Information processing method, terminal equipment, server and storage medium
An information processing method and terminal equipment technology, applied in the field of wireless communication, can solve the problems of leakage of user location privacy, lack of discovery and protection of correlations between location data, information leakage, etc., so as to avoid being excavated, enhance security, and guarantee credibility effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
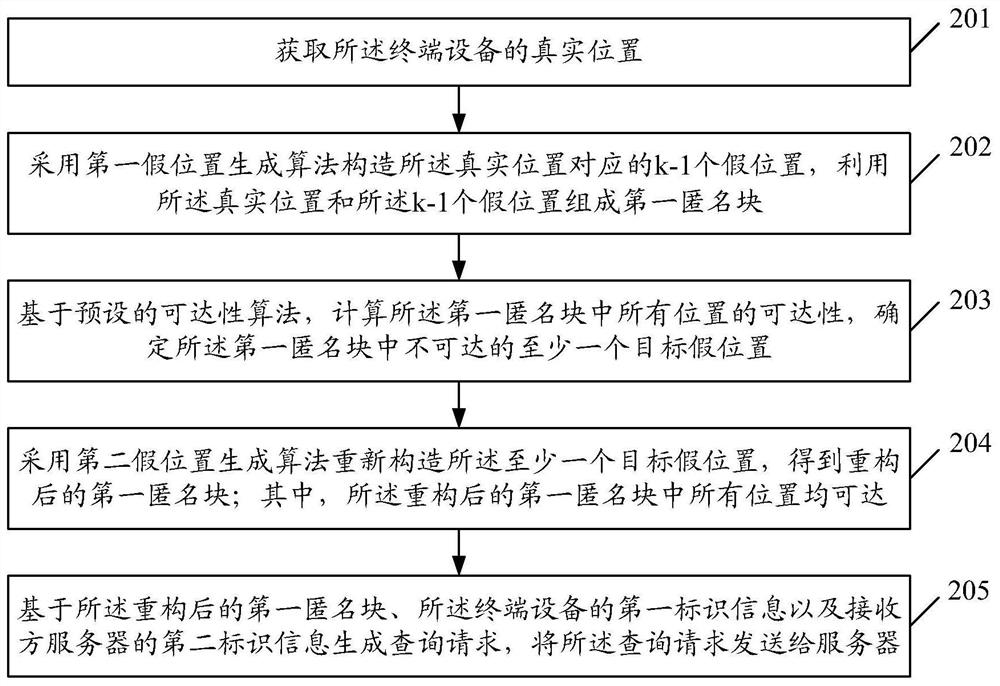
[0059] An embodiment of the present application provides an information processing method, which is applied to a terminal device, figure 2 It is a schematic diagram of the first flow structure of the information processing method in the embodiment of the present application, such as figure 2 As shown, the method may specifically include:
[0060] Step 201: Obtain the real location of the terminal device;
[0061] Step 202: Use the first fake location generation algorithm to construct k-1 fake locations corresponding to the real location, and use the real location and the k-1 fake locations to form a first anonymous block; where k is greater than 1 an integer of
[0062] Step 203: Calculate the reachability of all locations in the first anonymous block based on a preset reachability algorithm, and determine at least one unreachable target false location in the first anonymous block;
[0063] Step 204: Reconstruct the at least one target false location by using the second f...
Embodiment 2
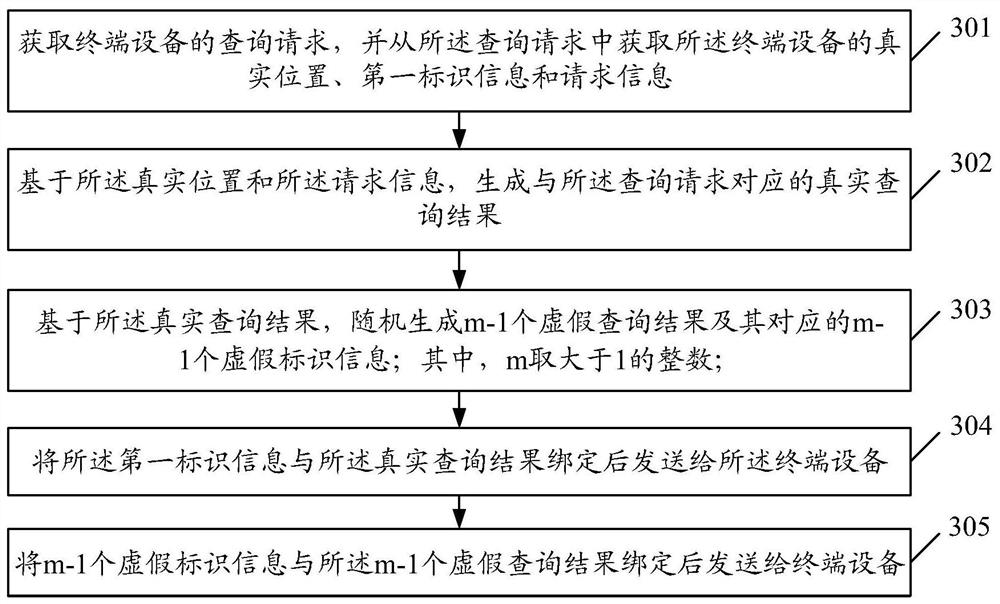
[0098] An embodiment of the present application provides an information processing method applied to a server, image 3 It is a schematic diagram of the second process flow structure of the information processing method in the embodiment of the present application, such as image 3 As shown, the method may specifically include:
[0099] Step 301: Obtain a query request of a terminal device; wherein, the query request includes at least the real location of the terminal device, first identification information and request content;
[0100] Step 302: Based on the real location and the request content, generate a real query result corresponding to the query request;
[0101] Step 303: Based on the real query results, randomly generate m-1 false query results and corresponding m-1 false identification information; wherein, m is an integer greater than 1;
[0102] Step 304: Bind the first identification information with the real query result and send it to the terminal device;
...
Embodiment 3
[0144] The embodiment of the present application also provides a terminal device, such as Figure 5 As shown, the equipment includes:
[0145] An acquiring unit 501, configured to acquire the real location of the terminal device;
[0146] An anonymous construction unit 502, configured to construct k-1 false positions corresponding to the real position using a first false position generation algorithm, and use the real position and the k-1 false positions to form a first anonymous block; wherein, k takes an integer greater than 1;
[0147] The processing unit 503 is configured to calculate the reachability of all locations in the first anonymous block based on a preset reachability algorithm, and determine at least one unreachable target false location in the first anonymous block;
[0148] The anonymous construction unit 502 is further configured to reconstruct the at least one target false position using a second false position generation algorithm to obtain a reconstructed...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More