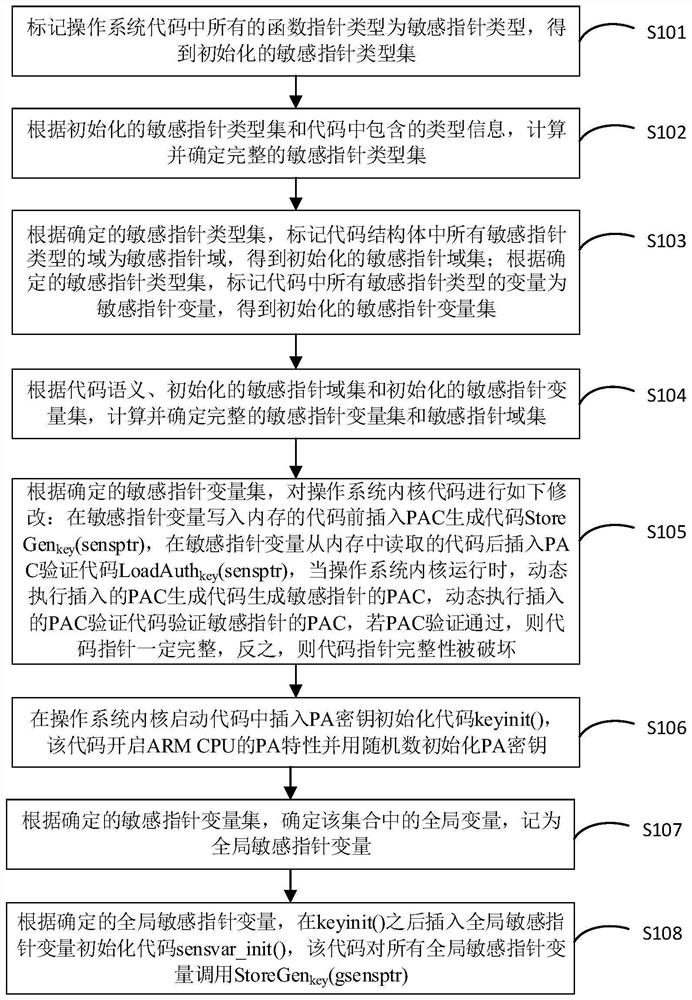
[0032] figure 1 A flowchart of a method for protecting the integrity of a kernel code pointer based on ARM pointer verification provided by an embodiment of the present invention; a method for protecting the integrity of a kernel code pointer based on ARM pointer verification provided in this embodiment uses a pointer verification code to All sensiti...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More